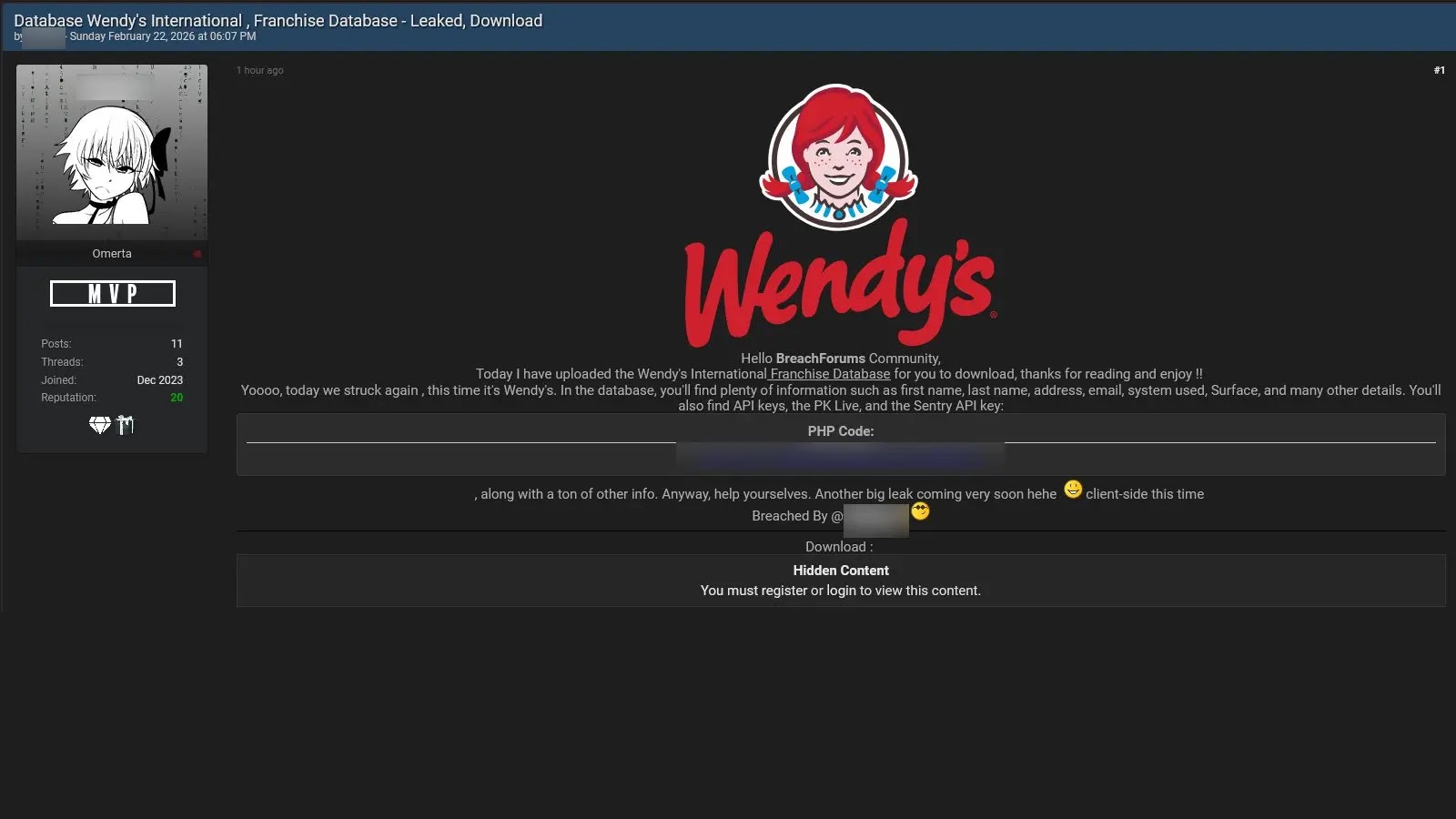
Threat Actor Allegedly Claimed Leak of Wendy’s International Franchise Database
A disturbing claim has surfaced in the cybersecurity landscape, sending ripples through the financial and operational structures of a global fast-food giant. On February 22, 2026, a threat actor alleged to have breached and subsequently leaked significant portions of what they termed the “Wendy’s International Franchise Database.” This alleged data exposure reportedly encompasses highly sensitive information, including critical operational configurations, detailed franchisee contact data, and crucial live payment integration credentials across multiple food service brands operating under the Wendy’s umbrella.
The implications of such a breach are profound, extending far beyond typical customer data leaks. For IT professionals, security analysts, and developers observing this incident, understanding the potential attack vectors and downstream consequences is paramount. This alleged incident underscores the persistent and evolving threats targeting complex franchise models and supply chains.
Understanding the Alleged Wendy’s Database Leak
The core of this incident revolves around a claim made by an unidentified threat actor regarding a breach of Wendy’s international franchise operations. According to the source, the leaked data includes a trifecta of highly sensitive categories:
- Sensitive Operational Configurations: This could range from backend system access details to internal network topology, potentially offering nefarious actors blueprints for further infiltration or disruption.
- Franchisee Contact Data: Personally identifiable information (PII) for franchisees, which could be exploited for targeted phishing attacks, social engineering campaigns, or even identity theft.
- Live Payment Integration Credentials: Arguably the most critical revelation, these credentials could enable unauthorized access to payment gateways, leading to financial fraud, service disruption, and massive reputational damage. The compromise of such credentials impacts direct financial transactions and the trust consumers place in the brand’s payment processing security.
The alleged leak’s impact is magnified by the multi-brand scope explicitly mentioned, suggesting a potential vulnerability that extends across an entire ecosystem of food service operations connected to Wendy’s international franchise model.
Ramifications of Compromised Payment Integration Credentials
The exposure of live payment integration credentials represents a severe security incident. Such data typically includes API keys, secret tokens, or other authentication mechanisms necessary to process transactions securely. If these are indeed compromised, the potential consequences are dire:
- Direct Financial Theft: Threat actors could use these credentials to reroute transactions, initiate fraudulent payments, or access funds directly.
- PCI DSS Compliance Violations: Companies handling payment card data are subject to the Payment Card Industry Data Security Standard (PCI DSS). A breach of this nature almost certainly indicates a severe violation, leading to hefty fines and loss of processing privileges.
- Service Disruption: Threat actors might disrupt payment services, causing operational paralysis for franchisees and significant financial losses.
- Reputational Damage: Consumer trust is fragile. Any compromise of payment systems can quickly erode customer confidence, leading to a long-term negative impact on brand loyalty and sales.
The Silence from Wendy’s: What It Means
At the time of this report, neither Wendy’s US nor Wendy’s UK has publicly acknowledged the alleged breach. This silence, while not uncommon in the immediate aftermath of such claims, leaves a critical void:
- Uncertainty for Franchises: Individual franchisees are left in the dark about potential risks and necessary countermeasures, which could expose them to continued vulnerability.
- Hindered Remediation: Without official confirmation, it becomes challenging for affected parties (if any) to take proactive steps to secure their systems or protect their data.
- Public Perception: Prolonged silence can be perceived negatively by the public and investors, suggesting either a lack of awareness, an attempt to conceal, or an ongoing internal investigation.
In cybersecurity incidents, swift and transparent communication, even if preliminary, is often crucial for managing fallout and trust. The absence of such communication increases the urgency for internal investigations and robust security audits.
Remediation Actions and Proactive Security Measures
Given the nature of the alleged leak, immediate and comprehensive remediation actions are critical for any organization operating a similar franchise model or handling sensitive payment integration data. Even without official confirmation, these best practices should be standard:
- Immediate Credential Rotation: All payment integration credentials, API keys, and secret tokens must be invalidated and rotated across all affected and potentially affected systems.
- Comprehensive Security Audit: Conduct a thorough security audit of all franchise databases, payment gateways, and interconnected systems. This includes penetration testing, vulnerability assessments, and configuration reviews.
- Network Segmentation: Implement or strengthen network segmentation to isolate critical systems, particularly those involved in payment processing and sensitive data storage. This limits the lateral movement of threat actors in case of a breach.
- Multi-Factor Authentication (MFA): Mandate MFA for all administrative access to critical systems and for franchisee portals.
- Supply Chain Security Review: Evaluate the security posture of all third-party vendors and service providers, especially those involved in payment processing or data management.
- Incident Response Plan Activation: Activate and review the organization’s incident response plan. Ensure all stakeholders, including legal, communications, and technical teams, are prepared to act.
- Employee Training: Conduct regular cybersecurity awareness training for all employees and franchisees, focusing on phishing, social engineering, and secure data handling practices.
- Regular Backups: Ensure secure, offsite, and frequent backups of all critical data.
- Patch Management: Maintain a rigorous patch management program for all software, operating systems, and hardware. While no specific CVE is identified for this alleged incident, maintaining up-to-date systems closes known vulnerabilities (e.g., CVE-2023-XXXXX).
Tools for Detection and Mitigation
To preempt and detect similar threats, organizations should leverage a combination of security tools and practices:
| Tool Name | Purpose | Link |
|---|---|---|
| Intrusion Detection/Prevention Systems (IDPS) | Monitors network traffic for malicious activity and policy violations, blocking detected threats. | Cisco Secure IPS |
| Security Information and Event Management (SIEM) | Collects and analyzes security logs from various sources to detect and alert on security incidents. | Splunk Enterprise Security |
| Vulnerability Scanners | Identifies security weaknesses in applications, systems, and networks. | Tenable Nessus |
| Endpoint Detection and Response (EDR) | Monitors endpoint and network events, providing advanced threat detection, investigation, and response capabilities. | CrowdStrike Falcon Insight |
| Data Loss Prevention (DLP) | Prevents sensitive data from leaving the organization’s network, crucial for protecting credentials and PII. | Symantec DLP |
Key Takeaways for a Resilient Security Posture
The alleged leak of the Wendy’s International Franchise Database serves as a stark reminder of the sophisticated and persistent threats facing interconnected business ecosystems. Organizations must prioritize robust cybersecurity measures, particularly in safeguarding payment integrations and franchisee data. Proactive security audits, stringent access controls, immediate response capabilities, and continuous employee training are not merely recommended but essential. The interconnected nature of modern business means that a compromise in one area can have cascading effects, making a layered and comprehensive security strategy indispensable for resilience in the face of evolving cyber threats.