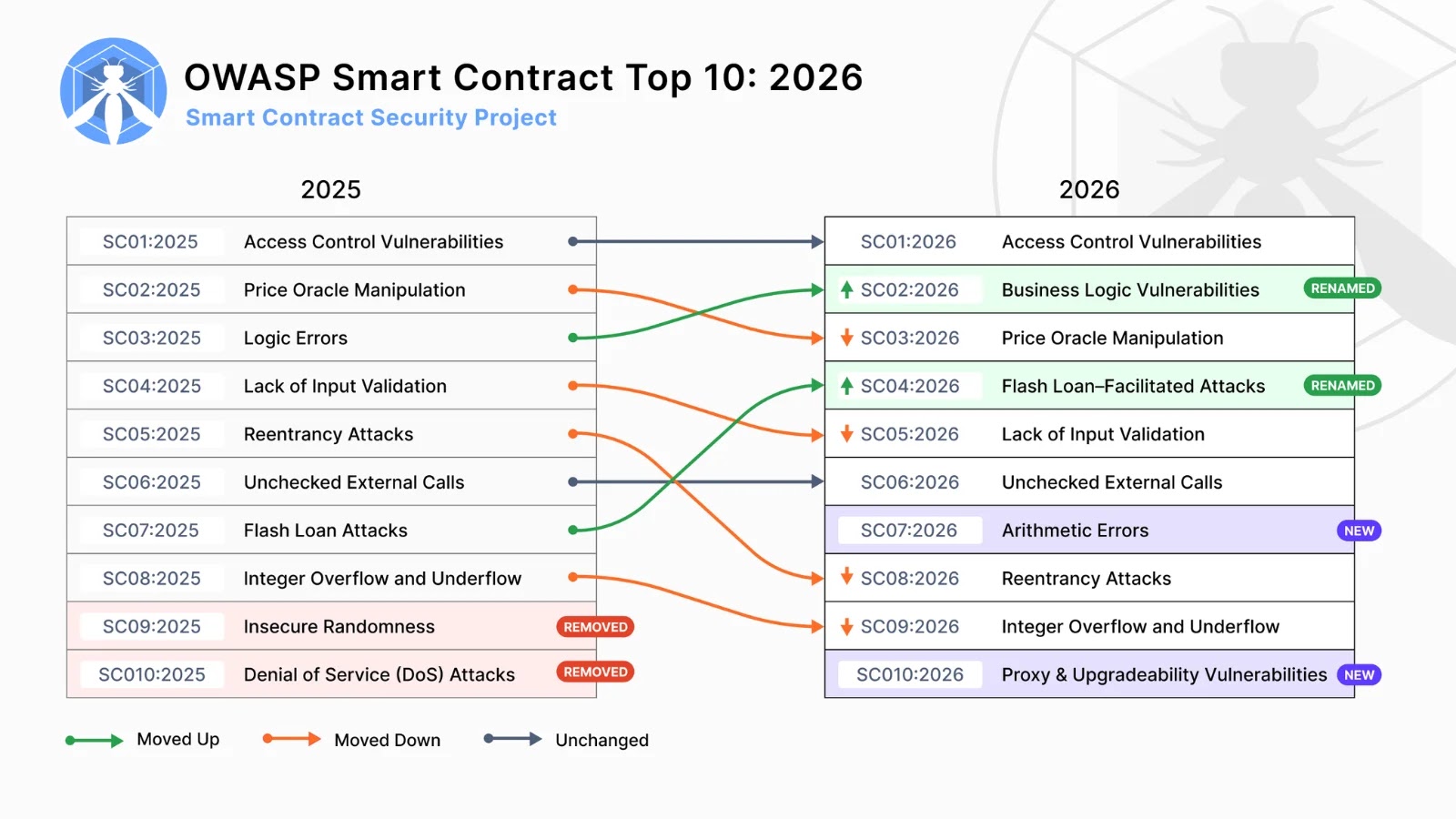
OWASP Smart Contract Top 10 2026 — Security Risks and Vulnerabilities
Smart contracts, the self-executing agreements encoded on blockchain technology, are the backbone of Web3 innovation. As their adoption accelerates, so too does the need for robust security. The Open Web Application Security Project (OWASP), a globally recognized non-profit dedicated to improving software security, has once again stepped up. Their release of the OWASP Smart Contract Top 10: 2026 provides a critical roadmap for developers, auditors, and protocol owners navigating the complex landscape of smart contract vulnerabilities. This forward-looking standard awareness document, a sub-project of the broader OWASP Smart Contract Security (OWASP SCS) initiative, highlights the most pressing security risks impacting decentralized applications today.
Understanding the OWASP Smart Contract Top 10: 2026
The OWASP Smart Contract Top 10: 2026 isn’t just a list; it’s a strategic resource categorizing the most prevalent and impactful security weaknesses in smart contracts. Its purpose is to guide stakeholders in prioritizing their security efforts, from secure coding practices during development to comprehensive auditing and post-deployment monitoring. By focusing on these top threats, the Web3 ecosystem can collectively enhance its resilience against sophisticated attacks.
Key Vulnerabilities and Remediation Strategies
Unchecked External Call
This vulnerability arises when a smart contract interacts with an external contract without proper validation of its return values or state changes. An attacker could exploit this to trigger unexpected behavior or drain funds if the external call fails silently or returns an unexpected value. This is particularly dangerous in scenarios where contract execution depends on the successful completion of an external function. For example, a token transfer failing and the originating contract not handling the error could lead to an inconsistent state.
Remediation Actions
- Input Validation: Always validate the return values of external calls. Even if the call is expected to succeed, explicit checks for success and failure are crucial.
- Reentrancy Guards: Implement reentrancy guards to prevent malicious contracts from repeatedly calling back into your contract before the first execution is complete. Consider using the OpenZeppelin
ReentrancyGuard. - Circuit Breakers: Incorporate mechanisms to pause or halt critical contract functions in the event of suspicious activity or unexpected external call failures.
- Time-Lock Mechanisms: For sensitive operations involving external calls, introduce time locks to allow for manual intervention if an issue is detected.
Reentrancy
Reentrancy is a well-known and often catastrophic vulnerability, famously exploited in the DAO hack (though not assigned a specific CVE, its impact is undeniable for CVE-2016-10115 and subsequent related issues). It occurs when an external call allows the external contract to call back into the original contract before the first transaction has completed, potentially leading to repeated withdrawals or state manipulation. Think of it as leaving a door unlocked during a sensitive operation, allowing someone to re-enter and take advantage of an incomplete process.
Remediation Actions
- Checks-Effects-Interactions Pattern: The most fundamental defense. Perform all checks, then apply all state changes, and only then interact with external contracts. This ensures the contract’s state is updated before external calls can be made.
- Use
transfer()orsend()for Ether: These functions have a gas limit of 2300, which is generally insufficient for a reentrant call, effectively preventing reentrancy for simple Ether transfers. However, note that these functions are deprecated for contracts that receive Ether. - Reentrancy Locks: Implement mutex-like locks within your contract using a boolean flag. Set the flag to
truebefore an external call andfalseafter, reverting if the flag is alreadytrue. OpenZeppelin’sReentrancyGuardcontract provides an excellent, battle-tested implementation. - Avoid External Calls in Loops: Minimize or avoid altogether external calls within loops, as this significantly increases the reentrancy attack surface.
Access Control Vulnerabilities
Improper access controls are a fundamental security flaw that can plague any software, and smart contracts are no exception. This category encompasses issues where unauthorized users can execute privileged functions, alter critical data, or bypass intended restrictions. Examples include missing onlyOwner modifiers, incorrect role-based access control (RBAC) implementations, or functions that everyone can call but should be reserved for specific entities.
Remediation Actions
- Implement Role-Based Access Control (RBAC): Define clear roles (e.g., owner, admin, minter) and assign specific permissions to each role. Use modifiers like
onlyOwneror custom role checks for restricted functions. - Use OpenZeppelin’s AccessControl: Leverage audited and robust access control contracts from OpenZeppelin to manage roles centrally and securely.
- Principle of Least Privilege: Grant only the necessary permissions to each address or role. Avoid giving broad administrative rights unless absolutely essential.
- Thorough Testing: Conduct extensive testing of all access control mechanisms to ensure they operate as intended under various scenarios.
Insufficient Cryptographic Security
Smart contracts often rely on cryptographic primitives for operations like randomness generation, signature verification, or secure data storage. Insufficient cryptographic security arises when weak algorithms are used, implementations are flawed, or inputs to cryptographic functions are predictable. This can lead to predictable outcomes, forged signatures, or compromised confidentiality. An example could be using block.timestamp or block.difficulty for generating random numbers, as these are easily manipulable by miners, as detailed in several whitepapers (e.g., related to CVE-2017-15707 for similar but off-chain issues).
Remediation Actions
- Use Secure Randomness Oracles: For true randomness, integrate with secure, decentralized randomness oracles like Chainlink VRF (Verifiable Random Function).
- Avoid Predictable On-Chain Data: Never use
block.timestamp,block.number,block.difficulty, or other easily forgeable on-chain data for security-critical decisions, especially randomness. - Validate Signature Inputs: When verifying signatures, ensure that the message signed and the signer’s address are correctly extracted and validated.
- Audit Cryptographic Implementations: Engage security experts to audit any custom cryptographic implementations to identify weaknesses.
Front-Running and Sandwich Attacks
Front-running occurs when an attacker observes a pending legitimate transaction in the mempool and submits their own transaction with a higher gas price, causing their transaction to be processed first. This allows them to profit from manipulating prices or stealing opportunities. A sandwich attack is a specific form where the attacker places their trade both before and after the victim’s trade, buying low and selling high at the victim’s expense.
Remediation Actions
- Commit-Reveal Schemes: For interactions where the order matters (e.g., sealed bids), use a commit-reveal scheme where users first commit a hash of their action and later reveal the action itself after a certain block height.
- Decentralized Exchanges (DEXs) with MEV Protection: Utilize DEXs that offer Maximal Extracting Value (MEV) protection mechanisms, such as private transaction relays or batch auctions.
- Off-Chain Computation with On-Chain Settlement: Move sensitive computations off-chain to prevent attackers from observing and reacting to pending transactions.
- Auction Mechanisms: Design auction mechanisms carefully to mitigate front-running, possibly using schemes where final prices are settled at the end of a block rather than individually.
Tools for Smart Contract Security
Leveraging the right tools is paramount in identifying and mitigating smart contract vulnerabilities. Here’s a table of essential tools:
| Tool Name | Purpose | Link |
|---|---|---|
| Mythril | Static analysis for Solidity bytecode (EVM). Detects common vulnerabilities like reentrancy, integer overflows, and unchecked external calls. | https://mythx.io/ |
| Slither | Static analyzer for Solidity. Detects vulnerabilities, provides quality reports, and visualizes inheritance graphs and call graphs. | https://github.com/crytic/slither |
| Truffle Security | Part of the Truffle Suite, it offers basic security analysis and integration with external tools during the development lifecycle. | https://trufflesuite.com/docs/truffle/security/ |
| Diligence Fuzzing (e.g., from Concensys) | Fuzz testing tool designed to find subtle vulnerabilities by feeding unexpected inputs to contracts. | https://diligence.consensys.net/fuzzing/ |
| Echidna | Fuzzing tool for Ethereum smart contracts written in Solidity. Focuses on finding assertion failures and unexpected behavior. | https://github.com/crytic/echidna |
| OpenZeppelin Contracts | A library of secure, community-vetted, and audited smart contracts for common functionalities (e.g., access control, ERC-20, ERC-721). Using these reduces vulnerability surface. | https://docs.openzeppelin.com/contracts/5.x/ |
The Path Forward: Continuous Security and Education
The OWASP Smart Contract Top 10: 2026 serves as a definitive guide for securing decentralized applications. Its emphasis on proactive identification and mitigation of critical vulnerabilities underscores the dynamic nature of Web3 security. Developers must adopt secure coding practices, implement robust testing frameworks, and leverage specialized security tools. Regular security audits by independent experts remain indispensable, complementing in-house efforts. For protocol owners and auditors, understanding these top risks facilitates more effective threat modeling and vulnerability assessments. Continuous education and adherence to evolving best practices are not optional but essential for building a resilient and trustworthy Web3 ecosystem.