Fake VPN and Spam Blocker Apps Tied to VexTrio Used in Ad Fraud, Subscription Scams
The digital landscape is a minefield of both innovation and deception. For cybersecurity professionals, staying ahead of sophisticated threats is paramount, especially when those threats leverage trusted platforms. Recent observations reveal a disturbing trend: malicious applications, masquerading as essential utilities like VPNs and spam blockers, are infiltrating official app stores to facilitate ad fraud and subscription scams. This insidious operation, tied to the ad tech purveyor VexTrio Viper, underscores a critical vulnerability in our mobile ecosystem.
The VexTrio Viper Apparatus: A Deep Dive
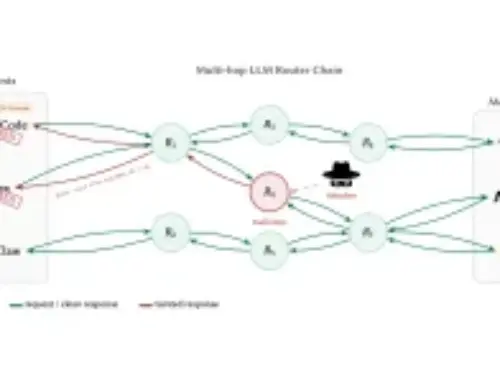
DNS threat intelligence firm Infoblox has shed light on VexTrio Viper’s deceptive tactics. This malicious entity is developing and deploying a suite of harmful applications under the guise of legitimate and seemingly useful tools. These aren’t isolated incidents; they represent a coordinated effort to exploit user trust and bypass app store security mechanisms.
- Masquerading as Essential Utilities: The applications primarily impersonate services users widely seek out. This includes fake VPNs, which promise enhanced privacy and security but deliver compromise, and sham spam blockers, which claim to protect users from unwanted communication while facilitating malicious activity.
- Beyond Security: The deception extends further, encompassing applications that pose as device “monitoring” tools, RAM cleaners for performance enhancement, and even dating services, all designed to lure unsuspecting users.
- Official App Store Infiltration: A critical aspect of VexTrio Viper’s strategy is its success in publishing these malicious apps on both Apple’s App Store and Google Play. This placement on trusted platforms lends an air of legitimacy, making it significantly harder for average users to discern the threat.
The Modus Operandi: Ad Fraud and Subscription Scams
The primary objectives behind these fake applications are ad fraud and subscription scams. Once installed, these apps leverage various techniques to generate illicit revenue:
- Malicious Ad Injection: The apps likely inject unsolicited advertisements, often in pop-up or fullscreen formats, forcing users to interact with them or inadvertently click on them, thereby generating fraudulent ad revenue for the attackers.
- Hidden Subscriptions: Users may be tricked into signing up for recurring, often exorbitant, subscriptions for services that are either non-existent or completely useless. These subscriptions are often difficult to cancel, leading to ongoing financial drain.
- Data Exfiltration (Potential): While the primary focus is ad fraud and scams, such sophisticated operations often include mechanisms for data collection. Users’ personal information, device data, or even more sensitive credentials could be at risk, though specific details on this aspect were not provided in the source.
Remediation Actions and Proactive Defense
Protecting networks and end-users from such pervasive threats requires a multi-layered approach involving both technical controls and user education.
- Enhanced App Store Scrutiny: While major platforms like Apple and Google invest heavily in security, this incident highlights the need for continuous improvement in their app vetting processes, especially for apps mimicking critical security functions.
- Network-Level DNS Filtering: Organizations should implement robust DNS filtering solutions. Services like Infoblox, which identified VexTrio Viper, can block connections to known malicious command-and-control servers or ad fraud domains, regardless of the application initiating the connection.
- Endpoint Detection and Response (EDR): Deploying EDR solutions on all corporate and BYOD mobile devices can help detect and quarantine suspicious app behavior, unauthorized network connections, and data exfiltration attempts.
- User Education and Awareness: A well-informed user base is the first line of defense. Educate employees about the following:
- Skepticism towards “Free” VPNs/Boosters: Emphasize that genuinely secure and reliable VPNs typically come with a cost. Free alternatives often monetize user data or inject ads.
- Verifying App Developer Reputation: Advise users to check developer reviews, website, and other apps before downloading. Look for consistent negative feedback or a lack of credible information.
- Reviewing App Permissions: Encourage users to critically assess the permissions requested by an app. A spam blocker demanding access to photos or contacts should raise immediate red flags.
- Reporting Suspicious Apps: Provide clear internal guidelines for reporting suspicious apps or unusual device behavior.
- Regular Security Audits: Conduct periodic security audits of mobile devices used for corporate access, ensuring they adhere to organizational security policies and are free from known malicious applications.
Tools for Detection and Mitigation
Leveraging appropriate tools is crucial for identifying and mitigating risks associated with malicious mobile applications.
| Tool Name | Purpose | Link |
|---|---|---|
| DNS Filtering Solutions (e.g., Infoblox, Cisco Umbrella) | Block access to known malicious domains associated with ad fraud and C2 servers. | infoblox.com |
| Mobile Threat Defense (MTD) Solutions (e.g., Zimperium, Lookout) | Provide real-time protection for mobile devices against malware, phishing, and network attacks. | zimperium.com |
| Endpoint Detection and Response (EDR) (e.g., CrowdStrike, SentinelOne) | Monitor endpoint and network events for suspicious activity and enable rapid response. | crowdstrike.com |
| App Store Security Guidelines | Information on how app stores review and maintain security standards. | developer.apple.com/app-store/review/guidelines/ |
Conclusion
The emergence of VexTrio Viper’s fake VPNs and spam blockers on official app stores is a Stark reminder of the persistent and evolving nature of cyber threats. It underscores the critical need for vigilance not only from end-users but also from organizations responsible for vetting and distributing applications. By combining robust technical controls, continuous monitoring, and proactive user education, the cybersecurity community can collectively build stronger defenses against these deceptive campaigns and safeguard the integrity of our digital interactions.