Copyright-Themed Lures Deliver Multi-Stage PureLog Stealer in New Credential Theft Campaign
The Deceptive Lure of Copyright: Unpacking the PureLog Stealer Campaign
In a world increasingly reliant on digital assets, the specter of copyright infringement looms large. Threat actors are now weaponizing this concern, weaving intricate social engineering schemes to deliver sophisticated credential-stealing malware. A recent and concerning campaign leverages fake copyright violation notices to distribute PureLog Stealer, a multi-stage information stealer that has already begun compromising organizations across critical sectors, including healthcare, government, education, and hospitality.
First analyzed in March 2026, this campaign highlights a disturbing evolution in cybercrime tactics. Attackers are exploiting perceived legal threats to bypass traditional security measures and trick victims into executing malicious payloads. This blog post will delve into the mechanics of this cunning campaign, explain the dangers of PureLog Stealer, and provide actionable advice for protecting your organization.
The Anatomy of Deception: How the Campaign Unfolds
The core of this attack lies in its clever social engineering. Victims receive what appears to be a legitimate copyright violation notice. These notices are crafted to invoke a sense of urgency and fear, prompting recipients to open an attached or linked file for more details. However, this seemingly innocuous legal document is, in fact, a malicious executable.
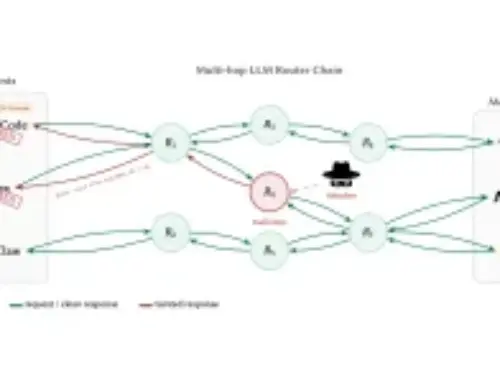
Upon execution, the file initiates a multi-stage infection process designed to evade detection and establish persistence. This staged approach allows PureLog Stealer to gradually reveal its capabilities, making it harder for endpoint detection and response (EDR) systems to identify the full scope of the threat immediately.
PureLog Stealer: A Potent Credential Thief
PureLog Stealer is not a new player in the threat landscape, but its integration into this copyright-themed campaign signifies a renewed and dangerous focus on credential theft. This malware is engineered to exfiltrate a wide array of sensitive information, including:
- Browser Passwords: Credentials saved in popular web browsers.
- Session Cookies: Data that can be used to hijack active user sessions.
- Credit Card Information: Stored financial details.
- VPN Credentials: Access to an organization’s internal network.
- Cryptocurrency Wallet Data: Private keys and wallet information.
- Operating System Information: System details that can aid further exploitation.
The successful deployment of PureLog Stealer can lead to significant data breaches, financial losses, and widespread operational disruption. The exfiltrated credentials can be used for secondary attacks, lateral movement within a compromised network, or sold on dark web marketplaces.
Targeted Sectors and Broader Implications
The campaign’s targeting of healthcare, government, education, and hospitality sectors is particularly alarming. These industries often handle vast amounts of personally identifiable information (PII) and sensitive data, making them prime targets for credential theft. A breach in any of these sectors can have far-reaching consequences, impacting patient privacy, national security, academic integrity, and customer trust.
The nature of the lure – a copyright violation – has broad appeal. Anyone from a small business owner to a large corporation could potentially receive such a notice, making the attack surface incredibly wide. This universal applicability increases the campaign’s potential for success and underscores the need for robust cybersecurity defenses across all organizational sizes and types.
Remediation Actions and Proactive Defense
Defending against sophisticated social engineering campaigns like this requires a multi-layered approach. Organizations must prioritize both technical controls and comprehensive employee education.
- Employee Training: Conduct regular security awareness training emphasizing the dangers of phishing, social engineering, and unexpected email attachments. Employees should be trained to scrutinize all unsolicited communication, especially those purporting to be legal notices.
- Email Filtering and Sandboxing: Implement advanced email filtering solutions that can detect and block malicious attachments and URLs. Utilize email sandboxing to safely detonate suspicious attachments in an isolated environment before they reach user inboxes.
- Endpoint Detection and Response (EDR): Deploy EDR solutions capable of detecting and responding to suspicious activities on endpoints, including the execution of unknown binaries and unusual process behavior.
- Multi-Factor Authentication (MFA): Enforce MFA across all critical systems and applications. This significantly reduces the impact of compromised credentials, as even if a password is stolen, the attacker cannot gain access without the second factor.
- Regular Backups: Maintain regular, offsite, and immutable backups of critical data to ensure business continuity in the event of a successful attack or data encryption.
- Patch Management: Keep all operating systems, applications, and security software up to date with the latest security patches to mitigate known vulnerabilities.
- Principle of Least Privilege: Implement the principle of least privilege, ensuring users only have access to the resources absolutely necessary for their job functions.
Tools for Detection and Mitigation
Leveraging the right tools can significantly enhance your organization’s security posture against threats like PureLog Stealer.
| Tool Name | Purpose | Link |
|---|---|---|
| Email Security Gateways (e.g., Proofpoint, Mimecast) | Advanced email filtering, anti-phishing, sandboxing | Proofpoint, Mimecast |
| Endpoint Detection & Response (EDR) (e.g., CrowdStrike, SentinelOne) | Real-time threat detection, incident response, behavioral analysis | CrowdStrike, SentinelOne |
| Security Awareness Training Platforms (e.g., KnowBe4, SANS) | Employee education and phishing simulation | KnowBe4, SANS |
| Threat Intelligence Platforms (e.g., Mandiant Threat Intelligence, IBM X-Force) | Information on adversary tactics, techniques, and procedures (TTPs) | Mandiant, IBM X-Force |
Key Takeaways: Staying Ahead of Creative Cyber Threats
The “copyright-themed lures” campaign delivering PureLog Stealer serves as a stark reminder of the evolving threat landscape. Cybercriminals are constantly adapting their social engineering tactics to exploit human psychology and bypass security controls. Organizations must:
- Be acutely aware of the latest phishing and social engineering trends.
- Invest in robust, layered security defenses that include both technological solutions and human elements.
- Prioritize continuous security awareness training for all employees.
- Assume compromise and implement strong incident response plans.
By understanding the mechanisms of these attacks and implementing proactive security measures, organizations can significantly reduce their risk of falling victim to sophisticated information-stealing campaigns like this one.