Fiber Optic Cables Turned Into Hidden Microphones to Secretly Spy on Your Conversations
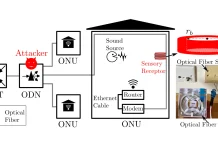
Imagine your critical conversations, the ones you deemed secure within the confines of your office or home, being effortlessly captured by an invisible adversary. Not through a hidden microphone you can sweep for, but through the very infrastructure that connects you to the world: your fiber optic internet cables. This isn’t science fiction; it’s a chilling reality demonstrated by recent research, revealing a sophisticated eavesdropping technique that transforms standard Fiber-to-the-Home (FTTH) telecom fibers into covert acoustic sensors.
This groundbreaking discovery, presented by researchers at NDSS 2026 from The Hong Kong Polytechnic University, The Chinese University of Hong Kong, and the Technological and Higher Education Institute of Hong Kong, highlights a significant, previously unaddressed vulnerability. It exposes how everyday fiber infrastructure can be weaponized for passive, undetectable surveillance, bypassing traditional RF scanning and ultrasonic jamming countermeasures. For cybersecurity professionals, IT managers, and privacy-conscious individuals, understanding this threat is paramount.
The Covert Acoustic Eavesdropping Attack Explained
The core of this exploit lies in the inherent sensitivity of optical fibers to minute physical vibrations. While designed for high-speed data transmission, these fibers are also susceptible to external acoustic waves, such as human speech. When sound waves hit a fiber optic cable, they induce tiny pressure fluctuations that subtly alter the fiber’s refractive index and path length. These changes, in turn, modulate the light signal traveling through the fiber.
Researchers have developed a method to detect and interpret these subtle modulations. By injecting continuous-wave light into the target fiber and analyzing the backscattered or reflected light, they can reconstruct acoustic signals. This technique essentially turns the fiber itself into a distributed acoustic sensor. What makes this particularly insidious is its passive nature: the attacker doesn’t need to inject malicious code or compromise network devices. They simply need access to an endpoint of the fiber, often at a service provider’s distribution hub or even close to the victim’s premises.
Beyond Traditional Eavesdropping: The Undetectable Threat
This method of eavesdropping poses a unique challenge because it operates entirely outside the realm of conventional cybersecurity defenses. Consider these critical aspects:
- Invisible to RF Scanners: Since the mechanism relies on light and physical vibrations within the fiber, there is no electromagnetic radiation to detect. Standard bug sweep equipment focused on RF signals is completely blind to this attack.
- Immune to Ultrasonic Jammers: Ultrasonic jammers work by flooding an area with high-frequency sound waves to disrupt microphone functionality. This attack, however, doesn’t rely on microphones in the traditional sense; the fiber itself is the sensor. Jammers would have no effect on the fiber’s ability to pick up normal speech frequencies.
- Passive and Remote: The attacker doesn’t need to physically enter a compromised location. As long as they can tap into the fiber line at a point accessible to them, often within the telecom infrastructure, they can conduct surveillance remotely.
- Utilizes Existing Infrastructure: The attack leverages the ubiquitous FTTH network, meaning millions of homes and businesses are potentially vulnerable without any additional hardware installation required by the attacker.
This vulnerability, while not yet designated with a public Common Vulnerabilities and Exposures (CVE) identifier, represents a significant paradigm shift in how we must think about physical layer security and acoustic privacy. It underscores the importance of a holistic approach to security that extends beyond digital threats.
Remediation Actions and Mitigations
Addressing a threat that harnesses the very physics of data transmission requires a multi-layered approach. While complete immunity may be challenging, several actions can significantly reduce risk:
- Physical Security of Fiber Infrastructure: Enhance physical security around fiber junction boxes, distribution points, and termination equipment. Unauthorized access to these points is critical for initiating such an attack. This includes robust locks, surveillance, and access control.
- Fiber Duct Hardening: Investigate and implement methods to “harden” fiber optic cable ducts and conduits, particularly in sensitive areas. This could involve using materials that dampen acoustic vibrations or creating physical separation from potential sound sources.
- Acoustic Isolation of Sensitive Areas: For critical meeting rooms or offices where highly sensitive discussions occur, consider enhanced acoustic isolation techniques. This goes beyond simple soundproofing and involves creating an environment where external vibrations are minimized.
- Optical Time-Domain Reflectometry (OTDR) Monitoring: While not a direct countermeasure to the eavesdropping itself, advanced OTDR systems could potentially be used to monitor for anomalies in fiber characteristics that might indicate an attempt to inject light or otherwise tamper with the fiber. However, sophisticated attackers might be able to mask their presence.
- Randomized Light Injection: Explore research into methods that introduce controlled noise or randomized light patterns into fibers carrying sensitive data. This could potentially interfere with an attacker’s ability to cleanly extract acoustic signals.
- Secure Communication Protocols: Emphasize the use of end-to-end encrypted communication for all sensitive discussions, whether digital or voice. While this doesn’t prevent detection, it ensures that even if conversations are captured, their content remains unreadable.
The development of specialized tools for detecting such an attack is still in its nascent stages, given the novelty of the research. However, an overview of potentially relevant tools for fiber integrity checks is provided:
| Tool Name | Purpose | Link |
|---|---|---|
| Optical Time-Domain Reflectometer (OTDR) | Measures signal loss, identifies breaks, and characterizes fiber optic cables. Can detect significant physical tampering. | https://en.wikipedia.org/wiki/Optical_time-domain_reflectometer |
| Fiber Inspection Microscope | Inspects connector end-faces for damage or contamination that could indicate tampering or poor installation. | https://www.flukenetworks.com/datacom-cabling/fiber-testing/fiber-inspection-microscope |
| Optical Loss Test Set (OLTS) | Measures the total insertion loss of a fiber optic link, which can reveal degradation or intentional attenuation. | https://www.flukenetworks.com/datacom-cabling/fiber-testing/optical-loss-test-set |
Looking Ahead: The Evolving Landscape of Eavesdropping
This research from NDSS 2026 serves as a stark reminder that security threats are constantly evolving, often leveraging the most unexpected attack vectors. The ability to covertly transform ubiquitous fiber optic cables into listening devices challenges our fundamental assumptions about privacy and secured environments. For professionals in cybersecurity, IT infrastructure management, and physical security, staying ahead means not just patching software but also understanding the physical vulnerabilities of our interconnected world.
The implications of this discovery are profound, pushing us to rethink physical security measures and consider the acoustic properties of our infrastructure. As we move forward, integrating physical layer security into our overall cybersecurity strategy will be crucial to safeguarding sensitive information against these sophisticated and stealthy forms of surveillance.