Low Noise, High Confidence: Optimizing SOC Costs with Better Threat Intelligence
In the complex landscape of modern cybersecurity, Security Operations Centers (SOCs) are constantly battling an onslaught of threats. The goal is clear: robust defense mechanisms that translate into measurable outcomes at an optimal cost. However, achieving this often means sifting through a mountain of data, much of it noisy and irrelevant. The key to high-performing SOCs and cost optimization lies in leveraging superior threat intelligence that cuts through the clutter, enabling swift, confident decision-making.
The Cost of Noise: Why Traditional Threat Data Fails
Many organizations rely on a broad array of threat data sources. While quantity might seem beneficial, a lack of quality often leads to “alert fatigue.” Analysts spend valuable time investigating false positives or low-priority alerts, diverting resources from genuine threats. This inefficiency directly inflates SOC operational costs, as more personnel are needed to manage the volume, and critical incidents might be missed amidst the noise. The core issue isn’t a lack of data, but a lack of actionable intelligence.
What Defines High-Confidence Threat Intelligence?
Optimizing SOC costs with better threat intelligence hinges on specific characteristics that transform raw data into actionable insights:
- High Fidelity: This refers to the accuracy and reliability of the intelligence. High-fidelity intelligence minimizes false positives, ensuring that alerts are more likely to represent genuine threats. It directly reduces the time and resources spent on investigating non-issues.
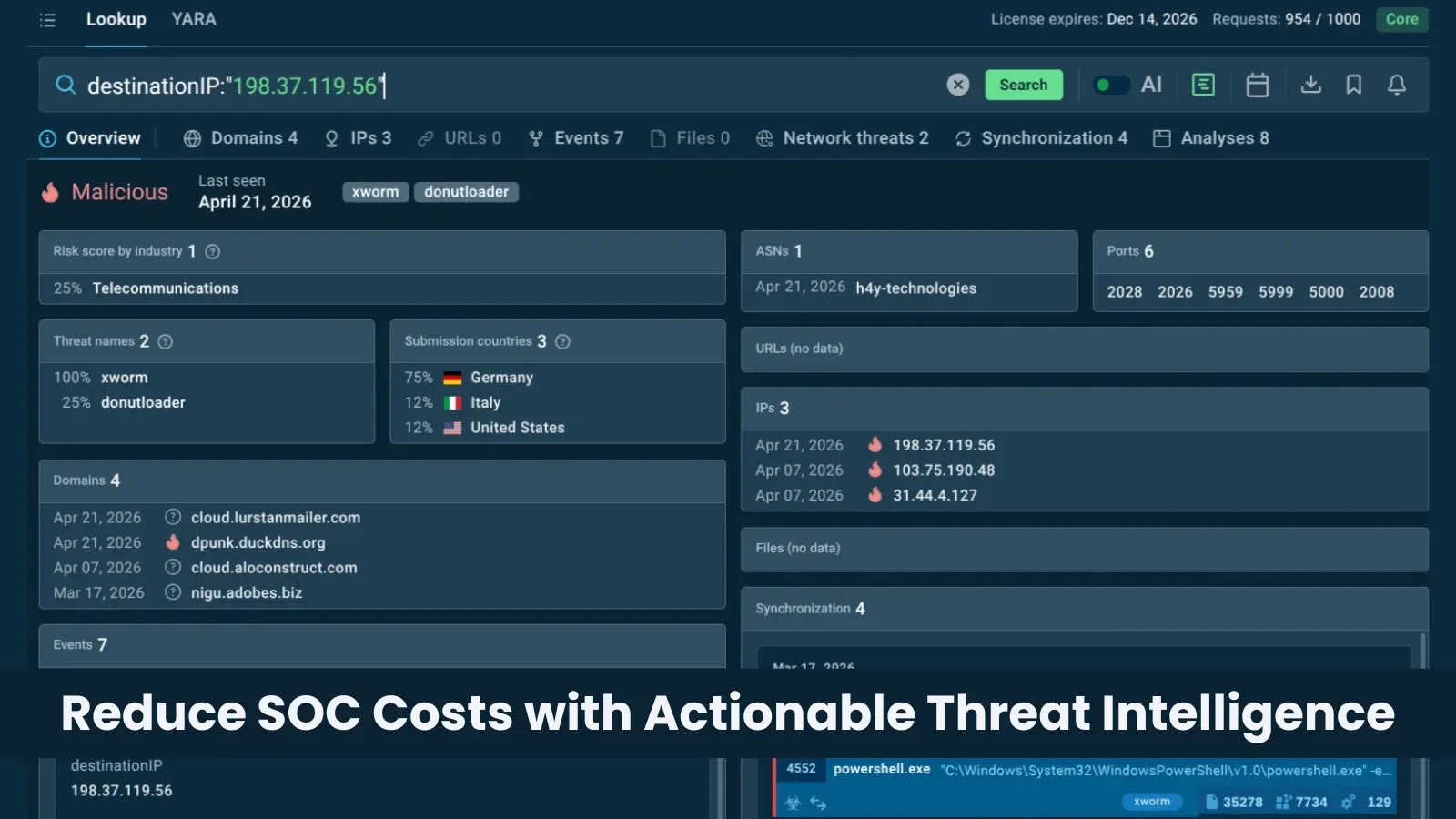
- Contextual: Effective threat intelligence provides context. It’s not just an IP address; it’s an IP address known to be associated with a specific, active campaign targeting your industry, or a particular malware family. This context allows analysts to quickly understand the severity and relevance of a threat, streamlining triage and investigation processes.
- Actionable: The intelligence must directly inform security actions. This means providing indicators of compromise (IOCs) that can be immediately blocked, detections that can be implemented in SIEMs, or playbooks that can be executed. Actionable intelligence reduces the cognitive load on analysts, allowing for faster response times.
Not all threat data sources meet these critical criteria. The difference in quality profoundly impacts the efficiency of investigations and the overall cost structure of the SOC.
Improving Triage Starts at the Source
The journey to a “low noise, high confidence” SOC begins by scrutinizing the sources of threat intelligence. Inefficient processes often stem from poor-quality inputs. Consider these improvements:
- Prioritize Reputable Feeds: Invest in commercial or open-source threat intelligence feeds known for their accuracy, relevance, and timeliness. Evaluate providers based on their methodologies for generating and verifying intelligence.
- Tailor to Your Environment: Generic threat intelligence has limited value. Focus on intelligence relevant to your industry, geographic location, and specific technology stack. This personalization significantly reduces irrelevant alerts.
- Integrate and Automate: Integrate threat intelligence directly into your security tools (SIEM, SOAR, EDR). Automate the ingestion, correlation, and initial triage of alerts based on this intelligence. This reduces manual effort and accelerates response.
- Leverage Community and Peer Sharing: Participate in information sharing and analysis centers (ISACs) or industry-specific groups. Shared intelligence from peers facing similar threats can be highly valuable and contextual.
Remediation Actions for Cost-Effective SOC Operations
To truly optimize SOC costs and achieve high confidence in your threat landscape, implement these strategic remediation actions:
- Regularly Audit Threat Intelligence Sources: Periodically review the performance of your threat intelligence feeds. Track false positive rates and the proportion of actionable alerts. Discard or deprioritize sources that consistently generate noise.
- Develop Strong Playbooks and Automation: For common threat types identified by high-fidelity intelligence, create automated playbooks within your SOAR platform. This ensures consistent, rapid response without constant manual intervention.
- Invest in Analyst Training: Equip your SOC analysts with the skills to effectively interpret, prioritize, and act upon high-quality threat intelligence. Training should cover not just tools, but also threat actor methodologies and kill chain analysis.
- Implement a Feedback Loop: Establish a continuous feedback loop between your security operations team and your threat intelligence team (if separate). Analysts on the front lines can provide invaluable insights into the usefulness and relevancy of intelligence.
- Utilize MITRE ATT&CK Framework: Map your threat intelligence and detection capabilities to the MITRE ATT&CK framework. This helps in identifying gaps in coverage and ensures that your intelligence addresses specific adversary tactics and techniques.
Conclusion
Building a high-performing and cost-effective SOC is not about eliminating alerts; it’s about eliminating unnecessary work and focusing resources where they matter most. By prioritizing high-fidelity, contextual, and actionable threat intelligence, organizations can significantly reduce operational overhead, improve incident response times, and gain superior confidence in their defensive posture. The strategic shift from merely consuming threat data to operationalizing meaningful threat intelligence is paramount for any modern security operation aiming for efficiency and resilience.





