node-ipc npm Package with 822K Weekly Downloads Compromised in Supply Chain Attack
Unpacking the Latest Compromise: Node-ipc Package Hit Again in Supply Chain Attack
The digital supply chain continues to be a fertile ground for sophisticated attacks, and the recent compromise of the popular node-ipc npm package serves as a stark reminder of these persistent threats. With over 822,000 weekly downloads, node-ipc is a critical component in countless JavaScript projects, facilitating inter-process communication. Its widespread adoption makes any compromise a significant concern for developers and security teams alike.
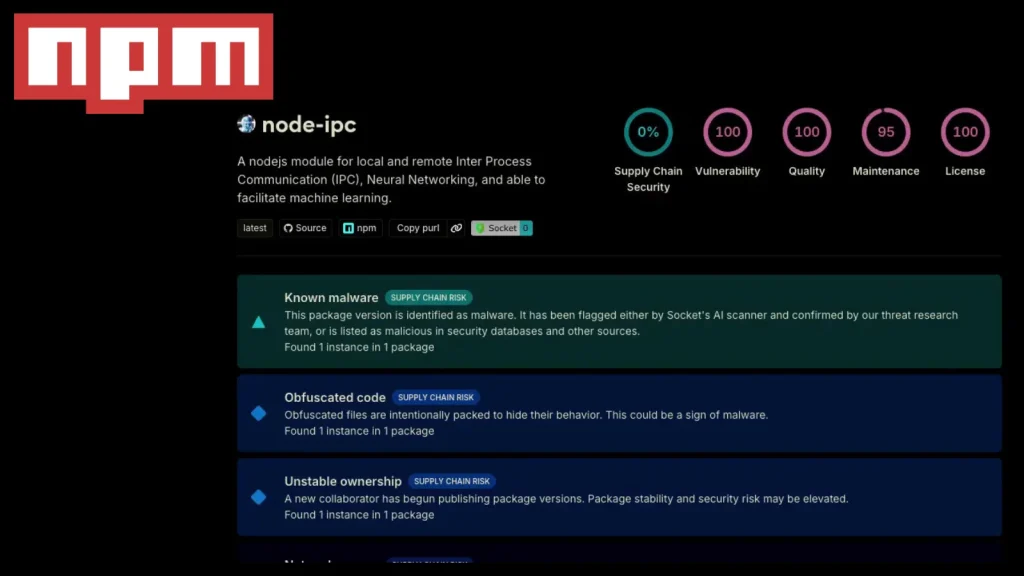
This incident, confirmed by Socket and Stepsecurity, highlights a concerning trend: this is the second major supply chain compromise for the node-ipc package since 2022. The malicious actors have injected obfuscated stealer and backdoor payloads into new versions, demonstrating a continued focus on capitalizing on open-source dependencies. Understanding the intricacies of this attack is crucial for safeguarding your projects and infrastructure.
Understanding the Node-ipc Compromise
The core of this latest attack lies in three specific versions of the node-ipc package: node-ipc@9.1.6, node-ipc@9.2.3, and additional versions identified in subsequent analysis. These versions were found to contain highly obfuscated malicious code designed to steal sensitive information and provide unauthorized backdoor access. The use of obfuscation is a common tactic employed by attackers to evade detection by static analysis tools and human review.
Supply chain attacks like this exploit trust in open-source ecosystems. Developers often integrate third-party packages without a deep dive into their underlying code, relying on the community’s vetting process. When a widely used package is compromised, the malicious code can propagate quickly through the dependency tree, affecting numerous applications and organizations downstream.
The Anatomy of the Attack: Stealer and Backdoor Payloads
The payloads identified within the compromised node-ipc versions are particularly insidious. A stealer payload is designed to exfiltrate sensitive data from the compromised system. This could include environment variables, configuration files, credentials, cryptographic keys, or proprietary source code. The exact nature of the data targeted would depend on the implementation of the stealer and the context in which the affected software is running.
Simultaneously, the presence of a backdoor payload indicates an attacker’s intent to maintain persistent access to compromised systems. A backdoor provides a covert means for attackers to execute arbitrary commands, download additional malware, or pivot to other systems within a network. This type of compromise can lead to long-term control over affected environments, making detection and remediation more challenging.
The obfuscation techniques used further complicate analysis. Attackers often employ techniques like string encoding, dead code insertion, and control flow flattening to make the malicious code appear benign or difficult to reverse-engineer. This allows the compromised code to potentially bypass automated security checks during package installation or deployment.
Previous Incidents and the Broader Context
The fact that this is the second major compromise of node-ipc since 2022 underscores a critical vulnerability in the open-source software supply chain. The previous incident, which involved politically motivated destructive payloads, highlighted the potential for non-financial motivations behind such attacks. This recent discovery, however, points towards more traditional cybercrime objectives: data theft and persistent access.
These recurring compromises serve as a potent example of how attackers are increasingly targeting popular libraries and packages. The vast reach of such dependencies means that a single successful compromise can have a cascading effect across the development community and ultimately impact end-users.
Remediation Actions for Developers and Organizations
Immediate action is required to mitigate the risks posed by this compromise. Developers and organizations must prioritize identifying and addressing any instances of the affected node-ipc versions within their projects.
- Identify Affected Versions: Scan your project dependencies for the compromised versions:
node-ipc@9.1.6,node-ipc@9.2.3, and any other versions confirmed to contain malicious code. Tools likenpm audit,yarn audit, or specialized software composition analysis (SCA) solutions can assist in this process. - Isolate and Remove: If affected versions are found, immediately isolate the compromised code. The safest course of action is to remove the malicious dependency and revert to a known good, uncompromised version or find an alternative package. If no clean update is available, consider temporarily freezing deployments until a secure version is released.
- Scan for Payloads: Conduct thorough scans of any systems where the affected applications were deployed for signs of the stealer or backdoor payloads. Look for unusual network activity, newly created files, or unauthorized processes.
- Review and Rotate Credentials: Given the nature of stealer payloads, assume that any credentials or sensitive information accessible by the compromised application might have been exfiltrated. Promptly review and rotate all API keys, database credentials, server passwords, and any other sensitive access tokens.
- Implement Supply Chain Security Best Practices:
- Software Composition Analysis (SCA): Integrate SCA tools into your CI/CD pipeline to continuously monitor dependencies for known vulnerabilities and malicious packages.
- Dependency Pinning: Pin specific versions of dependencies to prevent automatic updates to potentially compromised versions. Regularly review and update these pinned versions after careful vetting.
- Registry Integrity Checks: Utilize tools that verify the integrity of packages downloaded from npm or other registries.
- Least Privilege: Ensure that build environments and deployment pipelines operate with the principle of least privilege.
- Multi-Factor Authentication (MFA): Implement MFA for all developer accounts and access to package registries.
Recommended Tools for Detection and Mitigation
Leveraging the right tools is essential for maintaining robust supply chain security. Here are some categories and examples:
| Tool Category | Purpose | Link (Example) |
|---|---|---|
| Software Composition Analysis (SCA) | Identifies vulnerabilities and policy violations in open-source dependencies. | Sonatype Nexus Lifecycle |
| Dependency Auditing | Scans project dependencies for known vulnerabilities and malicious packages. | npm audit |
| Runtime Application Self-Protection (RASP) | Monitors and protects applications during runtime against attacks. | Contrast Security RASP |
| Endpoint Detection and Response (EDR) | Detects and investigates suspicious activity on host endpoints. | CrowdStrike Falcon Insight |
Protecting Your Software Supply Chain: A Continuous Effort
The recurring compromise of the node-ipc package serves as a powerful reminder that vigilance in software supply chain security is not a once-off task but a continuous process. Adopting a proactive security posture, combining robust tools with diligent development practices, is essential. Regularly updating dependencies, scrutinizing package provenance, and implementing comprehensive security controls throughout the development lifecycle are non-negotiable steps in protecting your applications from these evolving threats.





