CISA Urges Organizations to Secure Microsoft Intune Environments Following Stryker Breach
CISA Urges Organizations to Secure Microsoft Intune Environments Following Stryker Breach
The digital landscape is a constant battleground, and even the most robust organizations can fall victim to sophisticated cyberattacks. A recent incident involving Stryker Corporation, a leading U.S. medical technology firm, serves as a stark reminder of this reality. On March 11, 2026, Stryker experienced a significant cyberattack targeting its Microsoft environment, prompting an urgent alert from the U.S. Cybersecurity and Infrastructure Security Agency (CISA).
CISA, in coordination with the Federal Bureau of Investigation (FBI), is now strongly advising organizations to harden their endpoint management system configurations, particularly within Microsoft Intune environments. This incident underscores the critical importance of a proactive and vigilant approach to endpoint security.
The Stryker Breach: A Wake-Up Call for Endpoint Security
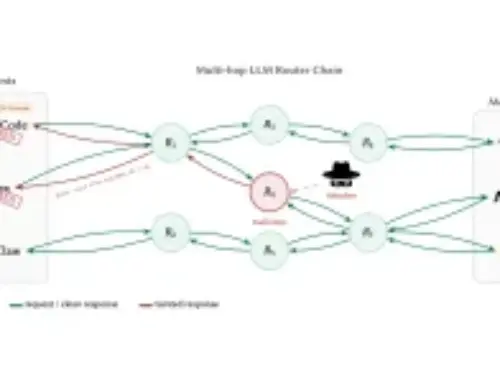
While specific details of the Stryker breach remain under wraps, the fact that CISA has issued a widespread alert points to the severity and potential implications of the attack. Targeting a Microsoft environment, the incident highlights a common attack vector: compromising endpoint management systems to gain broader network access or deploy malicious payloads.
Microsoft Intune, a cloud-based unified endpoint management (UEM) solution, is widely adopted for managing and securing devices and applications. While powerful, its pervasive nature makes it an attractive target for threat actors. A misconfigured or insufficiently secured Intune environment can open doors to significant vulnerabilities, allowing attackers to:
- Gain unauthorized access to sensitive data.
- Distribute malware across an organization’s devices.
- Exfiltrate critical intellectual property.
- Disrupt business operations.
Why Microsoft Intune Environments are Prime Targets
Endpoint management solutions like Microsoft Intune are central to an organization’s IT infrastructure. They manage user identities, device compliance, application deployments, and security policies. Compromising such a system can provide an attacker with a “skeleton key” to an organization’s digital assets. Attackers often exploit common weaknesses, including:
- Weak Authentication: Lack of multi-factor authentication (MFA) or reliance on easily guessable credentials.
- Misconfigured Policies: Overly permissive access controls or incomplete security policies.
- Outdated Software: Unpatched vulnerabilities in the Intune client or integrated applications.
- Lack of Monitoring: Insufficient logging and alerting for anomalous activities within the Intune console.
Remediation Actions and Best Practices for Securing Intune
CISA’s urgent alert is a call to action. Organizations must immediately review and fortify their Microsoft Intune configurations. Here are crucial steps to take:
- Implement Multi-Factor Authentication (MFA) Everywhere: Enforce MFA for all administrative accounts and, ideally, for all user accounts accessing Intune-managed resources. This dramatically reduces the risk of credential compromise.
- Enforce Strong Device Compliance Policies: Configure Intune to ensure devices meet stringent security requirements before gaining access to corporate resources. This includes requiring up-to-date operating systems, antivirus software, and encryption.
- Leverage Conditional Access: Implement Conditional Access policies to restrict access based on user location, device health, and application. This ensures users can only access resources from trusted locations and devices.
- Regularly Review and Audit RBAC: Scrutinize Role-Based Access Control (RBAC) assignments within Intune. Grant only the minimum necessary permissions to users and administrators. Regularly audit these assignments to remove unnecessary privileges.
- Patch and Update Religiously: Keep all operating systems, applications, and endpoint protection solutions up to date. While Intune itself is a cloud service, client-side vulnerabilities can still be exploited.
- Strengthen Endpoint Detection and Response (EDR): Integrate Intune with robust EDR solutions. Ensure all endpoints have EDR agents deployed and configured for proactive threat detection and response.
- Implement Advanced Threat Protection: Utilize Microsoft Defender for Endpoint and other advanced threat protection features within the Microsoft ecosystem to detect and block sophisticated attacks.
- Monitor Intune Activity Logs: Regularly review audit logs within Intune for unusual activity, unauthorized policy changes, or suspicious device enrollments. Integrate these logs with your Security Information and Event Management (SIEM) system.
- Educate Users: Implement ongoing security awareness training for all employees, emphasizing phishing prevention and the importance of reporting suspicious activities.
Tools for Detection and Mitigation
Effective security relies on the right tools. Here are some essential tools relevant to securing Microsoft Intune environments:
| Tool Name | Purpose | Link |
|---|---|---|
| Microsoft Defender for Endpoint | Endpoint Detection and Response (EDR) and advanced threat protection | Microsoft Defender for Endpoint |
| Azure AD Connect Health | Monitors identity infrastructure, including sync services and AD FS | Azure AD Connect Health |
| Microsoft 365 Defender | Unified security suite across endpoints, identities, email, and apps | Microsoft 365 Defender |
| Azure AD Identity Protection | Automated detection and remediation of identity-based risks | Azure AD Identity Protection |
| Log Analytics (Azure Monitor) | Collects, analyzes, and acts on telemetry data from your cloud and on-premises environments | Log Analytics |
Key Takeaways
The Stryker breach and CISA’s subsequent alert highlight an undeniable truth: endpoint management systems are prime targets for cyberattacks. Proactive security measures, continuous monitoring, and adherence to best practices are not optional but essential. Organizations must leverage the robust security features available within Microsoft Intune and the broader Microsoft 365 ecosystem. By hardening configurations, enforcing strong authentication, and maintaining vigilance, organizations can significantly reduce their attack surface and protect their critical assets from evolving cyber threats.