Detecting SaaS Privilege Abuse with Session Monitoring.
Detecting SaaS Privilege Abuse with Session Monitoring and Management Access
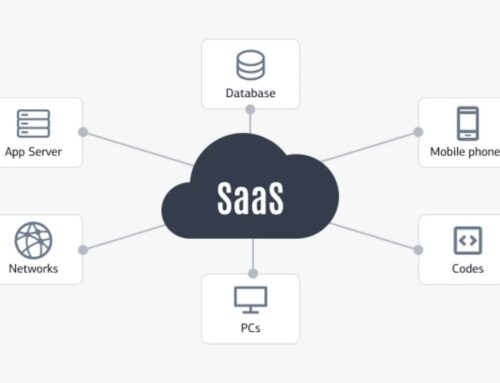
In today’s interconnected digital landscape, the security of Software as a Service (SaaS) environments is paramount. Privilege abuse, particularly within SaaS applications, poses a significant threat to organizations of all sizes. This article delves into the critical aspects of detecting SaaS privilege abuse through effective session monitoring and management access strategies. By understanding privileged access, its inherent risks, and the tools available, organizations can fortify their defenses against insider threats and potential data breaches.
Understanding Privileged Access
Privileged access refers to the elevated rights and permissions granted to certain user accounts, service accounts, or processes within an IT system. These privileges enable access to sensitive data, critical configurations, and core functionalities, surpassing the capabilities of standard user accounts. Managing and monitoring privileged access is crucial for maintaining a robust security posture and preventing malicious activities that could compromise the entire organization.
Definition of Privileged Access
Privileged access is defined as the authorization granted to user accounts or processes allowing them to perform sensitive actions that a standard user cannot, often involving specific access rights. This elevated access, often required for administrative tasks, database management, and system configurations, introduces significant security risks if not properly managed. The principle of least privilege dictates that only the minimum necessary access should be granted to each user, reducing the potential attack surface.
Types of Privileged Accounts
Privileged accounts come in various forms, each presenting unique security challenges. These accounts can include:
- User accounts with administrative permissions, which grant broad control over systems and applications.
- Service accounts, used by applications to interact with the operating system, also require careful management to prevent unauthorized access to sensitive data.
Additionally, emergency access accounts are used for break-glass scenarios needing elevated access to maintain security.
Importance of Privileged Access Management (PAM)
Privileged Access Management (PAM) is crucial for organizations to secure their SaaS environments. Teamwin Global Technologica provides PAM solutions, including access security and identity and access management features. A robust PAM solution is essential to manage privileged identities and enforce least privilege access, which reduces the risk of both insider threats and external breaches. With PAM, security teams gain the visibility needed to monitor privileged sessions, detect malicious activities, and respond swiftly to security incidents.
Session Management in SaaS Environments
What is Session Management?
Session management in SaaS environments is the process of controlling user access to applications and data during an active session. Effective session management involves authentication, authorization, and maintaining the user’s state as they interact with the application. Robust session management is crucial for enforcing access control and protecting sensitive data. Without adequate controls, SaaS environments are exposed to security risks, including unauthorized access, privilege escalation, and potential data breaches. A comprehensive approach to session management ensures only authenticated and authorized users gain access to appropriate resources, mitigating potential insider threats and enhancing overall security posture.
Role of Session Monitoring
Session monitoring plays a vital role in detecting and preventing privilege abuse in SaaS environments. By implementing privileged session monitoring, security teams gain real-time visibility into user activities, including privileged activities performed by privileged users. Session recording and audit trail functionalities provide detailed records of privileged sessions, enabling security teams to identify anomalous access patterns and detect malicious activities in real time. Proactive session monitoring helps in identifying and responding to security incidents promptly, mitigating potential data breaches and privilege escalation attempts. With session monitoring, organizations can strengthen their security posture and safeguard against insider threats.
Best Practices for Session Management
Implementing best practices for session management is essential for maintaining a secure SaaS environment. Several key actions are crucial in this regard, including:
- Enforcing least privilege by granting users only the necessary permissions, which reduces the attack surface.
- Using privileged access management tools to manage privileged identities and credentials securely.
- Regularly auditing user access and privileged accounts to detect and address any unauthorized access.
Furthermore, implementing multi-factor authentication enhances security controls, preventing unauthorized logins. Continuous session monitoring and privileged session management are also essential to detect malicious activities and enforce access security, protecting sensitive data and mitigating the risks of insider threats and privilege abuse.
Detecting Abuse through Real-Time Monitoring
Real-Time Session Monitoring Techniques
Real-time session monitoring is a pivotal aspect of detecting privilege abuse in SaaS environments. By implementing privileged session monitoring, security teams gain immediate visibility into user activities, allowing them to detect any malicious actions as they occur. Tools like TeamWin’s real-time Dark Web monitoring provide an additional layer of access security by identifying compromised privileged credentials or data breach attempts, enhancing overall detection and response capabilities. This proactive approach helps organizations to promptly respond to security incidents and prevent further damage through effective identity and access management. Continuous session monitoring enables the identification of anomalous access patterns and unauthorized activities, which can be indicators of insider threats or privilege escalation attempts. These solutions often include session recording, giving security teams the ability to perform detailed audit trail analysis when investigating potential breaches.
Identifying Privilege Escalation Attempts
Identifying privilege escalation attempts is critical for maintaining a robust security posture in SaaS environments, particularly through effective detection and response strategies. Privilege escalation occurs when a user gains elevated access to resources or functionalities beyond their authorized permissions. Session monitoring tools can detect suspicious activities, such as unauthorized access to sensitive data or attempts to modify system configurations, which may indicate a privilege escalation attempt. By analysing access patterns and user behaviour, security teams can identify and mitigate potential risks associated with privilege escalation. Implementing the principle of least privilege is crucial in preventing such attempts, as it limits the potential damage caused by compromised user accounts. Regular privileged access reviews and audit logs are essential for detecting and addressing privilege escalation attempts promptly.
Audit and Log Analysis for Privileged Sessions
Audit and log analysis are indispensable components of privileged session management and overall access security. By regularly reviewing audit trails and log data, security teams can identify anomalous access patterns, unauthorized activities, and potential security incidents. Detailed privileged session recording provides a comprehensive record of user actions, enabling thorough investigations of security breaches and privilege abuse. Integrating audit and log analysis with privileged access management (PAM) solutions enhances visibility into privileged activities and facilitates proactive threat detection. These processes help organizations enforce least privilege access, identify insider threats, and maintain compliance with regulatory requirements. Continuous monitoring and analysis of audit logs, along with real-time detection and response mechanisms, are essential for maintaining a secure SaaS environment and safeguarding sensitive data.
Implementing Privileged Session Management
Strategies for Effective Privileged Session Management
Effective privileged session management strategies, including identity and access management, are crucial for maintaining access security within SaaS environments. By implementing comprehensive privileged session management solutions, organizations can monitor privileged activities in real time and detect potential security incidents. Implementing the principle of least privilege, along with robust access control policies, ensures that privileged users only have the necessary permissions to perform their tasks, thus minimizing the attack surface. Regularly auditing privileged access, integrating privileged session recording, and enforcing multi-factor authentication are key components of a strong privileged session management strategy. Effective privileged session management helps mitigate insider threats, prevent data breaches, and maintain a strong security posture by ensuring proper monitoring of session data.
Integrating Just-in-Time Access
Integrating just-in-time (JIT) access is a best practice for enhancing access security in SaaS environments. JIT access grants privileged users temporary, elevated access only when it is needed, reducing the risk of standing privileges being exploited and ensuring better password management. Integrating JIT access with privileged access management (PAM) solutions provides a streamlined workflow for managing privileged identities and ensuring compliance with the principle of least privilege. Implementing JIT access helps organizations minimize the attack surface, prevent privilege escalation attempts, and improve overall security posture. By granting elevated access only when necessary, JIT access reduces the potential for lateral movement by attackers and limits the impact of compromised privileged credentials.
Using PAM Solutions for Enhanced Security
PAM solutions play a critical role in enhancing security within SaaS environments. These solutions provide centralized management of privileged identities, enforce access control policies, and enable privileged session monitoring. By implementing PAM solutions, organizations gain visibility into privileged activities, detect anomalous access patterns, and respond swiftly to security incidents. PAM solutions, like those provided by Teamwin Global Technologica, often include features such as privileged session recording, audit trail analysis, and real-time alerts for suspicious activities. A robust PAM solution helps enforce least privilege, manage privileged access to sensitive data, and mitigate the risks of insider threats and data breaches, thus ensuring a strong security posture.
Access Control and Security Measures
Establishing Access Control Policies
Establishing robust access control policies is essential for securing SaaS environments and preventing privilege abuse. Access control policies define who can access what resources and under what conditions. Enforcing the principle of least privilege is a cornerstone of effective access control, ensuring that users only have the minimum necessary permissions to perform their job functions. Regularly reviewing and updating access control policies is crucial for maintaining access security and mitigating the risks of unauthorized access and privilege escalation. Implementing multi-factor authentication and role-based access control (RBAC) further strengthens access control and protects sensitive data from insider threats and malicious activities.
Managing Privileged Identities
Managing privileged identities is a critical aspect of access security in SaaS environments. Privileged identities, which include privileged user accounts, service accounts, and emergency access accounts, require special attention due to their elevated access to sensitive data and critical systems. Implementing privileged access management (PAM) solutions helps organizations manage privileged identities, enforce access control policies, and monitor privileged activities, thereby addressing potential blind spots. Regular privileged access reviews, credential rotation, and multi-factor authentication are key components of effective privileged identity management. By managing privileged identities effectively, organizations can reduce the risk of insider threats, prevent data breaches, and maintain a strong security posture.
Least Privilege Principle in SaaS
The principle of least privilege is a fundamental security best practice that dictates users should only be granted the minimum access permissions necessary to perform their job functions, thereby limiting unnecessary data access. Applying this principle in SaaS environments reduces the attack surface, limits the potential damage from compromised user accounts, and prevents privilege escalation attempts. Enforcing least privilege requires careful planning and implementation of access control policies, as well as ongoing monitoring and auditing of user access. Implementing privileged access management (PAM) solutions can help organizations enforce least privilege by providing granular control over user access, enabling privileged session monitoring, and automating access reviews. By adhering to the principle of least privilege, organizations can significantly enhance their security posture and mitigate the risks of insider threats and data breaches.
How does privileged session monitoring improve privileged access security and detect SaaS privilege abuse?
Privileged session monitoring records and analyses sessions initiated by admin accounts, privileged users, and service accounts across modern SaaS platforms to provide a layer of security that complements privileged account and session management. By capturing session data, keystrokes, commands, and screen activity, organizations gain visibility into access to privileged accounts and access to critical systems and data access patterns. Correlating these security events with security information and event management (SIEM) systems enables rapid detection and response to anomalous behaviour, insider threats, lateral movement, or misuse of privileged credentials, strengthening privileged access security and effective privileged access management.
What monitoring capabilities are essential for enforcing least privilege and preventing lateral movement in SaaS platforms?
Effective monitoring capabilities include continuous session recording, real-time alerting on policy violations, contextual analytics, and integration with identity and access management and security information platforms. Enforce least privilege by combining role-based access, strict access policies, and automated workflow approvals for elevated access. Detect lateral movement by tracking unusual access to sensitive systems, correlating sessions with security events, and using behavioural baselines for privileged user and service account activity. This management and monitoring approach reduces attack surface and ensures security and compliance across cloud access and on-premises systems and data.
Can session monitoring integrate with existing privileged access management solutions and SIEM for improved detection and response?
Yes. A privileged session monitoring solution should integrate with privileged access management solution components, security information and event management tools, and identity and access management systems. Integration enables forwarding of session data and security events to SIEM for centralized correlation, long-term retention, and richer incident response. This unified view supports security controls enforcement, auditing of access to privileged accounts and access to sensitive systems, and helps demonstrate compliance with security policies and access policies.
How do access policies and role-based access reduce the risk of credential misuse and insider threats in SaaS environments?
Access policies and role-based access implement the principle of least privilege by granting users only the permissions they need for their job, limiting elevated access and reducing the number of privileged credentials in use. Combined with privileged identity management practices—such as just-in-time access, multi-factor authentication for admin accounts, and automated approvals—these controls shrink the attack surface. Continuous monitoring and security events tracking help detect deviations from expected behaviour, enabling timely mitigation of insider threats and protection of access to critical systems and sensitive data.
What are the best practices for balancing visibility and privacy when monitoring privileged sessions on cloud SaaS platforms?
Best practices include defining clear security policies that specify what session data is captured, retaining only necessary logs for compliance, masking sensitive data where legally required, and using role-based access controls to limit who can view session recordings. Ensure monitoring capabilities are aligned with security and compliance requirements by integrating with security information for audit trails and leveraging anonymization where possible. Document access policies and management and monitoring workflows so stakeholders understand how session monitoring protects systems and data while enforcing security posture and access security without violating user privacy.