20-Year-Old Vulnerability Allows Hackers to Control Train Brakes
A 20-Year Legacy of Risk: Unpacking the Critical Train Brake Vulnerability
Imagine a scenario where the safety of millions hinges on a digital thread, a vulnerability lurking for two decades, finally exposed. This isn’t a plot from a thriller; it’s the stark reality revealed by a recent critical advisory from the Cybersecurity and Infrastructure Security Agency (CISA). A severe vulnerability, now identified as CVE-2025-1727, has come to light within the very communication systems that control our nation’s trains, potentially allowing unauthorized actors to remotely manipulate train brakes. Understanding the implications of this long-standing flaw is paramount for safeguarding our transportation infrastructure.
The Heart of the Problem: End-of-Train/Head-of-Train Protocols
The vulnerability primarily targets a crucial component of railway operations: the End-of-Train (EOT) and Head-of-Train (HOT) remote linking protocols. These protocols are the digital connective tissue, enabling safe communication and control between the locomotive (head of train) and the caboose or remote braking unit (end of train). For approximately twenty years, these systems have been operating with an unseen, unaddressed flaw. The CISA warning underscores the pervasive nature of this issue, affecting transportation infrastructure across the United States. The vulnerability’s substantial CVSS v4 score of 7.2 highlights its significant potential impact.
Understanding CVE-2025-1727
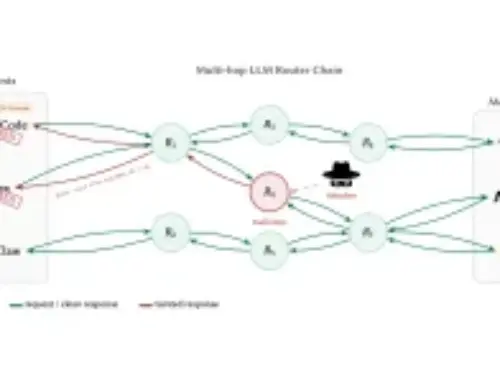
CVE-2025-1727 represents a critical weakness in the communication architecture of railway systems. While specifics of the exploit chain are often withheld for security reasons, the core mechanism involves bypassing or manipulating the signals that govern train braking. Such a capability in the wrong hands could lead to catastrophic outcomes, ranging from deliberate derailments to significant operational disruptions and, most concerningly, severe injury or loss of life.
The Broader Implications for Critical Infrastructure
This discovery serves as a potent reminder of the inherent risks embedded within aging critical infrastructure systems. Many of these systems were designed and implemented before the rise of modern cybersecurity threats, often prioritizing functionality and reliability over robust digital security. The interconnectedness of today’s systems means that a vulnerability in one area can have cascading effects across an entire network. For railway systems, this vulnerability could be exploited not just for direct control, but also potentially for intelligence gathering, reconnaissance, or as a stepping stone for further network penetration.
Remediation Actions for Railway Operators
Addressing CVE-2025-1727 requires immediate and decisive action from railway operators and infrastructure owners. Here are critical steps to mitigate the risk:
- Vulnerability Assessment and Patching: Prioritize identifying all affected EOT/HOT systems and apply any patches or firmware updates issued by vendors. Establish a rigorous patch management process.
- Network Segmentation: Implement strict network segmentation to isolate operational technology (OT) networks from IT networks. This limits the lateral movement of attackers if one segment is compromised.
- Access Control and Authentication: Enforce strong authentication mechanisms for all access points to critical railway systems, including multi-factor authentication (MFA) where feasible. Regularly review and revoke unnecessary privileges.
- Intrusion Detection Systems (IDS): Deploy and configure IDS/IPS solutions to monitor network traffic for anomalous behavior or indicators of compromise within the railway communication protocols.
- Incident Response Plan: Develop and regularly test a comprehensive incident response plan specifically for OT environments. This plan should detail procedures for detection, containment, eradication, and recovery from a cyber-attack.
- Vendor Collaboration: Maintain close communication with EOT/HOT system vendors to stay informed about new vulnerabilities, patches, and security best practices.
Essential Tools for Detection and Mitigation
Effective management of such vulnerabilities often relies on specialized tools. Below are categories of tools relevant for assessing and securing railway critical infrastructure environments:
| Tool Name/Category | Purpose | Link (Example) |
|---|---|---|
| Network Intrusion Detection/Prevention Systems (IDS/IPS) | Monitors network traffic for malicious activity and known attack signatures related to industrial protocols. | Snort / Suricata |
| Vulnerability Scanners (OT-specific) | Identifies known vulnerabilities in industrial control systems (ICS) and OT components. | Claroty / Tenable.ot |
| Security Information and Event Management (SIEM) | Aggregates security logs and events from various sources for centralized monitoring and analysis. | Splunk / ELK Stack (Elastic SIEM) |
| Packet Analyzers | Captures and analyzes network packets to understand communication flows and identify anomalies. | Wireshark |
Conclusion: The Urgency of Industrial Cybersecurity
The revelation of CVE-2025-1727 underscores a critical truth: the digital vulnerabilities of yesterday can become the existential threats of today. For railway systems, where safety is paramount, securing these long-standing operational technologies is not merely a best practice but an absolute necessity. Protecting our critical transportation infrastructure demands persistent vigilance, proactive mitigation, and a commitment to modern cybersecurity principles in concert with operational reliability.