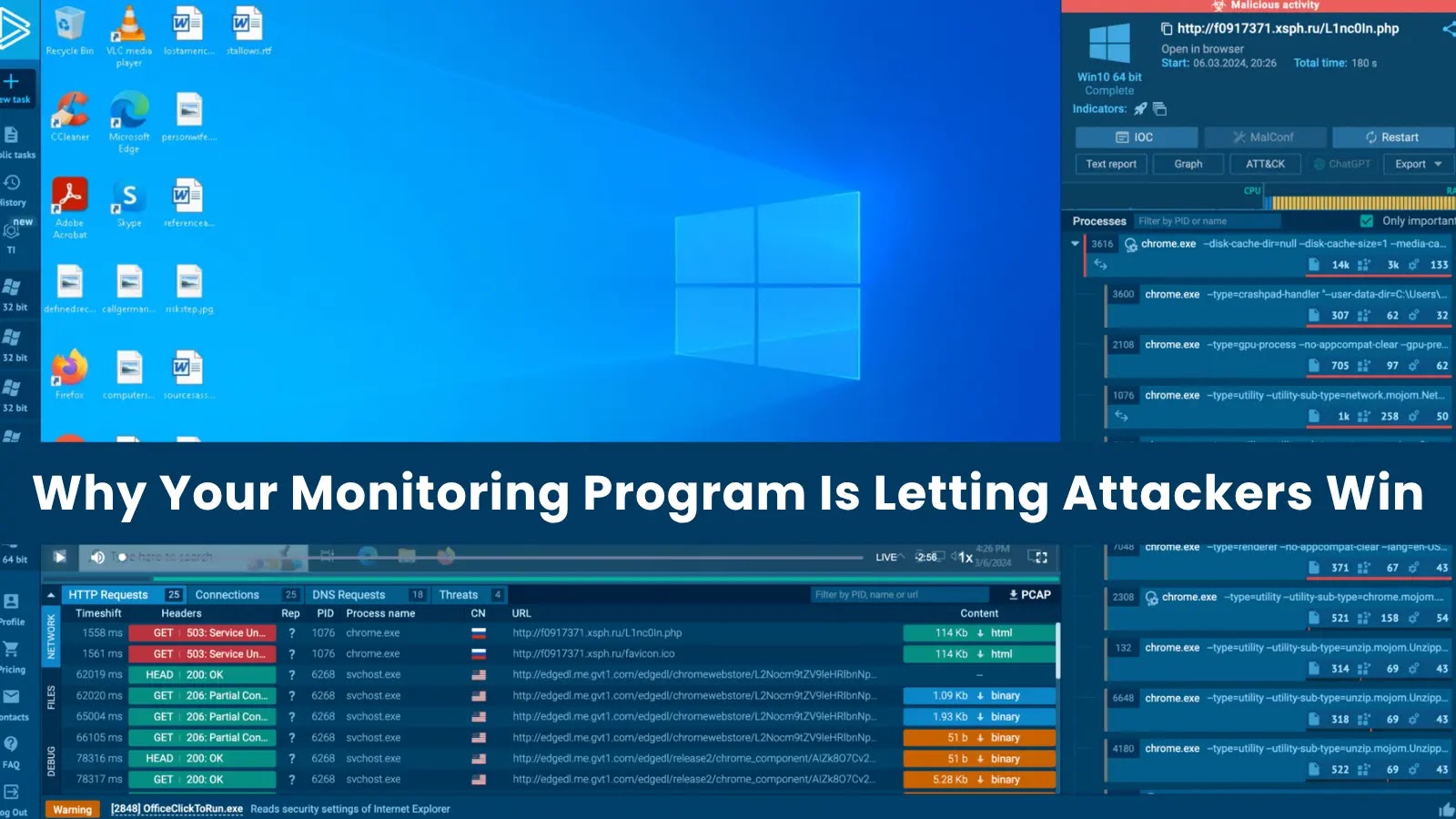
Why Your Monitoring Program Is Letting Attackers Win
In the high-stakes world of cybersecurity, a sophisticated monitoring program is often considered the bedrock of defense. Organizations invest heavily in advanced logging infrastructures, myriad detection rules, and dashboards brimming with operational metrics. Yet, a stark reality often emerges: despite this impressive facade, attackers frequently dwell within networks for weeks or even months, executing reconnaissance, achieving lateral movement, exfiltrating sensitive data, and meticulously preparing their final payloads—all while remaining completely undetected.
This isn’t a failure of technology or a lack of investment in security tools. Rather, it points to a critical disconnect in how many organizations approach their threat monitoring strategies. The problem isn’t the presence of monitoring, but its efficacy. Let’s delve into why your seemingly robust monitoring program might be inadvertently allowing attackers to secure their wins.
The Illusion of Comprehensive Logging
Many organizations equate high log ingestion volumes with superior security. The more logs accumulated, the better, right? Not necessarily. While comprehensive logging is a foundational element, an overwhelming deluge of uncontextualized data can be as detrimental as insufficient logging. Security teams often find themselves drowning in noise, struggling to discern legitimate threats from background chatter. This “signal-to-noise” problem means that critical indicators of compromise (IoCs) are easily missed amidst terabytes of benign entries.
- Raw Volume vs. Relevant Context: Focus on logging data that provides meaningful context about user behavior, system changes, network flows, and application interactions, rather than indiscriminately collecting everything.
- Alert Fatigue: An abundance of low-fidelity alerts creates alert fatigue, leading analysts to either ignore warnings or become desensitized to their urgency.
Detection Rules: Quantity Over Quality
The number of detection rules deployed often becomes another metric of a program’s perceived strength. Hundreds, or even thousands, of rules might populate a Security Information and Event Management (SIEM) system. However, the effectiveness of these rules hinges on their quality, specificity, and ongoing tuning. Stale, generic, or poorly configured rules are easily bypassed by even moderately sophisticated attackers.
- Signature-Based Limitations: Over-reliance on signature-based rules means that zero-day exploits or novel attack techniques will bypass detection. Attackers are constantly evolving, and static rules struggle to keep pace.
- Lack of Behavioral Analytics: Many programs lack robust behavioral analytics that can identify deviations from normal baseline activities. Lateral movement, privilege escalation, and data exfiltration often present as anomalous behaviors rather than matching a known signature.
- Poor Rule Tuning: Rules often generate too many false positives, leading to their eventual disabling or ignoring, thereby opening critical detection gaps.
Unseen Gaps in Coverage and Context
Even with substantial logging and a plethora of rules, critical gaps often persist. These gaps are not always technological; they can be procedural, contextual, or human-centric.
- Blind Spots: Are all critical assets and network segments adequately monitored? Often, shadow IT, forgotten legacy systems, or newly provisioned cloud resources bypass the established monitoring framework entirely.
- Lack of Threat Intelligence Integration: Effective monitoring should be augmented by actionable threat intelligence. Without integrating real-time intelligence on emerging threats, attacker TTPs (Tactics, Techniques, and Procedures), and IoCs, monitoring remains reactive rather than proactive.
- Insufficient Contextualization: An alert about a suspicious login from an unusual IP address means very little without context. Is it a user on vacation? A legitimate remote employee? Or an attacker? Lacking context, analysts cannot effectively triage and respond.
The Human Element: Skill Gaps and Burnout
Technology alone cannot secure an organization. The effectiveness of any monitoring program is heavily reliant on the skilled analysts interpreting the data, triaging alerts, and launching investigations. Unfortunately, many security operations centers (SOCs) face significant challenges:
- Skill Shortages: A global shortage of cybersecurity talent means that many SOCs are understaffed or staffed by less experienced personnel.
- Analyst Overload and Burnout: The sheer volume of alerts, coupled with the pressure of protecting an organization, can lead to chronic stress and high rates of burnout among security analysts.
- Lack of Training: Analysts require continuous training on new threats, tools, and investigative techniques to remain effective.
Remediation Actions: Fortifying Your Monitoring Program
To transition from a program that looks good on paper to one that genuinely protects, consider these actionable steps:
- Prioritize Logging Quality: Instead of ingesting everything, define a log retention strategy based on asset criticality, compliance requirements, and threat model. Focus on high-fidelity logs, such as endpoint detection and response (EDR) data, authentication logs, network flow data, and cloud activity logs.
- Adopt Behavioral Analytics: Implement tools and strategies that baseline normal behavior and detect anomalies. This includes User and Entity Behavior Analytics (UEBA) solutions.
- Refine and Tune Detection Rules: Regularly review and update detection rules. Prioritize rules that detect known attacker TTPs (e.g., as outlined by MITRE ATT&CK). Implement aggregation and correlation rules to reduce alert volume and highlight critical threats.
- Integrate Threat Intelligence: Subscribe to reputable threat intelligence feeds and integrate them directly into your SIEM and other security tools. Automate the enrichment of alerts with relevant threat intelligence.
- Conduct Regular Purple Teaming: Engage in purple team exercises where red teams (attackers) simulate real-world threats and blue teams (defenders) work with them to improve detection and response capabilities. This helps identify blind spots and validate detection efficacy.
- Invest in Your Security Team: Provide continuous training, foster a culture of knowledge sharing, and implement strategies to prevent analyst burnout. Automate repetitive tasks where possible to free up analysts for more complex investigations.
- Implement Clear Incident Response Playbooks: For every detected threat, have a well-defined and rehearsed incident response playbook to ensure swift and effective containment and remediation.
- Regularly Audit Cloud Configurations: For organizations leveraging cloud infrastructure, ensure continuous monitoring of cloud configurations and activity logs to detect unauthorized changes or suspicious activities. (e.g., A misconfigured S3 bucket, though not directly a CVE, is a common vulnerability that effective monitoring should detect).
Conclusion
A monitoring program that fails to detect sophisticated threats isn’t just an inefficiency; it’s a critical vulnerability. The challenge isn’t merely about collecting data or deploying tools; it’s about intelligent data collection, contextualized analysis, high-fidelity detection, and empowering skilled human analysts. By shifting focus from sheer volume to strategic efficacy, organizations can transform their monitoring from a perceived security measure into a formidable defense against persistent and evolving cyber adversaries.





