AI Router Vulnerabilities Allow Attackers to Inject Malicious Code and Steal Sensitive Data
Unmasking the Silent Threat: AI Router Vulnerabilities That Hijack Your Data
The rise of AI agents promises unparalleled automation, from managing complex cloud infrastructure to executing financial transactions. However, a critical and largely overlooked attack surface has emerged: third-party AI routers. These intermediary services, vital for AI agent functionality, are becoming potent weapons in the hands of malicious actors. This article delves into how vulnerabilities within these AI routers can be weaponized to silently hijack tool calls, drain cryptocurrency wallets, and exfiltrate sensitive credentials at scale, posing a significant threat to organizations relying on AI agent ecosystems.
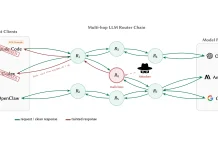
The Critical Role of AI Routers in the AI Agent Ecosystem
AI agents, designed to automate high-stakes tasks, frequently rely on external tools and APIs to perform their operations. AI routers act as the crucial intermediaries, directing these tool calls and managing the flow of information between the AI agent and the external services. They parse requests, route them appropriately, and often handle authentication and data formatting. This central role makes them a prime target for attackers, as compromising an AI router grants control over the AI agent’s interactions with its environment.
How Attackers Exploit AI Router Vulnerabilities
The primary vector for these attacks lies in manipulating the instructions an AI router interprets or executes. By injecting malicious code or malformed requests, attackers can trick the router into:
- Hijacking Tool Calls: Instead of the AI agent communicating with its intended, legitimate tool, the router can be redirected to a malicious endpoint controlled by the attacker. This allows for interception and manipulation of data, or even the execution of arbitrary code within the AI agent’s environment.
- Exfiltrating Sensitive Data: Compromised routers can be leveraged to siphon off sensitive information, including API keys, authentication tokens, user data, and proprietary business logic, that the AI agent processes or has access to.
- Draining Cryptocurrency Wallets: For AI agents involved in financial transactions, a hijacked router can redirect cryptocurrency transfers to attacker-controlled wallets, leading to significant financial losses.
- Gaining Persistent Access: Once compromised, AI routers can serve as a persistent backdoor, allowing attackers to maintain access and control over the AI agent’s operations and its broader environment.
The Anatomy of an AI Router Attack: A Silent Compromise
Unlike traditional network attacks that might trigger immediate alerts, AI router vulnerabilities enable a more insidious form of compromise. The attacks often appear as legitimate tool calls or API interactions from the perspective of the AI agent, making detection challenging. The attacker effectively “speaks the language” of the AI agent’s operations, manipulating the intermediary layer to achieve their objectives without direct detection by the AI agent itself. This silent weaponization makes these vulnerabilities particularly dangerous, as the breach may go undiscovered for long periods, leading to extensive damage.
Remediation Actions: Securing Your AI Agent Ecosystem
Proactive measures are essential to mitigate the risks associated with AI router vulnerabilities. Organizations must prioritize robust security practices to protect their AI agent deployments:
- Thorough Vendor Security Assessments: Before integrating any third-party AI router, conduct comprehensive security audits of the vendor. Scrutinize their security architecture, patching policies, and incident response capabilities.
- Input Validation and Sanitization: Implement strict input validation and sanitization at every stage of the AI agent’s interaction with the router. Ensure that all incoming data, especially from external sources, is checked for malicious payloads or unexpected formats.
- Least Privilege Principle: Configure AI routers and the tools they interact with to operate with the absolute minimum necessary privileges. This limits the potential damage an attacker can inflict if a compromise occurs.
- Network Segmentation and Microsegmentation: Isolate AI agent environments and routers from other critical systems using network segmentation. Consider microsegmentation to restrict communications strictly to what is necessary for operations.
- Continuous Monitoring and Anomaly Detection: Implement robust logging and monitoring solutions for AI router activity. Look for anomalous patterns, unusual tool calls, or unexpected data flows that could indicate a compromise.
- API Security Gateways: Employ API security gateways to enforce access control, rate limiting, and threat detection for all API interactions involving the AI router.
- Regular Security Audits and Penetration Testing: Conduct regular security audits and penetration tests specifically targeting your AI agent ecosystem, including the AI routers, to identify and address vulnerabilities before they can be exploited.
Tools for Detection and Mitigation
While specific tools for AI router vulnerability scanning are emerging, several established cybersecurity tools can aid in detection and mitigation:
| Tool Name | Purpose | Link |
|---|---|---|
| OWASP ZAP | Web application security scanner; useful for API fuzzing and identifying common web vulnerabilities that might affect router interfaces. | https://www.zaproxy.org/ |
| Burp Suite Professional | Integrated platform for performing security testing of web applications, including API inspection and manipulation. | https://portswigger.net/burp |
| SIEM Solutions (e.g., Splunk, Elastic Stack) | Centralized logging and security event management; critical for correlating logs from AI routers and associated systems to detect anomalies. | https://www.splunk.com/ |
| API Security Gateways (e.g., Kong, Apigee) | Provides access control, threat protection, and policy enforcement for API traffic. | https://konghq.com/ |
The Path Forward: Securing the Future of AI Automation
The vulnerabilities in AI routers represent a critical, yet often overlooked, attack surface in the expanding landscape of AI agent deployment. As AI agents continue to undertake more sensitive and high-value tasks, the security of their underlying infrastructure, particularly the intermediary routers, becomes paramount. Organizations must adopt a proactive and comprehensive security strategy, focusing on thorough vendor assessment, stringent input validation, the principle of least privilege, and continuous monitoring. Only by addressing these foundational security gaps can we truly secure the promise of AI automation and prevent malicious actors from silently compromising our most advanced systems.