Apex – AI-Powered Pentester Attacks Apps in Black-Box Mode to Find Vulnerabilities
In the relentless pursuit of robust software security, traditional penetration testing often struggles to keep pace with rapid development cycles. Security teams face immense pressure to identify and remediate vulnerabilities before they can be exploited. This challenge is magnified by the complexity of modern applications and the sheer volume of code being deployed. Enter a new paradigm in security testing: AI-powered autonomous agents designed to unearth flaws with unprecedented speed and efficiency.
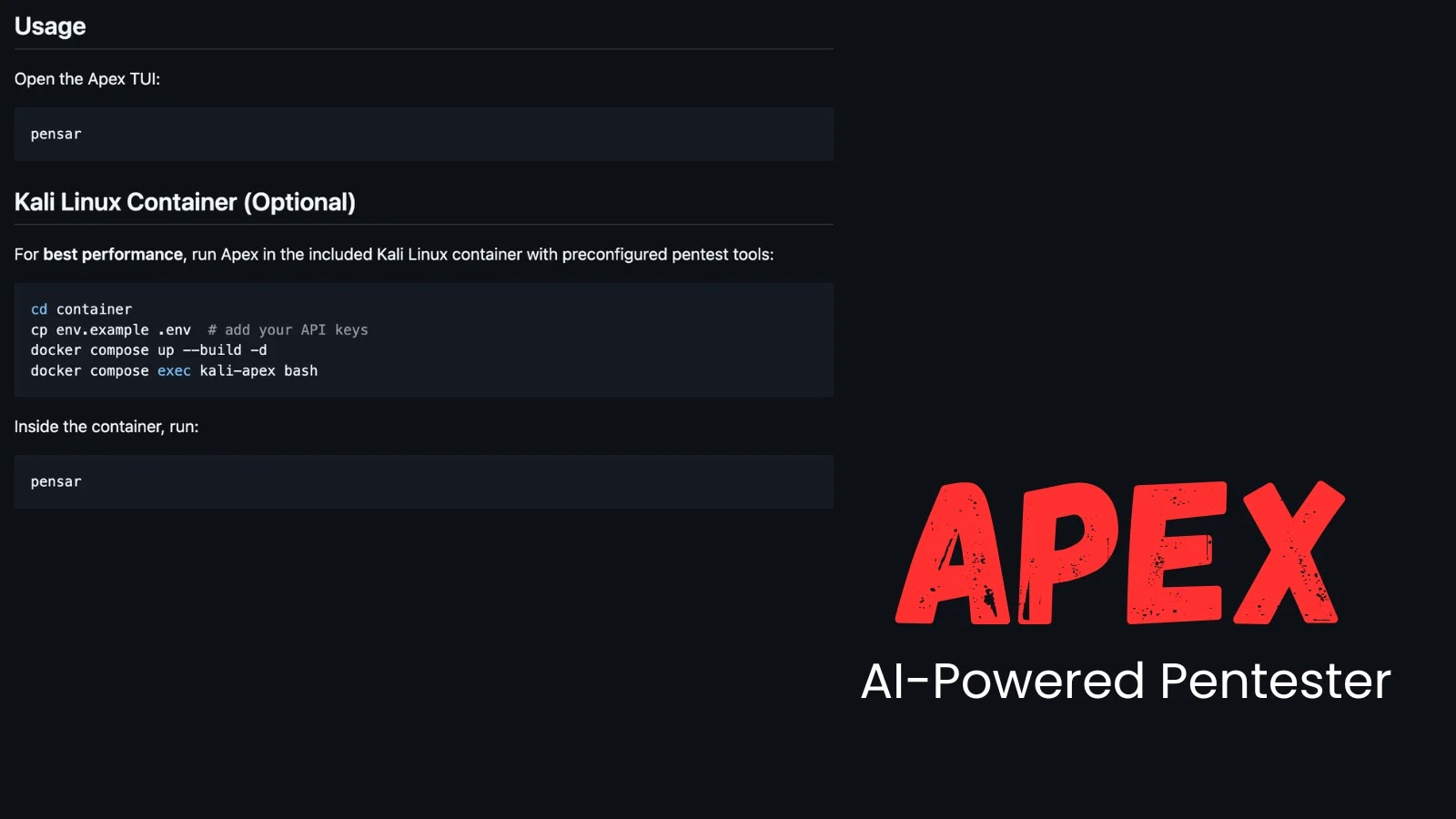
Introducing Apex: The Autonomous AI Pentester
The cybersecurity landscape has witnessed a significant leap forward with the emergence of Apex, an innovative AI-powered penetration testing agent. Unlike conventional static or dynamic application security testing (SAST/DAST) tools, Apex operates in a unique black-box mode. This means it requires no prior knowledge of the application’s internal workings, source code, design specifications, or predefined attack paths. It behaves much like a real-world attacker, interactively probing live applications to discover weaknesses.
Black-Box Penetration Testing Reimagined
Apex’s black-box approach is a critical distinction. Traditional penetration testing often relies on grey-box or white-box methods, where testers have some level of access or information about the application. While valuable, these methods can be time-consuming and may not always reflect the tactics of an external, uninformed attacker. Apex’s ability to operate without internal insights significantly broadens its attack surface and increases the likelihood of finding exploitable vulnerabilities that might otherwise be overlooked.
Discovery, Chaining, and Verification at Speed
The speed and accuracy with which Apex operates address a core pain point in modern software development. It’s designed not just to identify isolated vulnerabilities but to actively chain them together, mimicking sophisticated attack sequences. This process of discovery, chaining, and verification ensures that the identified issues are not merely theoretical flaws but represent genuine, exploitable security gaps. This streamlined workflow is essential for keeping pace with DevOps and agile environments, where delays in security testing can become critical bottlenecks.
Consider a scenario where an application might have a seemingly innocuous input validation flaw (e.g., related to CVE-2023-38036, a common vulnerability type for injection). Apex could potentially leverage this initial entry point to chain it with another weakness, such as an insecure deserialization vulnerability (similar to those covered by CVE-2023-21949), ultimately leading to remote code execution. This multi-stage attack simulation is incredibly valuable for understanding true risk.
The Catalyst for Autonomous Penetration Testing
The underlying mechanism enabling Apex’s autonomous capabilities is its structural intelligence, which allows it to comprehend application logic and adapt its attack strategies dynamically. This contrasts sharply with signature-based or rule-based security tools that are limited by their predefined knowledge. Apex uses advanced AI algorithms to learn from application responses, evolving its attack vectors in real-time to find and exploit weaknesses.
Implications for Cybersecurity Professionals
For IT professionals, security analysts, and developers, tools like Apex represent a significant shift. They don’t replace human pentesters but rather augment their capabilities, freeing up expert time for more complex, nuanced, and strategic security challenges. Apex can act as a force multiplier, running continuous security assessments in development, staging, and even production environments, providing constant feedback on an application’s security posture.
Key takeaways:
- Apex is an autonomous, AI-powered penetration testing agent.
- It operates in black-box mode, requiring no source code or internal knowledge.
- It excels at discovering, chaining, and verifying real-world vulnerabilities.
- Its speed and efficiency are crucial for modern DevOps and agile workflows.
- Ultimately, Apex enhances security by providing continuous, scalable vulnerability assessment, allowing human experts to focus on higher-level threat analysis and remediation strategies.





