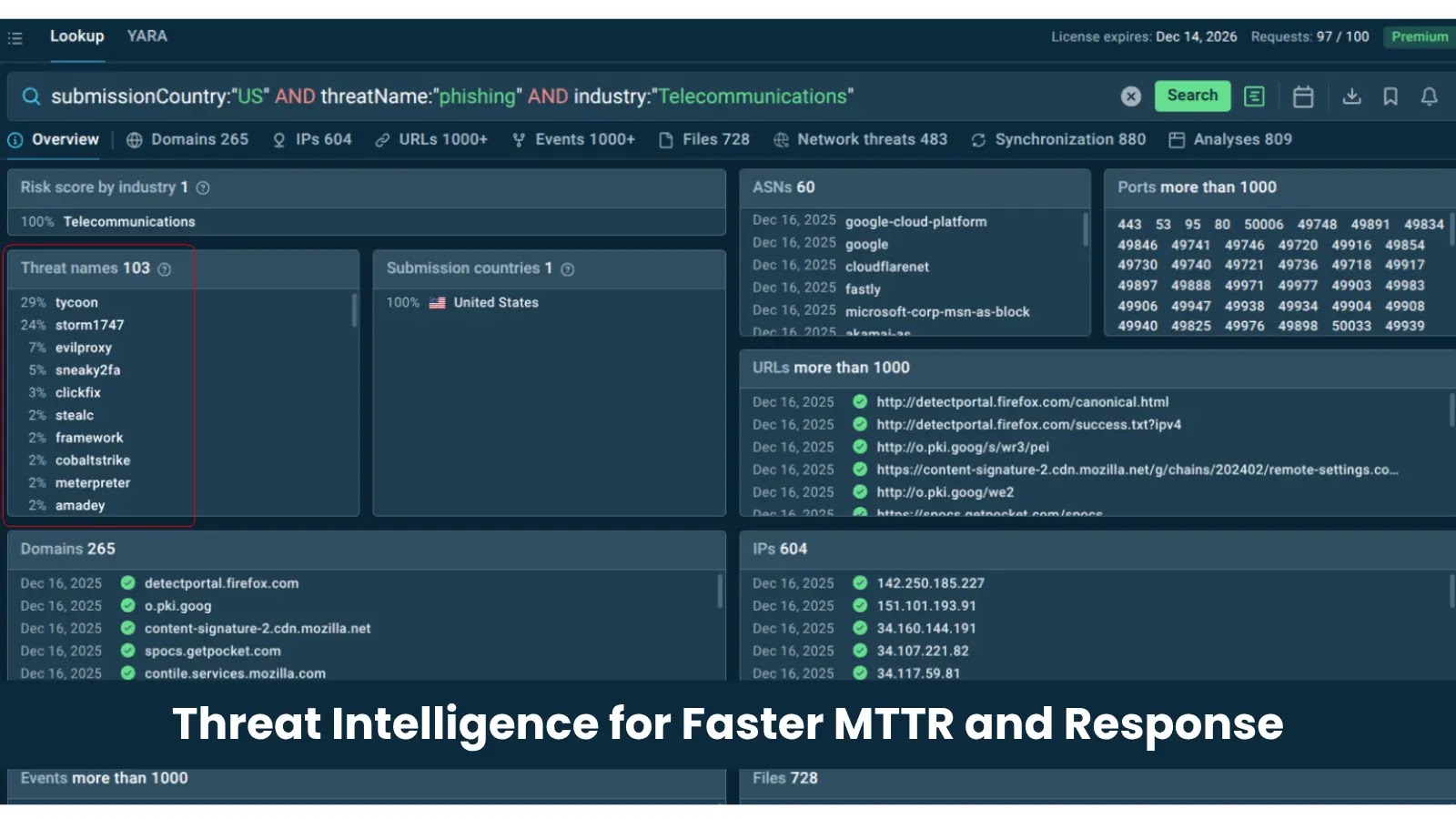
From Alert Overload to Rapid Response: Why Threat Intelligence Is a Top Solution for Fast MTTR
From Alert Overload to Rapid Response: Why Threat Intelligence Is a Top Solution for Fast MTTR
Modern Security Operations Centers (SOCs) face a relentless deluge of alerts. Despite significant investments in sophisticated tools like Security Information and Event Management (SIEM) systems, Endpoint Detection and Response (EDR) platforms, and automation technologies, many organizations continue to grapple with a critical challenge: efficiently investigating these alerts and making confident, timely decisions under pressure. The core issue isn’t a deficiency in tools; rather, it’s the rapidly widening gap between the sheer volume of alerts generated and the practical capacity of security teams to investigate them effectively. This phenomenon, often termed “alert overload,” directly impedes the ability to achieve a rapid Mean Time to Respond (MTTR).
The Pervasive Problem of Alert Overload
Organizations are increasingly drowning in data. Each security solution deployed generates its own set of logs, events, and alerts. While these alerts are designed to signal potential threats, their sheer quantity often overwhelms analysts. This isn’t just a matter of inconvenience; it creates significant operational friction. Analysts spend valuable time sifting through a massive volume of benign or low-priority alerts, delaying their ability to identify and respond to genuine threats. This often leads to:
- Analyst Burnout: Constant exposure to a high volume of alerts, many of which are false positives, leads to fatigue and decreased morale.
- Missed Threats: Critical alerts can be buried amidst noise, increasing the risk of a breach going undetected for extended periods.
- Increased MTTR: The time spent triaging and investigating non-critical alerts directly inflates the overall Mean Time to Respond (MTTR) to actual incidents.
- Inefficient Resource Allocation: Valuable security resources are diverted to low-impact tasks instead of proactive threat hunting or strategic security enhancements.
Threat Intelligence: Bridging the Gap Between Volume and Capacity
Threat intelligence emerges as a powerful antidote to alert overload and a catalyst for improving MTTR. By providing context, relevance, and prioritization for incoming alerts, threat intelligence transforms raw security data into actionable insights. It empowers SOC teams to move beyond reactive firefighting and adopt a more proactive, informed stance against cyber threats.
The strategic application of threat intelligence allows organizations to:
- Prioritize True Positives: Threat intelligence feeds provide information on known malicious IP addresses, domains, file hashes, TTPs (Tactics, Techniques, and Procedures), and attacker profiles. This allows SIEM and EDR systems to filter out known benign activity and highlight events that align with current threat landscapes, significantly reducing false positives. For example, knowing that a specific IP address is associated with a recent APT campaign (e.g., related to CVE-2023-38831 impacting WinRAR) elevates an alert from that IP to critical status.
- Enhance Investigation Speed: When an alert triggers, enriched with threat intelligence, analysts instantly gain context. Instead of starting an investigation from scratch, they know who the likely adversary is, their typical methods, and potential targets. This streamlines the investigation process, allowing for quicker identification of the root cause and scope of an incident.
- Automate Response Actions: With high-fidelity threat intelligence, certain low-level, high-confidence threats can be automatically blocked or contained. For instance, if a known malicious domain (CVE-2023-0288 for OpenSSL is an example of a critical vulnerability, though not directly related to domains, it highlights the need for quick action on high-severity threats) attempts to establish a connection, firewalls can block it instantly, drastically reducing response time for that specific threat vector.
- Proactive Threat Hunting: Beyond reactive alert handling, threat intelligence fuels proactive threat hunting initiatives. By understanding the latest TTPs and emerging indicators of compromise (IoCs), security teams can actively search for threats that may have bypassed traditional defenses, preventing incidents before they escalate.
- Informed Decision-Making: Under pressure, confident decision-making is paramount. Threat intelligence provides the necessary data points—such as attacker motivation, capabilities, and historical actions—to make well-informed decisions regarding containment, eradication, and recovery strategies.
Integrating Threat Intelligence for Optimal MTTR
Maximizing the benefits of threat intelligence requires a strategic integration approach:
- Choose Relevant Feeds: Not all threat intelligence is created equal. Select feeds that are pertinent to your industry, geographic location, and specific threat landscape.
- Automate Ingestion and Correlation: Integrate threat intelligence feeds directly into your SIEM, EDR, and security orchestration, automation, and response (SOAR) platforms. This ensures real-time correlation with your internal logs and automated enrichment of alerts.
- Develop Use Cases: Create specific use cases that leverage threat intelligence to detect and prioritize threats relevant to your organization.
- Train Your Analysts: Equip your SOC team with the skills to interpret and leverage threat intelligence effectively during investigations and threat hunting.
- Continuous Refinement: Threat intelligence is dynamic. Regularly review and update your feeds and integration strategies to maintain relevance and effectiveness.
Conclusion
The battle against cyber threats is a race against time. In an environment dominated by alert overload, an organization’s ability to minimize its Mean Time to Respond (MTTR) is a critical indicator of its overall security posture. Threat intelligence is no longer a luxury but a necessity for any modern SOC striving for efficiency and effectiveness. By providing context, enabling prioritization, and accelerating investigations, robust threat intelligence capabilities empower security teams to cut through the noise, focus on genuine threats, and respond with the speed and precision required to defend against today’s sophisticated adversaries.