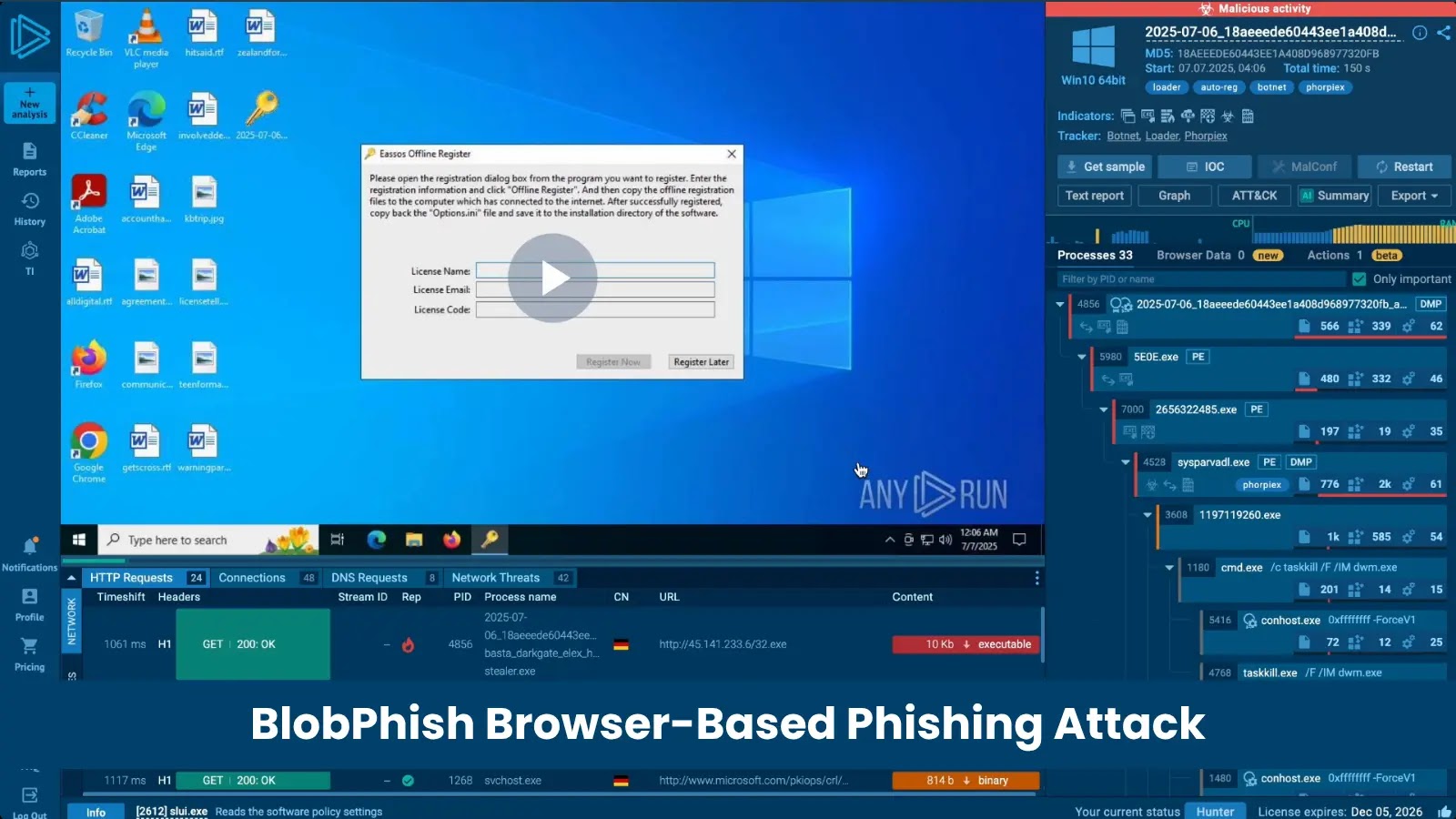
New BlobPhish Attack Leverages Browser Blob Objects to Steal Users’ Login Credentials
Unmasking BlobPhish: A Stealthy New Threat to Your Credentials
The digital landscape is under perpetual siege, with threat actors consistently innovating to bypass established defenses. A critical new development in this ongoing battle is the emergence of BlobPhish, a sophisticated, memory-resident phishing campaign that has been actively targeting users’ login credentials since October 2024. This stealthy operation exploits a seemingly innocuous browser feature – Blob URL APIs – to silently pilfer sensitive information from unsuspecting victims, primarily focusing on Microsoft 365, major U.S. banks, and other financial platforms. What makes BlobPhish particularly insidious is its ability to operate almost entirely under the radar of traditional security tools, necessitating a deeper understanding of its mechanics and effective countermeasures.
What is BlobPhish and How Does it Operate?
BlobPhish represents a significant evolution in credential phishing. Unlike conventional phishing attacks that rely on directly hosting malicious content on easily identifiable domains, BlobPhish leverages browser Blob objects. A Blob (Binary Large Object) is a data type that can store raw data, and Blob URLs are pseudo-protocols that allow browsers to reference and display this data as if it were a file. Threat actors are now weaponizing this legitimate browser functionality.
The attack typically unfolds as follows:
- Victims receive a phishing email containing a seemingly legitimate link.
- Upon clicking this link, instead of being redirected to a malicious server, the browser is instructed to generate a Blob URL.
- This Blob URL then points to a dynamically generated, in-memory phishing page. This page is often a meticulously crafted replica of a legitimate login portal for services like Microsoft 365 or a banking institution.
- Crucially, because the phishing page content resides within the browser’s memory as a Blob object and is accessed via a Blob URL, it bypasses many traditional security checks that inspect URL reputation, domain certificates, or server-side content.
- When users attempt to log in on this “memory-resident” phishing page, their credentials are surreptitiously captured and exfiltrated by the attackers.
This method significantly reduces the attack’s footprint, making it incredibly difficult for network-based security solutions, web filters, and even some endpoint detection and response (EDR) tools to identify and block the attack in real-time. The phishing content never actually touches a malicious server in the conventional sense, leading to its “almost completely invisible” nature.
Targeted Organizations and Impact
The primary targets of the BlobPhish campaign are:
- Microsoft 365 Users: Attackers aim to compromise corporate accounts, leading to potential data breaches, business email compromise (BEC) schemes, and further lateral movement within an organization’s network.
- Major U.S. Banks and Financial Platforms: Stealing financial credentials allows direct access to bank accounts, facilitating financial fraud and theft.
The impact of a successful BlobPhish attack can be severe, ranging from direct financial losses for individuals and organizations to reputational damage, long-term data exposure, and significant recovery costs associated with incident response.
Remediation Actions and Proactive Defense
Given the stealthy nature of BlobPhish, a multi-layered defense strategy is paramount. Organizations and individuals must adopt proactive measures to mitigate this novel threat.
- Enhanced Email Security: Implement advanced email gateway solutions with robust anti-phishing capabilities, including AI-driven anomaly detection and URL sandboxing to identify and quarantine suspicious emails before they reach users.
- User Awareness Training: Continuously educate users about phishing tactics, especially those that mimic legitimate services. Train them to scrutinize URLs (even Blob URLs, which might look unusual), report suspicious emails, and never enter credentials on unexpected login prompts.
- Multi-Factor Authentication (MFA): Mandate MFA for all online accounts, particularly for Microsoft 365 and financial services. Even if credentials are stolen, MFA acts as a critical secondary barrier to unauthorized access.
- Endpoint Detection and Response (EDR) / Extended Detection and Response (XDR): Deploy and properly configure EDR/XDR solutions that can monitor browser processes, detect unusual script execution linked to Blob URL generation, and identify credential exfiltration attempts. Behavioral analysis is key here.
- Browser Security Best Practices: Encourage the use of updated browsers with the latest security patches. Consider browser extensions that enhance security by flagging suspicious elements or isolating web content.
- Network Traffic Analysis (NTA): Although the phishing page is in-memory, the exfiltration of stolen credentials still involves network traffic. NTA tools can help detect anomalous outbound connections or data transfer patterns that might indicate a compromise.
- Regular Security Audits: Conduct frequent security audits and penetration tests to identify potential vulnerabilities in your security posture that could be exploited by new attack vectors.
Detection and Mitigation Tools
While no single tool currently offers a silver bullet against BlobPhish, a combination of technologies can significantly enhance detection and mitigation capabilities.
| Tool Name | Purpose | Link |
|---|---|---|
| Advanced Email Security Gateways (e.g., Proofpoint, Mimecast) | Pre-delivery phishing detection, URL sandboxing, attachment analysis. | Proofpoint, Mimecast |
| Endpoint Detection and Response (EDR) / XDR Solutions (e.g., CrowdStrike, SentinelOne) | Behavioral anomaly detection on endpoints, process monitoring, script analysis. | CrowdStrike, SentinelOne |
| Security Information and Event Management (SIEM) (e.g., Splunk, Microsoft Sentinel) | Aggregating and correlating security logs to identify suspicious activity patterns. | Splunk, Microsoft Sentinel |
| Network Detection and Response (NDR) (e.g., Vectra AI, Darktrace) | Detecting anomalous network traffic, data exfiltration attempts, and command & control communications. | Vectra AI, Darktrace |
Key Takeaways
The BlobPhish campaign underscores the continuous need for vigilance and adaptation in cybersecurity. Its reliance on legitimate browser functionality to deliver memory-resident phishing pages makes it particularly difficult to detect with traditional methods. Organizations and individuals must prioritize robust email security, ubiquitous multi-factor authentication, advanced endpoint protection, and comprehensive user education to defend against this evolving threat. Staying informed about new attack vectors like BlobPhish and implementing a proactive, layered security approach are essential to safeguarding sensitive credentials and mitigating the risk of compromise.





