How Elite SOCs Cut Escalation Rates by Arming Tier 1 With Better Threat Intelligence
In the high-stakes world of cybersecurity, a Security Operations Center (SOC) is the frontline defense against ever-evolving threats. Yet, even in mature SOC environments, a critical challenge persists: alert escalation. What should be a precise, surgical process, reserved for complex incidents demanding expert intervention, too often devolves into a reflex action. This “pass the buck” mentality plagues many teams, turning a deliberate function into a mere pressure valve for uncertainty. The result? Strained resources, delayed incident response, and an ultimately less effective security posture.
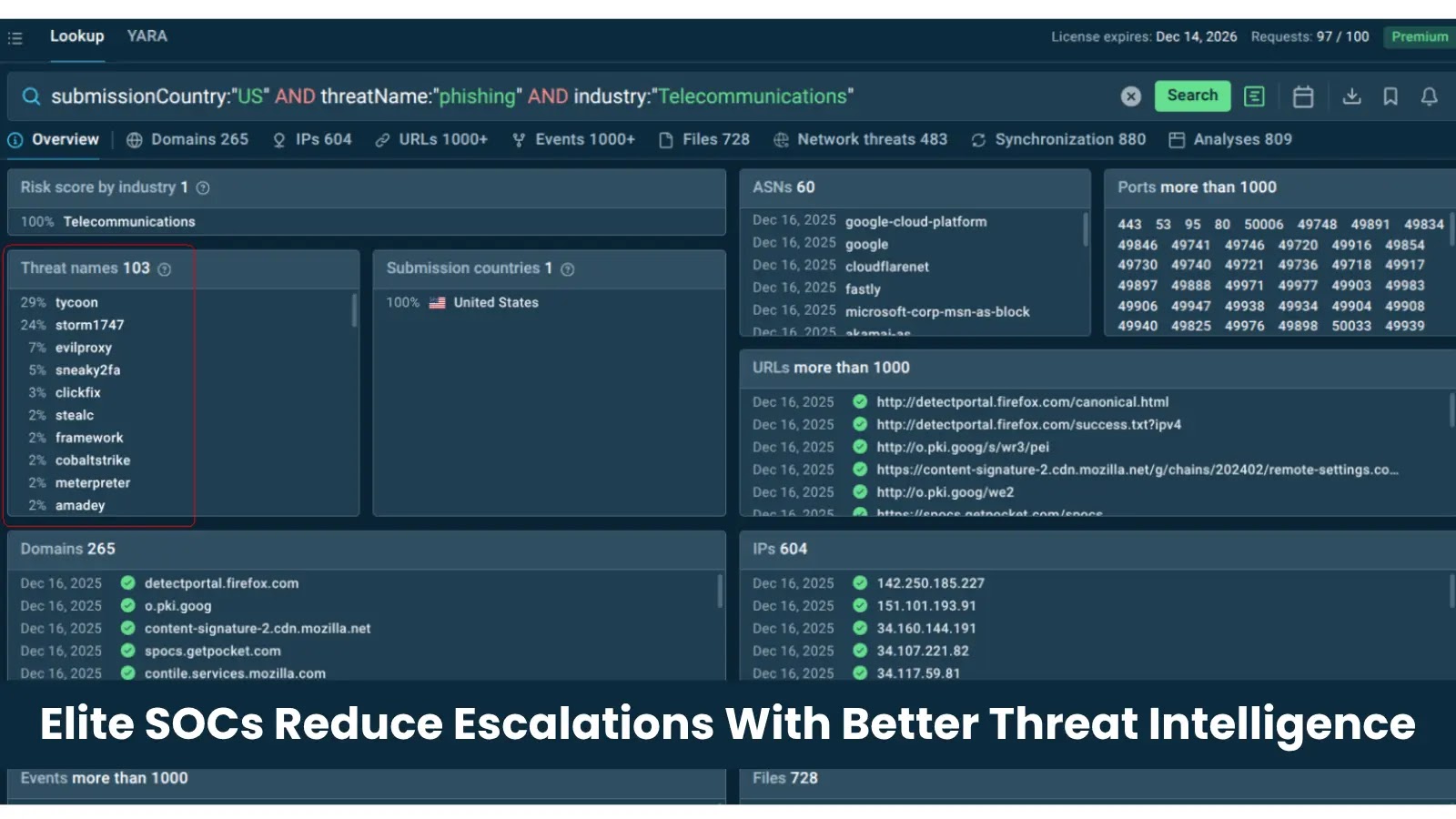
Elite SOCs, however, have cracked the code. They understand that equipping Tier 1 analysts with superior threat intelligence isn’t just about reducing noise; it’s about empowering them to make better, faster decisions. This strategic shift transforms Tier 1 from a mere triaging point to a powerful initial containment and resolution hub, significantly cutting escalation rates and bolstering overall operational efficiency. This article will delve into how leading SOCs achieve this critical advantage.
The Escalation Conundrum: Why Tier 1 Struggles
The core issue often lies in inadequate context. Tier 1 analysts, traditionally, are tasked with sifting through a deluge of alerts generated by various security tools. Without rich, actionable intelligence, differentiating a true positive from a false positive or low-priority event becomes a laborious, often overwhelming, task. This lack of clear signals forces a risk-averse default: escalate. Common reasons for this include:
- Insufficient Data: Many SIEM alerts lack the granular detail needed for definitive decisions.
- Limited Context: Without understanding the “who, what, where, and why” behind an IP address or domain, its malicious intent is hard to ascertain.
- Skill Gap: While proficient in initial triage, Tier 1 often lacks the deep forensic or reverse engineering skills of Tier 2/3.
- Alert Fatigue: A constant stream of low-fidelity alerts desensitizes analysts, leading to blanket escalations.
Each unnecessary escalation consumes valuable Tier 2 and Tier 3 analyst time, diverting them from strategic threat hunting and complex incident resolution to re-triage issues that could have been handled earlier in the chain.
Empowering Tier 1 with Actionable Threat Intelligence
The solution isn’t to simply demand more from Tier 1 but to equip them with the tools and information to succeed. Elite SOCs achieve this by integrating comprehensive threat intelligence directly into the Tier 1 workflow. This isn’t just about providing raw data; it’s about delivering context-rich, prioritized, and machine-readable intelligence. Key aspects include:
- Contextual Enrichment: Automatically enriching alerts with reputation scores, associated campaigns, threat actor profiles, observed TTPs (Tactics, Techniques, and Procedures), and historical prevalence. For example, an alert involving a connection to IP address
192.0.2.1might be immediately flagged as a known command-and-control (C2) server for a specific ransomware variant documented under CVE-2023-34567. - Automated Prioritization: Using intelligence to dynamically rank alerts based on real-time threat landscapes, organizational specific risks, and asset criticality. This allows Tier 1 to focus on what truly matters.
- Playbook Integration: Linking specific threat intelligence artifacts to automated or semi-automated playbooks for initial containment, blocking, or further investigation steps. If an alert involves a domain known for phishing campaigns, the playbook might automatically block the domain at the perimeter and scan internal endpoints for similar indicators.
- Indicator Reputation and Lifecycle: Providing real-time insight into the reputation of IPs, domains, hashes, and email addresses. Is an observed indicator a newly emerged threat, or one that has been active for months? This lifecycle information is crucial.
- Vulnerability Context: Connecting observed threats to known vulnerabilities within the organization’s asset inventory. An alert concerning an attempted exploit against a system, such as a known vulnerability like CVE-2024-12345, immediately informs the Tier 1 analyst of its potential severity and aids in initial triage.
Tangible Benefits: Reduced Escalation, Improved Efficiency
The impact of arming Tier 1 with advanced threat intelligence is profound:
- Reduced False Positives: High-fidelity intelligence helps rapidly discard benign alerts, dramatically cutting down the volume of items requiring human review.
- Faster Triage and Resolution: Analysts can quickly contextualize alerts, leading to faster decisions on whether to contain, resolve, or escalate.
- Empowered Tier 1: Analysts gain confidence and a broader skillset, reducing dependence on higher tiers for routine investigations.
- Frees Up Senior Analysts: Tier 2 and Tier 3 teams can dedicate more time to complex incidents, threat hunting, and strategic security initiatives, rather than re-triaging basic alerts.
- Improved Mean Time To Respond (MTTR): By resolving incidents lower in the chain, the overall time to detect and respond to threats decreases significantly.
Remediation Actions: Implementing Enhanced Threat Intelligence for Tier 1
For organizations looking to emulate elite SOCs and slash their escalation rates, consider these actionable steps:
- Assess Current Threat Intelligence Capabilities: Understand what intelligence sources are being consumed, how they are integrated, and their current impact on Tier 1 operations.
- Integrate a Robust Threat Intelligence Platform (TIP): A TIP centralizes, normalizes, and enriches intelligence from various sources, making it digestible for analysts and automated systems.
- Focus on Contextual Enrichment: Ensure that your SIEM or SOAR platform automatically enriches alerts with relevant threat intelligence before they reach a Tier 1 analyst. This should include reputation, associated campaigns, and known vulnerabilities (e.g., linking to CVE-2023-98765 if applicable).
- Develop Tier 1-Specific Playbooks: Create clear, intelligence-driven playbooks that guide Tier 1 analysts through common alert types, outlining specific actions based on intelligence context.
- Invest in Analyst Training: Train Tier 1 analysts on how to effectively use threat intelligence platforms, interpret enriched data, and understand the geopolitical landscape of common threat actors.
- Automate Where Possible: Leverage SOAR capabilities to automate initial containment or enrichment based on high-confidence threat intelligence, further reducing manual workload.
- Continuous Feedback Loop: Establish a feedback mechanism between Tier 1 and higher tiers to refine intelligence sources, threat detection rules, and playbooks based on real-world outcomes.
Conclusion
The evolution from a reactive, escalation-heavy SOC to a proactive, intelligence-driven one is not merely an aspiration; it’s a strategic imperative. By arming Tier 1 analysts with targeted, contextual, and actionable threat intelligence, organizations can transform their security operations. This empowers the frontline, reduces alert fatigue, and enables a more precise, efficient, and ultimately more secure environment. Elite SOCs understand this principle: the scalpel of escalation should be reserved for genuine emergencies, not as a default for uncertainty, and robust threat intelligence is the key to sharpening Tier 1’s decision-making capabilities.





