Want To Detect Incidents Before It’s Too Late? You Need Threat Intelligence
Want To Detect Incidents Before It’s Too Late? You Need Threat Intelligence
The difference between a minor security incident and a devastating breach often comes down to one critical factor: how quickly you can detect and respond to a cyber threat. Organizations that consistently fall victim to costly data breaches or operational disruptions frequently lack the proactive intelligence required to anticipate and counter sophisticated attacks. This isn’t just about patching known vulnerabilities; it’s about understanding the evolving adversary landscape.
The Critical Role of Early Incident Detection
In cybersecurity, time is a critical differentiator. The longer a malicious actor resides undetected within your network, the greater the potential for data exfiltration, system compromise, and reputational damage. Early incident detection is not merely a reactive measure; it’s a strategic imperative that minimizes dwell time and reduces the blast radius of an attack. Without robust detection capabilities, a minor infiltration can quickly escalate into a full-scale crisis.
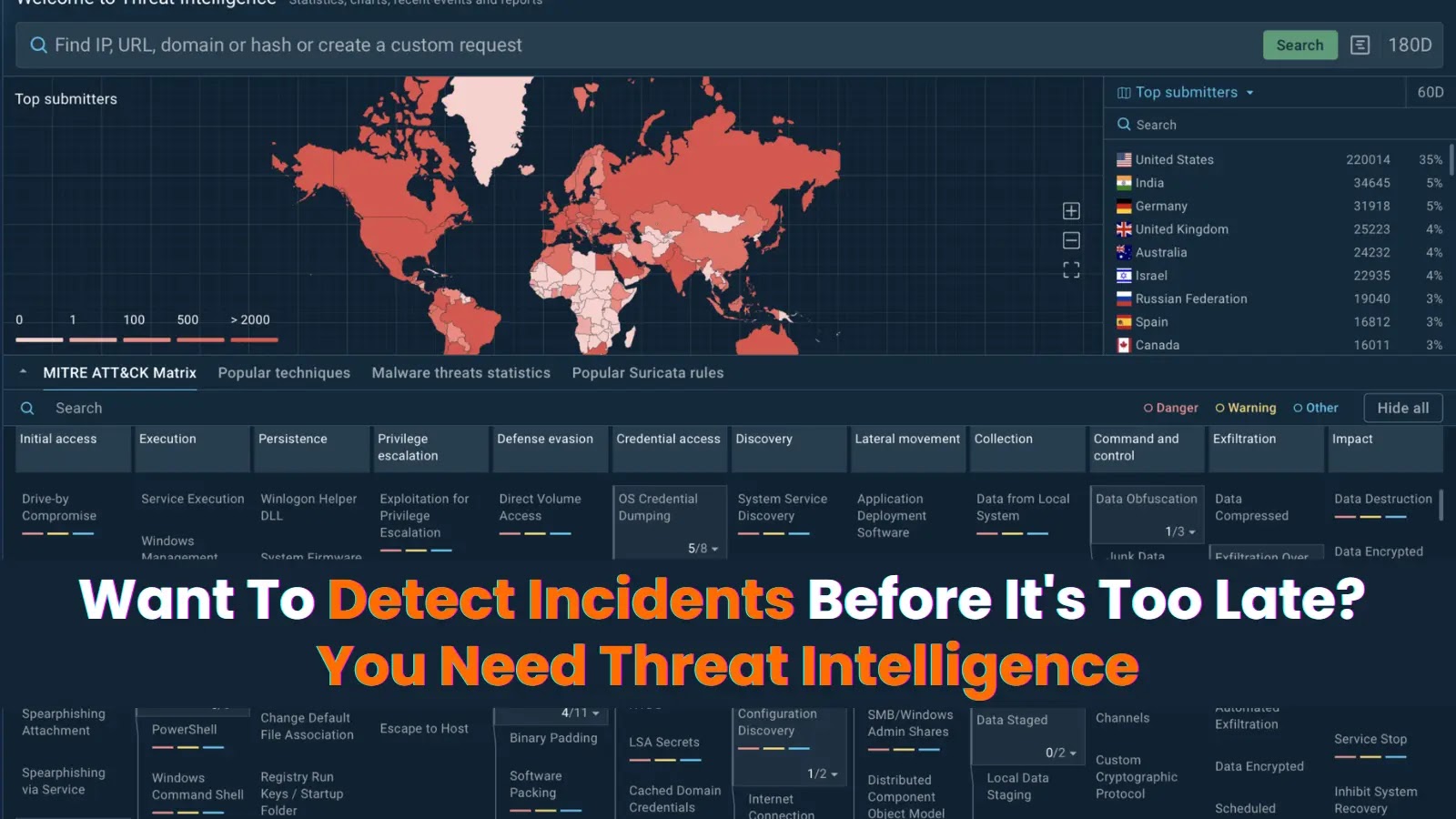
Understanding Adversary Tactics, Techniques, and Procedures (TTPs)
Hackers rarely target an isolated business. They typically launch campaigns that hit multiple companies with similar tactics, techniques, and procedures (TTPs). This means, by the time an organization experiences a novel attack, a similar methodology might have already been observed elsewhere. Leveraging this collective intelligence – specifically, understanding the TTPs employed by threat actors – enables organizations to shift from a reactive posture to a proactive defense. Threat intelligence provides insights into malware variants, exploit kits, phishing campaigns, and even the infrastructure used by adversaries.
What is Threat Intelligence?
Threat intelligence refers to aggregated, refined, and analyzed information about existing or emerging threats that can be used to understand the motivations, capabilities, and intentions of malicious actors. It’s not just raw data; it’s contextualized, actionable insights that help security teams make informed decisions. This includes everything from real-time indicators of compromise (IOCs) like malicious IP addresses and file hashes to strategic analyses of geopolitical cyber warfare trends.
Actionable Insights from Threat Intelligence
Implementing a robust threat intelligence program transforms raw data into actionable insights for your security operations center (SOC). Here’s how:
- Proactive Defense: By understanding the latest TTPs, organizations can proactively strengthen their defenses, anticipating attacks before they materialize. This might involve updating firewall rules, configuring intrusion detection systems, or patching specific vulnerabilities.
- Enhanced Detection: Threat intelligence feeds security information and event management (SIEM) systems with IOCs, enabling quicker identification of malicious activity. For example, if a specific malware variant associated with CVE-2023-45678 (see CVE-2023-45678) is trending, your SIEM can be configured to alert on its specific behavioral patterns.
- Faster Response: When an incident occurs, threat intelligence provides crucial context. Knowing the likely actor or their common methodologies can streamline incident response, allowing teams to quickly identify the root cause and contain the breach.
- Vulnerability Management Prioritization: Not all vulnerabilities are equally critical. Threat intelligence helps prioritize patching efforts by highlighting vulnerabilities actively being exploited in the wild, or those associated with specific, high-impact threat groups. For instance, exploits related to CVE-2024-12345 (CVE-2024-12345) might demand immediate attention if threat actors are actively leveraging them.
- Strategic Planning: Higher-level threat intelligence informs executive decisions, budget allocations, and long-term cybersecurity strategy by providing an understanding of the evolving threat landscape and potential future risks.
Remediation Actions and Best Practices for Implementing Threat Intelligence
Integrating threat intelligence into your security program requires more than just subscribing to a feed. Here are key remediation actions and best practices:
- Integrate with Existing Security Tools: Feed threat intelligence into your SIEM, endpoint detection and response (EDR), firewalls, and intrusion prevention systems (IPS) for automated alerting and blocking.
- Automate IOC Ingestion: Leverage SOAR (Security Orchestration, Automation, and Response) platforms to automatically ingest and action IOCs from multiple threat intelligence sources, reducing manual effort and improving response times.
- Develop Use Cases: Define specific use cases for your threat intelligence. For example, “Detect phishing attempts targeting C-level executives” or “Identify lateral movement associated with Ransomware-as-a-Service (RaaS) groups.”
- Regularly Update Intelligence Feeds: The threat landscape is dynamic. Ensure your intelligence feeds are current and diverse, pulling from open-source intelligence (OSINT), commercial vendors, and industry-specific sharing groups.
- Train Your Security Team: Ensure your security analysts understand how to interpret and act upon threat intelligence. Provide training on threat hunting techniques using intelligence indicators.
- Attribution and Context: Don’t just focus on the “what,” but also the “who” and “why.” Understanding actor attribution and motivation provides invaluable context for a more strategic defense.
- Establish a Threat Intelligence Platform (TIP): For larger organizations, a TIP can centralize, normalize, and manage disparate threat intelligence feeds, providing a single pane of glass for analysis.
Conclusion
In a world where cyber threats constantly evolve, passive security measures are no longer sufficient. Threat intelligence is no longer a luxury but a fundamental component of a mature cybersecurity posture. By understanding adversary TTPs, proactively detecting emerging threats, and contextualizing security incidents, organizations can significantly reduce their risk exposure and ensure that a minor anomaly doesn’t escalate into a catastrophic breach. Invest in threat intelligence; it’s the cornerstone of effective, anticipatory cybersecurity.