Authorities Disrupt IoT Botnet Infrastructure Behind Record-Breaking 30 Tbps DDoS Attacks
The digital battlefield just saw a significant victory for cybersecurity, as authorities successfully dismantled the command-and-control (C2) infrastructure behind four colossal Internet of Things (IoT) botnets. This operation, spearheaded by the U.S. Justice Department in close collaboration with Canadian and German agencies, targeted the administrators and critical architecture underpinning the Aisuru, KimWolf, JackSkid, and Mossad botnets. These sophisticated networks collectively infected over three million devices worldwide, launching Distributed Denial of Service (DDoS) attacks reaching an unprecedented 30 Terabits per second (Tbps).
The Anatomy of a 30 Tbps Threat: Understanding IoT Botnets
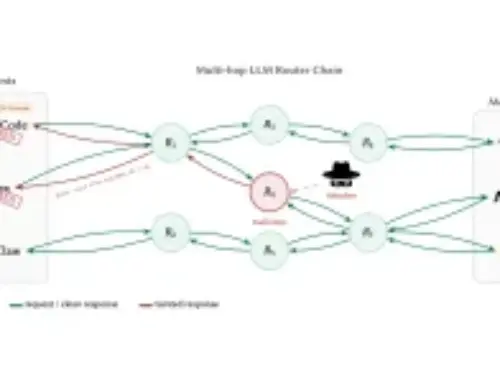
IoT botnets represent a particularly insidious threat due to their ability to weaponize countless vulnerable internet-connected devices. From smart home gadgets to industrial sensors, these devices often possess weak security protocols, making them easy targets for compromise. Once infected, they become “bots” – enslaved components of a larger network, silently awaiting commands from their operators. The Aisuru, KimWolf, JackSkid, and Mossad botnets exemplified this threat model, leveraging millions of compromised devices to unleash crippling DDoS attacks.
A DDoS attack overwhelms a target server or network with a flood of traffic, rendering it inaccessible to legitimate users. A 30 Tbps attack is a staggering figure, capable of bringing down even the most robust online infrastructures. The sheer scale of these botnets – controlling over three million devices – underscores the critical importance of securing every connected endpoint.
International Collaboration: A Takedown in Action
The successful disruption of these botnets highlights the growing effectiveness of international law enforcement cooperation in combating cybercrime. The collaborative efforts between the U.S. Justice Department, Canadian, and German agencies were crucial in identifying the C2 infrastructure, tracing the botnet operators, and ultimately neutralizing their capabilities. This multi-jurisdictional approach is increasingly vital given the borderless nature of cyber threats.
By targeting the C2 infrastructure, authorities effectively severed the communication lines between the botnet operators and the compromised devices. This action renders the botnet inoperable, as the “bots” can no longer receive commands or participate in attacks. This type of intervention is a temporary reprieve, however, as the underlying vulnerabilities in the infected devices often remain. For instance, many IoT devices are susceptible to known vulnerabilities, such as default credentials or unpatched firmware. While specific CVEs for the botnet’s initial compromise vectors were not detailed in the source, common IoT vulnerabilities often include issues like CVE-2019-11531 (affecting certain D-Link devices) or general weaknesses related to older Linux kernels often found embedded in IoT devices like those impacted by CVE-2021-4034 (PwnKit).
Remediation Actions for IoT Device Owners
While the C2 infrastructure has been dismantled, the millions of compromised devices remain a potential vector for future attacks if not properly secured. Device owners play a crucial role in preventing their devices from being re-infected or used in other botnets. Here are essential remediation actions:
- Change Default Credentials: Immediately change all default usernames and passwords on every IoT device. Use strong, unique passwords.
- Update Firmware Regularly: Keep device firmware updated to the latest version provided by the manufacturer. These updates often include critical security patches for known vulnerabilities.
- Network Segmentation: If possible, segment your IoT devices onto a separate network (e.g., guest network or dedicated IoT VLAN) to limit their access to your main network.
- Disable Unused Services: Turn off any services or features on your IoT devices that you do not actively use. This reduces the attack surface.
- Use a Strong Router Password and Firewall: Ensure your home or business router has a strong, unique password and a properly configured firewall.
- Monitor Network Traffic: Implement basic network monitoring to detect unusual outgoing traffic from your IoT devices, which could indicate compromise.
- Purchase from Reputable Manufacturers: Prioritize IoT devices from manufacturers with a strong reputation for security and regular software updates.
The Ongoing Battle Against Cybercrime
The takedown of the Aisuru, KimWolf, JackSkid, and Mossad botnets is a significant achievement, but it’s a stark reminder of the persistent and evolving threat landscape. Cybercriminals are constantly seeking new ways to exploit vulnerabilities and weaponize internet-connected devices. This operation underscores the need for continuous vigilance, proactive security measures, and robust international cooperation.
Incident response teams and cybersecurity professionals must remain abreast of emerging threats and develop strategies to not only disrupt attacks but also to educate the public on securing their digital footprint. As our world becomes increasingly interconnected, the security of every single device contributes to the overall resilience of the internet.