Crunchyroll Data Breach — Threat Actor Claims Exfiltration of 100 GB of User Data
A disturbing report has emerged concerning Crunchyroll, the dominant anime streaming platform owned by Sony. A threat actor is claiming to have exfiltrated a significant 100 GB of user data, potentially comprising personally identifiable information (PII). This alleged breach, which purportedly took place on March 12, 2026, highlights the persistent and evolving nature of cyber threats targeting even large, established online services.
The alleged compromise reportedly stemmed from a foothold gained through a compromised employee at Telus, an outsourcing partner of Crunchyroll. As of this writing, Crunchyroll has not publicly acknowledged the incident, leaving users and the cybersecurity community awaiting official confirmation and details.
The Alleged Crunchyroll Data Breach: What We Know So Far
The core information surrounding this incident revolves around a threat actor’s claim of a substantial data exfiltration. Approximately 100 GB of user data is believed to have been compromised. The method of initial access is particularly noteworthy: a compromised employee at Telus, an outsourcing partner to Crunchyroll. This vector underscores the critical importance of supply chain security and the extended attack surface that large organizations face when relying on third-party vendors.
While the exact nature of the PII exfiltrated remains unconfirmed without official statements from Crunchyroll, such breaches often include information like email addresses, usernames, hashed passwords, subscription details, and potentially even payment information (though typically, payment card details are not stored directly by streaming services but handled by payment processors). The date of the alleged breach, March 12, 2026, indicates a relatively recent event, making rapid response and communication crucial.
The PII Threat: Understanding the Risks for Crunchyroll Users
The potential exfiltration of 100 GB of PII poses significant risks for Crunchyroll’s vast user base. PII, when compromised, can be leveraged by malicious actors for various nefarious activities, including:
- Identity Theft: Stolen personal details can be used to open fraudulent accounts, apply for loans, or commit other forms of identity theft.
- Phishing and Spear-Phishing: Attackers can use email addresses and other personal information to craft highly convincing phishing emails, tricking users into revealing further sensitive data or downloading malware.
- Account Takeovers (ATO): If hashed passwords are weak or reused across different services, attackers can attempt to log into other accounts associated with the compromised credentials.
- Doxing: Public exposure of personal information can lead to harassment or other real-world threats.
The involvement of a third-party vendor compromise adds another layer of complexity. Organizations like Crunchyroll often outsource specific functions to leverage specialized expertise and cost efficiencies. However, this also means inheriting the security posture of their partners. A lapse in security at a vendor like Telus can directly impact the primary organization’s data integrity.
Supply Chain Security: The Weakest Link
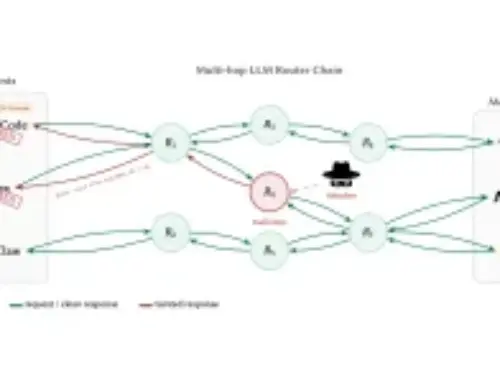
This alleged breach serves as a stark reminder of the vulnerabilities inherent in modern supply chains. The compromise of a third-party vendor, in this case, an outsourcing partner, demonstrates how an organization’s security is only as strong as its weakest link. Attackers increasingly target suppliers and partners as an indirect route into larger, more fortified targets.
- Vendor Risk Management: Robust programs are essential to assess, monitor, and mitigate the cybersecurity risks posed by third-party vendors. This includes regular security audits, contractual obligations for data protection, and clear communication channels during incidents.
- Employee Training and Awareness: The focus on a “compromised employee” at Telus highlights the persistent threat of human error or social engineering. Continuous cybersecurity training and awareness programs are critical for all employees, including those at partner organizations, to recognize and report suspicious activities.
- Least Privilege and Network Segmentation: Granting third-party access based on the principle of least privilege and implementing strong network segmentation can limit the blast radius if an individual or system within the vendor’s environment is compromised.
Remediation Actions for Crunchyroll Users (Proactive Measures)
While Crunchyroll has yet to confirm the breach, proactive measures are always advisable when such claims emerge. Users should consider taking the following steps:
- Change Crunchyroll Password: Immediately update your Crunchyroll password to a strong, unique one if you haven’t recently.
- Enable Two-Factor Authentication (2FA): If Crunchyroll offers 2FA (or multi-factor authentication, MFA), enable it without delay. This adds a crucial layer of security, making it significantly harder for attackers to access your account even with a compromised password.
- Beware of Phishing Attempts: Be exceptionally vigilant for suspicious emails or messages claiming to be from Crunchyroll. Attackers often follow up breaches with targeted phishing campaigns.
- Review Account Activity: Regularly check your Crunchyroll account for any unusual activity or unauthorized changes.
- Monitor Other Accounts: If you use the same or similar passwords for other online services, change those unique passwords immediately. Password reuse is a major vulnerability.
- Use a Password Manager: Employ a reputable password manager to generate and securely store unique, complex passwords for all your online accounts.
The Path Forward: Transparency and Robust Security
This alleged Crunchyroll data breach underscores the ongoing challenges in cybersecurity. For organizations, the incident highlights the critical need for comprehensive supply chain security, continuous vulnerability management, and transparent communication protocols. For users, it’s a reminder that personal vigilance and proactive security practices are paramount in protecting their digital identity. As the situation develops, official communication from Crunchyroll will be essential for users to understand the full scope of the breach and take appropriate, informed actions.