Where Most SOCs Stall: Building SOC Maturity with Threat Intelligence Feeds
For many Security Operations Centers (SOCs), the promise of proactive defense often remains just out of reach. We invest in sophisticated tools and assemble talented teams, yet critical decisions are still made on fragmented information and outdated indicators. This is where most SOCs stall. While threat data cascades in, it frequently remains external to the workflow, a reference rather than a driving force. The true differentiator for mature SOCs lies in a fundamental shift: embedding threat intelligence directly into their operational fabric.
The Stalling Point: Fragmented Intelligence and Outdated Indicators
The core challenge for many SOCs isn’t a lack of data, but a lack of actionable intelligence within their daily processes. Imagine a SOC analyst sifting through alerts, attempting to correlate disparate pieces of information without a unified view of the current threat landscape. This reactive posture is inefficient and leaves organizations vulnerable. The source content highlights this perfectly: “threat data remains external to the workflow.” This disconnect prevents timely, informed decisions, limiting a SOC’s ability to evolve past basic alert triage.
Beyond Reference: What Mature SOCs Do Differently
Mature SOCs don’t just consume threat intelligence; they integrate it. They understand that threat intelligence isn’t merely a feed of indicators of compromise (IOCs) to be cross-referenced; it’s a dynamic dataset that informs every stage of their security operations. This proactive approach transforms threat intelligence from a siloed resource into an indispensable component of their defensive strategy. It’s about empowering analysts with context, anticipating attacks, and prioritizing responses based on real-world threats and attacker methodologies.
Building SOC Maturity with Integrated Threat Intelligence Feeds
Integrating threat intelligence feeds effectively requires more than simply subscribing to a service. It demands a strategic approach to data ingestion, processing, and application. Here’s how to move past the stalling point:
- Automated Ingestion and Enrichment: Threat intelligence shouldn’t be manually reviewed. Automate the ingestion of feeds from reputable sources. Enrich these feeds with internal context, such as known assets, existing vulnerabilities (e.g., CVE-2023-38827, a critical WinRAR vulnerability, or CVE-2023-44487 impacting HTTP/2), and historical incident data.
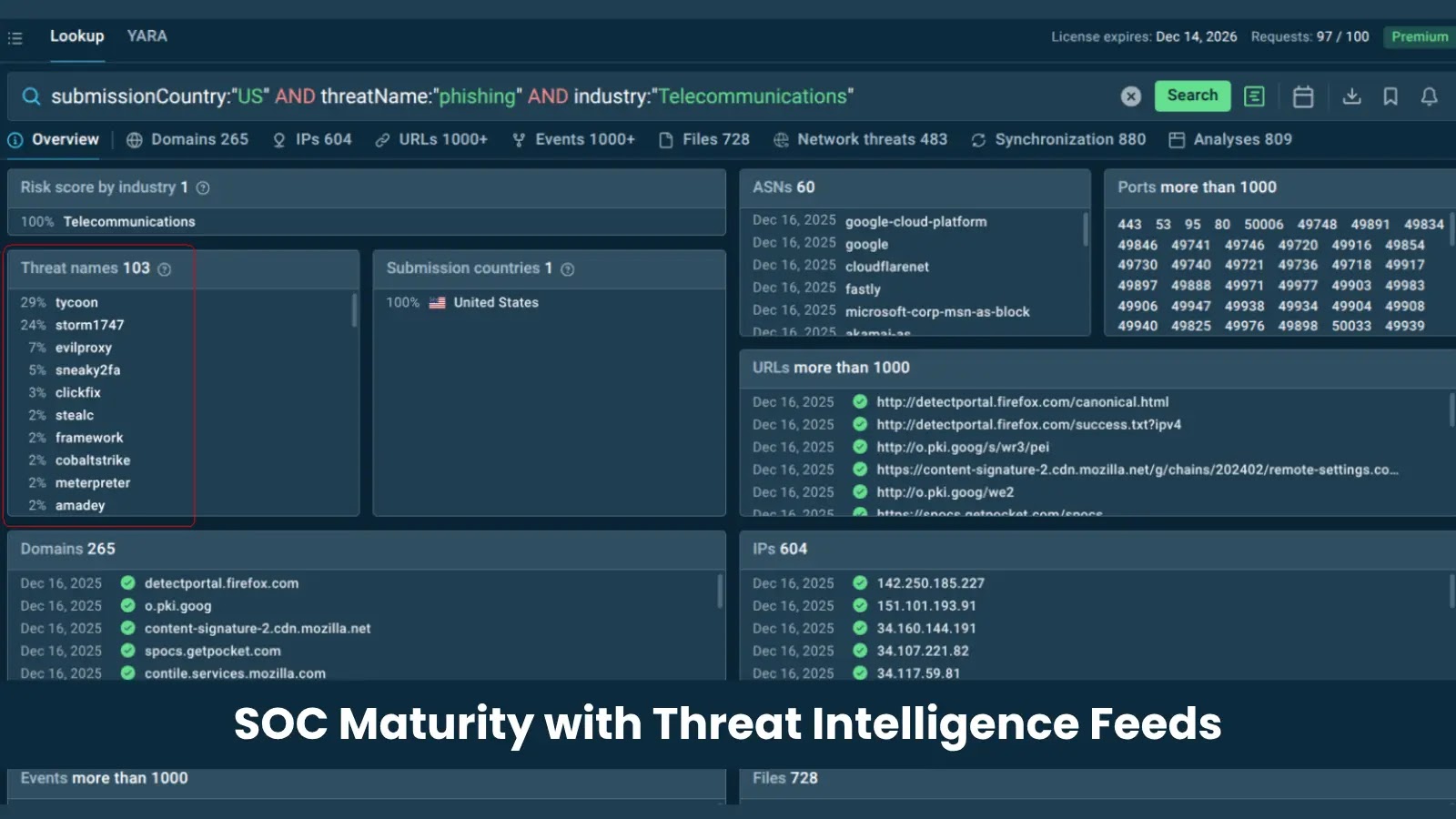
- Contextual Alerting and Prioritization: When an alert fires, threat intelligence should instantly provide context: Is this IP address associated with a known threat actor? Has this domain been flagged for phishing? This context allows analysts to quickly prioritize and respond to the most critical threats, rather than sifting through false positives.
- Proactive Hunting and Detection: Threat intelligence feeds are invaluable for proactive threat hunting. By understanding current attacker techniques, tactics, and procedures (TTPs), SOC teams can actively search for anomalous behavior that might otherwise go unnoticed.
- Incident Response Acceleration: During an incident, timely access to relevant threat intelligence can significantly reduce dwell time and accelerate containment. Knowing the likely adversaries, their typical attack vectors, and associated IOCs empowers a faster, more effective response.
- Vulnerability Management Enhancement: Threat intelligence provides crucial insights into which vulnerabilities are actively being exploited in the wild. This allows organizations to prioritize patching and mitigation efforts based on real-world risk, rather than simply CVSS scores alone.
Remediation Actions for Stalled SOCs
If your SOC is struggling with fragmented intelligence, consider these steps to enhance your threat intelligence integration:
- Assess Current State: Conduct an audit of your existing threat intelligence sources, how they are consumed, and their actual impact on decision-making. Identify gaps and areas for improvement.
- Define Intelligence Requirements: Work with stakeholders to define what intelligence is most critical for your organization’s specific risk profile. Not all intelligence is created equal; focus on what’s relevant.
- Choose Appropriate Feeds: Select threat intelligence feeds that align with your requirements. Consider open-source intelligence (OSINT), commercial feeds, and sector-specific intelligence sharing groups (ISACs/ISAOs).
- Integrate with Existing Tools: Implement connectors and APIs to integrate threat intelligence seamlessly with your SIEM, SOAR, EDR, and vulnerability management platforms. Automate the flow of data.
- Train Your Analysts: Provide comprehensive training to your SOC analysts on how to effectively use and interpret threat intelligence. Foster a culture of continuous learning about new threats and TTPs.
- Measure and Refine: Regularly evaluate the effectiveness of your threat intelligence program. Track key metrics such as reduced mean time to detect (MTTD) and mean time to respond (MTTR) for incidents where threat intelligence played a crucial role.
Conclusion
The distinction between a stalled SOC and a mature, proactive one often boils down to a single factor: the strategic integration of threat intelligence. By moving beyond treating threat data as an external reference and instead embedding it directly into operational workflows, SOCs can transform their decision-making, accelerate response, and effectively counter the ever-evolving threat landscape. This isn’t just about collecting more data; it’s about making that data truly actionable, enabling security teams to shift from a reactive posture to one of informed, proactive defense.





