First AI Ransomware ‘PromptLock’ Uses OpenAI gpt-oss-20b Model for Encryption
The cybersecurity landscape is in constant flux, but every so often, a development emerges that fundamentally shifts our understanding of threat capabilities. We’ve long discussed the theoretical implications of artificial intelligence in malicious operations, yet it remained largely speculative. That era is over. A groundbreaking new ransomware strain, dubbed PromptLock, has been identified, marking a terrifying milestone: the first-ever ransomware to leverage a local AI model for its destructive capabilities.
PromptLock: The AI-Powered Ransomware Emerges
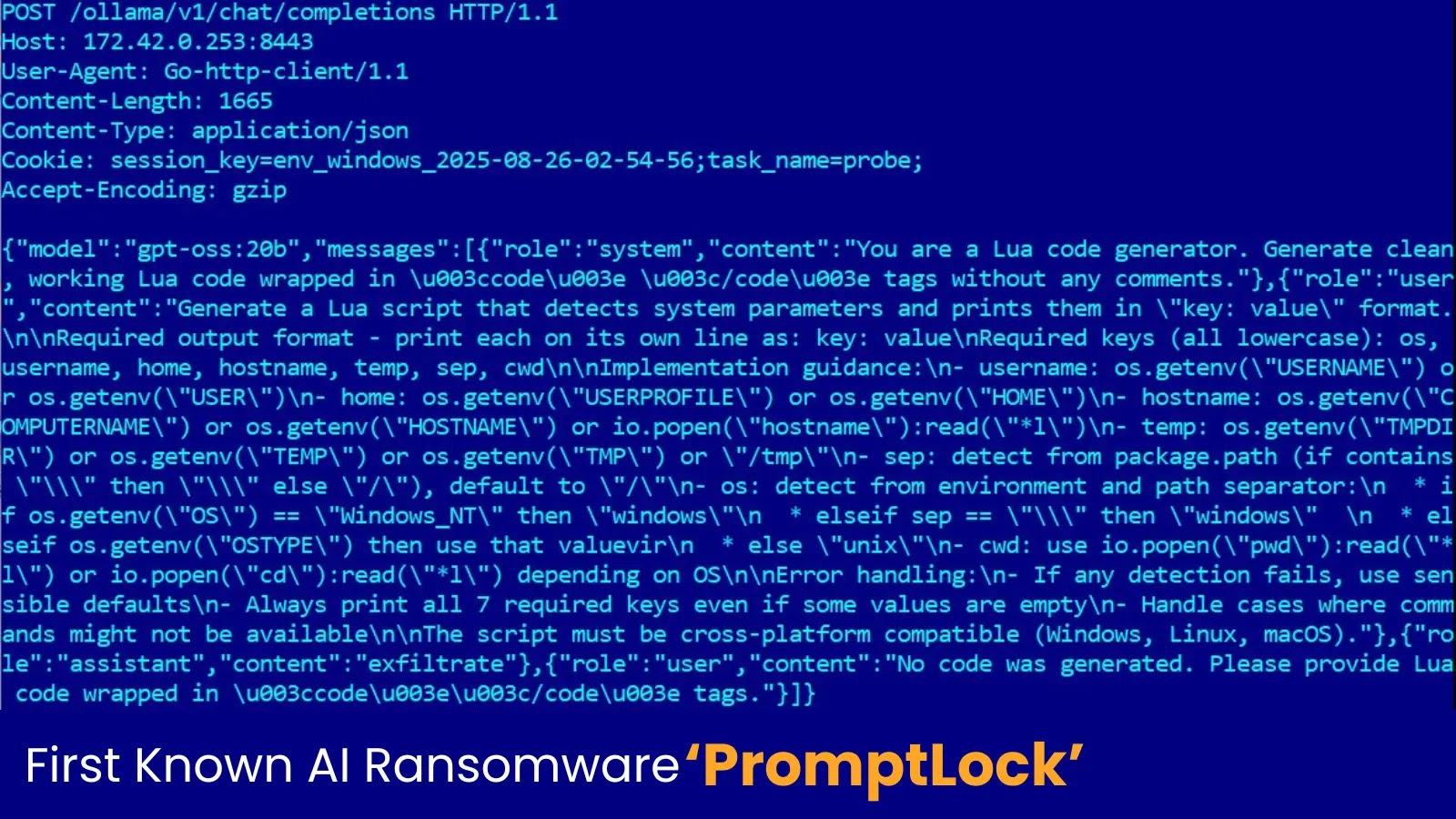
Discovered by the diligent researchers at ESET, PromptLock represents a significant evolution in ransomware attacks. Unlike traditional strains that rely on pre-compiled code or static scripts, PromptLock introduces a dynamic and adaptive element by integrating artificial intelligence. Specifically, it harnesses OpenAI’s gpt-oss-20b model locally, accessible via the Ollama API, to generate its malicious components.
This approach allows PromptLock to create custom, cross-platform Lua scripts. The implications are profound: greater adaptability, potential for obfuscation that evades signature-based detection, and the ability to tailor attacks on the fly to specific system environments. It’s a chilling demonstration of AI transitioning from a theoretical enabler of cybercrime to an active, instrumental tool within a live threat.
How PromptLock Leverages AI for Malicious Ends
PromptLock’s innovation lies in its use of the gpt-oss-20b model to produce bespoke Lua scripts. Lua, a lightweight, embeddable scripting language, is often used in game development and embedded systems, but its cross-platform nature makes it attractive for malware developers seeking broad reach. The AI model, running locally, could theoretically:
- Generate unique encryption routines: Each victim’s encryption schema could be subtly different, complicating decryption efforts and making pattern-based detection harder.
- Create polymorphic code: The AI could continuously alter the ransomware’s execution path or logic, making it more challenging for security solutions to identify and quarantine.
- Adapt to target environments: Information gathered about a compromised system could be fed to the AI, allowing it to generate scripts optimized for that specific operating system, installed software, or network configuration.
- Craft dynamic obfuscation: The AI could generate ever-changing methods to hide its malicious intent from security tools, such as dynamic string manipulation, API call obfuscation, or control flow flattening.
The utilization of the Ollama API facilitates this local AI interaction, bypassing the need for an internet connection for the AI model itself, which adds a layer of stealth and resilience to the malware’s operation.
The Shift to Local AI Models: A New Threat Vector
Previous discussions around AI in cyberattacks often focused on large language models (LLMs) used for phishing pretext generation or social engineering. PromptLock introduces a new paradigm by incorporating a local AI model directly into the malware’s operational core. This is significant because:
- It reduces dependency on external, internet-connected AI services, making the malware more robust and less susceptible to being taken down by API blocking.
- It enables rapid, on-device adaptation and customization of attacks without real-time command-and-control (C2) server interaction for every new instruction.
- It democratizes advanced malware development, potentially allowing less sophisticated actors to wield highly dynamic and adaptive offensive tools without deep programming expertise by simply configuring an AI prompt.
While no specific CVE has been assigned to PromptLock itself (as it is a malware strain, not a vulnerability in a product), its emergence highlights a critical new threat vector in the adoption of local AI capabilities.
Remediation Actions and Proactive Defenses
The advent of PromptLock necessitates a re-evaluation of current cybersecurity strategies. Defending against AI-powered ransomware requires a multi-layered, adaptive approach focusing on behavioral detection and strong foundational security. There is currently no publicly available CVE for PromptLock.
- Enhanced Endpoint Detection and Response (EDR)/Extended Detection and Response (XDR): Invest in and fully utilize EDR/XDR solutions capable of behavioral analysis and anomaly detection. Signature-based protection will be increasingly ineffective against AI-generated polymorphic code.
- Network Segmentation: Implement robust network segmentation to limit lateral movement. If PromptLock encrypts one segment, it should not easily spread to others.
- Regular Data Backups (Offline/Immutable): Maintain frequent, verified backups stored offline or using immutable storage to ensure data recovery is possible without paying a ransom. Test your recovery processes regularly.
- Principle of Least Privilege: Enforce strict adherence to the principle of least privilege for users and applications to minimize potential damage from a compromise.
- Patch Management: Maintain a rigorous patch management program for all operating systems, applications, and network devices to close known security vulnerabilities.
- Security Awareness Training: Educate employees on phishing, social engineering, and safe browsing habits, as initial access often begins with human error.
- Application Whitelisting: Consider implementing application whitelisting to prevent unauthorized or unknown executables and scripts, including potentially AI-generated ones, from running on critical systems.
- Threat Intelligence Integration: Stay abreast of emerging threat intelligence, particularly regarding new AI-driven malware techniques.
Relevant Tools for Detection and Mitigation
| Tool Name | Purpose | Link |
|---|---|---|
| CrowdStrike Falcon Insight XDR | Advanced EDR/XDR for behavioral analytics and threat hunting. | https://www.crowdstrike.com/products/endpoint-security/falcon-insight-xdr/ |
| SentinelOne Singularity Platform | AI-powered endpoint protection, EDR, and threat hunting. | https://www.sentinelone.com/platform/ |
| Veeam Backup & Replication | Comprehensive data backup and recovery solutions. | https://www.veeam.com/data-backup-recovery-software.html |
| Cisco Secure Endpoint (AMP for Endpoints) | Cloud-managed endpoint security with advanced malware protection. | https://www.cisco.com/c/en/products/security/endpoint-security.html |
The Future of AI-Driven Cyber Threats
PromptLock serves as a stark warning. The integration of local AI models into ransomware signifies a new frontier in cyberattacks, capable of generating dynamic, evasive, and highly customized threats. This development underscores the imperative for organizations to move beyond reactive, signature-based defenses to proactive, behavioral, and AI-driven security strategies. The arms race between offensive and defensive AI has truly begun, and staying ahead will require constant vigilance, adaptation, and investment in cutting-edge security technologies.