macOS Malware Leverages Google Ads and Legitimate Claude.ai Shared Chats to Deliver Malware
macOS Malware Leverages Google Ads and Legitimate Claude.ai Shared Chats for Delivery
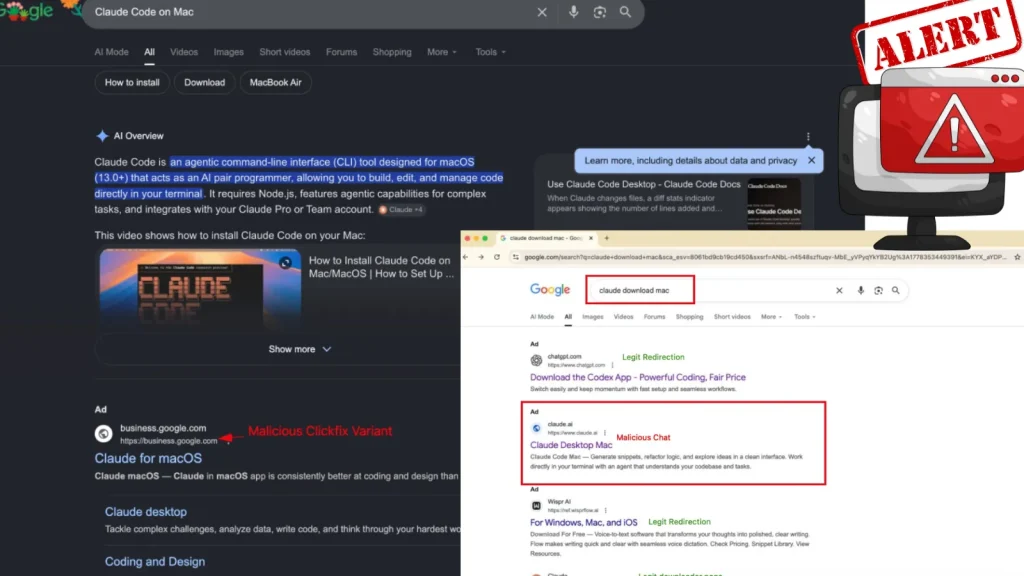
In a concerning development for Apple users, threat actors are deploying a sophisticated malvertising campaign, employing poisoned Google Ads and deceptive artificial intelligence applications to distribute malware on macOS. This operation bypasses traditional security measures by co-opting trusted platforms, presenting a significant challenge for detection and prevention. Recent investigations have uncovered how these attackers are redirecting unsuspecting victims to fraudulent landing pages through sponsored search results, all while leveraging legitimate tools to further their malicious goals.
The Malvertising Campaign: A Deceptive Entry Point
The core of this attack hinges on malvertising, a technique where malicious advertisements are used to spread malware. Threat actors are purchasing ad space on prominent platforms like Google, ensuring their malicious links appear at the top of search results for popular queries. This tactic tricks users into believing they are accessing legitimate software or services, when in reality, they are clicking on a doorway to compromise. The initial point of contact is often a seemingly innocuous ad, designed to lure users seeking specific software or information, particularly those related to AI applications.
Clickfix Social Engineering and Impersonation
Once a victim clicks on a poisoned Google Ad, they are subjected to a sophisticated social engineering technique known as “Clickfix.” This method often involves presenting a series of fake errors or requiring additional, seemingly benign actions from the user, all designed to gain their trust and compliance. Attackers are also heavily relying on impersonation, mimicking legitimate software downloads or updates. For macOS users, this often involves presenting a fake installer that closely resembles a genuine Apple installer, complete with familiar branding and progress bars. The goal is to bypass the user’s skepticism and encourage them to proceed with the installation.
Leveraging Legitimate Claude.ai Shared Chats
One of the more alarming aspects of this campaign is the abuse of legitimate platforms for payload delivery. Researchers have observed attackers utilizing shared chats from artificial intelligence services like Claude.ai. This innovative approach allows threat actors to host malicious links or instructions within a trusted and seemingly benign environment. By sharing a chat conversation that appears to offer helpful information or solutions, the attackers can subtly guide victims towards the malicious payload without raising immediate red flags. This further complicates detection, as security solutions may struggle to differentiate between legitimate and malicious content when both are hosted on reputable services.
The MacSync Payload: What It Is and Its Capabilities
The ultimate goal of this intricate malvertising and social engineering effort is to deliver the MacSync payload. While the specific functionalities of MacSync can vary, typical macOS malware of this nature often aims to achieve:
- Data Exfiltration: Stealing sensitive information such as login credentials, financial data, and personal files.
- Remote Access: Establishing a backdoor for persistent access to the compromised system.
- Spyware Capabilities: Monitoring user activities, taking screenshots, or recording audio/video.
- System Modification: Altering security settings, installing additional malware, or disrupting normal system operation.
The MacSync payload is designed to operate stealthily, often employing obfuscation techniques to evade detection by antivirus software. Its ability to persist on the system allows attackers long-term access and control.
Remediation Actions
Mitigating the risk of falling victim to such sophisticated macOS malware campaigns requires a multi-layered approach. Users and organizations must adopt robust cybersecurity practices.
- Exercise Extreme Caution with Google Ads: Always verify the legitimacy of a website before downloading software, even if it appears in sponsored search results. Directly navigate to official vendor websites instead of clicking on search ads.
- Scrutinize Downloaded Files: Before opening or running any downloaded file, especially those from unfamiliar sources, inspect its origin and verify its authenticity. macOS Gatekeeper and XProtect offer some protection, but user vigilance is paramount.
- Implement Advanced Endpoint Detection and Response (EDR): EDR solutions can provide valuable visibility into endpoint activities, helping to detect and prevent malicious processes associated with malware like MacSync.
- Regularly Update macOS and All Software: Keep your operating system and all applications patched to the latest versions. Updates often include critical security fixes that address known vulnerabilities.
- Employ a Robust Antivirus/Anti-Malware Solution: While no solution is foolproof, a reputable security suite can offer a significant layer of defense against known malware signatures and behavioral anomalies.
- Educate Users on Social Engineering Tactics: Awareness training is crucial. Users should be educated about common social engineering techniques, such as the “Clickfix” method, and the dangers of clicking suspicious links or downloading software from unverified sources.
- Backup Data Regularly: In the event of a successful compromise, having recent backups can significantly reduce the impact of data loss or ransomware attacks.
Conclusion
The ongoing malvertising campaign targeting macOS users, leveraging poisoned Google Ads and legitimate platforms like Claude.ai for delivery, underscores the evolving threat landscape. Threat actors are continually refining their tactics, combining technical sophistication with psychological manipulation to bypass security defenses. Staying informed about these threats and implementing comprehensive security measures are essential for protecting against these increasingly stealthy and effective attacks.





