New Windows Error Reporting Vulnerability Lets Attackers Escalate to Gain SYSTEM Access
A silent threat lurked within the venerable Windows Error Reporting (WER) service, a component many Windows users scarcely consider, yet one crucial for system stability. Recent analysis has exposed a severe local privilege escalation vulnerability, tracked as CVE-2026-20817, that allowed attackers to effortlessly gain full SYSTEM access on affected machines. This isn’t merely a bug; it was a structurally dangerous flaw that prompted Microsoft to take the extraordinary step of completely removing the culpable feature rather than attempting a traditional code-level patch. For IT professionals, security analysts, and developers, understanding the implications and remediation is paramount.
The Windows Error Reporting Vulnerability: CVE-2026-20817 Explained
The core of this critical security flaw resided within the main executable library of the Windows Error Reporting service. The WER service is designed to collect and send error data to Microsoft when applications crash or stop responding. While seemingly innocuous, an exploit against CVE-2026-20817 leveraged a weakness that enabled a local attacker with standard user privileges to escalate to SYSTEM-level access. Gaining SYSTEM access effectively grants an attacker complete control over the compromised operating system, allowing them to install programs, view, change, or delete data, and create new accounts with full user rights.
The severity of this local privilege escalation (LPE) vulnerability was underscored by Microsoft’s response. Instead of issuing a patch that might attempt to fix the underlying code, they opted for an outright removal of the vulnerable feature. This action highlights the deep-seated nature of the flaw, indicating that a traditional patch might have been insufficient or presented further avenues for exploitation. Such a drastic measure is rare and speaks volumes about the potential impact CVE-2026-20817 could have had.
How Local Privilege Escalation Works
Local privilege escalation vulnerabilities are a common and highly sought-after exploit by attackers once they’ve gained an initial foothold on a system. Here’s a typical breakdown of the attack chain:
- Initial Access: An attacker first needs to gain low-level user access to a system. This could be achieved through phishing, exploiting application vulnerabilities, or compromised credentials.
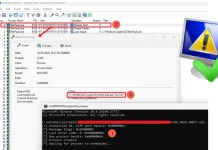
- Vulnerability Identification: Once on the system, the attacker identifies a local privilege escalation vulnerability, such as CVE-2026-20817 in the Windows Error Reporting service.
- Exploitation: The attacker executes specially crafted code that leverages the identified flaw. In the case of WER, this would involve manipulating the service’s functions or data handling.
- Privilege Gain: The exploit allows the attacker’s low-privilege process to execute code or operations with higher privileges, ultimately achieving SYSTEM access in this scenario.
With SYSTEM privileges, an attacker can disable security software, create backdoors, access sensitive data, and persist on the network, turning an initial compromise into a far more significant breach.
Remediation Actions for CVE-2026-20817
Given Microsoft’s action, the primary remediation for CVE-2026-20817 is straightforward: apply the latest Windows updates immediately. Microsoft’s decision to remove the vulnerable feature means that installing the relevant security patch will effectively eliminate the exploit vector. Organizations and individuals running Windows operating systems must prioritize these updates.
Additional defensive strategies should include:
- Regular Patch Management: Ensure all systems are kept up-to-date with the latest security patches for the operating system and all installed applications.
- Principle of Least Privilege: Enforce strict adherence to the principle of least privilege, ensuring users and applications only have the minimum necessary access rights to perform their functions. This limits the impact of a low-level compromise.
- Endpoint Detection and Response (EDR): Implement and monitor EDR solutions to detect suspicious activities and potential privilege escalation attempts. EDR tools can often identify unusual process behavior or system calls indicative of an ongoing attack.
- Vulnerability Scanning: Regularly scan your environment for known vulnerabilities, misconfigurations, and outdated software.
- Security Awareness Training: Educate users about phishing and other social engineering tactics that could lead to initial system access.
Tools for Detection and Mitigation
Effective defense against vulnerabilities like CVE-2026-20817 involves a combination of proactive scanning and reactive monitoring. Here’s a table of useful tools:
| Tool Name | Purpose | Link |
|---|---|---|
| Microsoft Windows Update | Primary mitigation: Installs patches that remove the vulnerable WER feature. | Microsoft Support |
| Tenable Nessus | Vulnerability scanning for identifying missing patches and other security weaknesses. | Tenable.com |
| Qualys VMDR | Comprehensive vulnerability management, detection, and response platform. | Qualys.com |
| Microsoft Defender for Endpoint | Endpoint Detection and Response (EDR) for real-time monitoring and threat hunting. | Microsoft Security |
| Sysmon (Sysinternals) | Monitors and logs system activities, useful for detecting unusual process creation or activity that could indicate LPE. | Microsoft Docs |
Conclusion
The discovery and remediation of CVE-2026-20817 serve as a stark reminder of the persistent threat posed by local privilege escalation vulnerabilities. While the immediate danger has been addressed by Microsoft’s decisive action to remove the vulnerable feature, the incident underscores the critical importance of a proactive security posture. Regular patching, adherence to the principle of least privilege, and continuous monitoring are not just best practices—they are necessities in safeguarding digital assets against evolving threats. For cybersecurity professionals, staying informed about such critical vulnerabilities and implementing timely remediations is paramount to maintaining a robust defensive perimeter.





