Hackers Abuse GitHub and GitLab to Host Malware and Credential Phishing Campaigns
The Trojan Horse in Trusted Code Repositories: How Attackers Weaponize GitHub and GitLab
Imagine a scenario where the very platforms you trust daily for software development and collaboration become conduits for malware and credential theft. This isn’t a hypothetical threat; it’s the alarming reality facing organizations as cybercriminals increasingly abuse GitHub and GitLab to host malicious payloads and engineer sophisticated phishing campaigns. The core issue? These widely used developer platforms often bypass traditional security filters, granting attackers an unhindered path directly into corporate networks and unsuspecting users’ inboxes.
The Evolution of Attack Vectors: Why GitHub and GitLab?
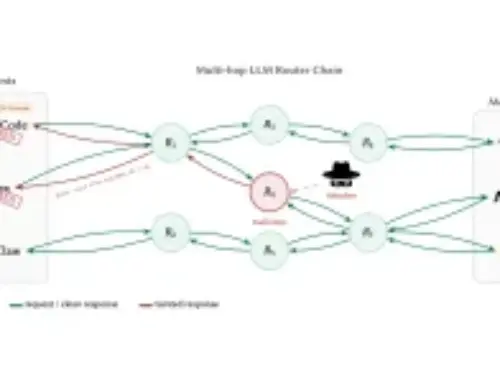
Threat actors are constantly seeking novel ways to evade detection. Their pivot to platforms like GitHub and GitLab is a calculated move. Organizations and their security tools inherently trust these domains due to their critical role in the software development lifecycle (SDLC). This inherent trust creates a blind spot, allowing malicious content masquerading as legitimate code or developer resources to bypass perimeter defenses that might flag less reputable hosting services. Cybercriminals are exploiting this trust to their advantage, leveraging the credibility of these platforms to enhance the success rate of their attacks.
Malware Hosting and Credential Phishing: The Dual Threat
The abuse of GitHub and GitLab manifests in two primary attack methodologies:
- Malware Hosting: Attackers upload malicious executables, scripts, or archives directly to repositories. These files are then distributed through phishing emails, compromised websites, or social engineering tactics, often appearing as legitimate software updates, tools, or project dependencies. Since the hosting domain is GitHub or GitLab, security mechanisms designed to block known malicious domains may let these downloads sail through.
- Credential Phishing Campaigns: Beyond hosting malware, these platforms are being used to host sophisticated phishing pages designed to steal login credentials. A common tactic involves creating a repository that mimics a legitimate login portal (e.g., for a SaaS application or even an internal corporate system). Users are then directed to these fake pages via deceptive links, often delivered through tailored spear-phishing emails, believing they are interacting with a trusted service. The high reputation of GitHub and GitLab domains further boosts the likelihood of these phishing links bypassing email security and endpoint protection.
The Peril of Implicit Trust
The inherent security posture of many organizations rests on the assumption that traffic from reputable domains like GitHub and GitLab is benign. This implicit trust is precisely what attackers are weaponizing. For a network firewall or email gateway, a link to github.com/malicious-user/repo/raw/main/evil.exe looks superficially similar to a legitimate link to github.com/trusted-org/project/raw/main/app.zip. Distinguishing between the two requires deeper inspection, often beyond the capabilities of basic domain-level filtering.
Remediation Actions and Proactive Defenses
Countering this evolving threat requires a multi-faceted approach, balancing security with the operational necessity of these platforms:
- Enhanced Endpoint Detection and Response (EDR): Implement and continuously tune EDR solutions to detect malicious behavior on endpoints, regardless of the download source. Look for suspicious process chains, file modifications, and network connections.
- Advanced Email Security Gateways: Configure email security solutions to perform deep link analysis and sandboxing for URLs, even those originating from trusted domains. Look for deviations in URL structure, non-standard content on landing pages, and unusual redirection chains.
- Network Traffic Analysis (NTA): Monitor network traffic for unusual connections or data exfiltration attempts originating from or destined for GitHub/GitLab, especially when associated with user activity that doesn’t align with development workflows.
- User Awareness Training: Conduct regular and engaging security awareness training that highlights the nuances of sophisticated phishing, including attacks leveraging trusted domains. Emphasize critical thinking about unexpected requests, even if they appear to come from familiar sources.
- Application Security Posture Management (ASPM) / Software Supply Chain Security: For organizations consuming open-source code from these platforms, implement robust processes for vetting third-party dependencies, including scanning for known vulnerabilities (e.g., using tools that identify packages with associated CVEs like CVE-2023-38831 relating to WinRAR vulnerabilities exploited in supply chain attacks) before integration into production environments.
- Implement Browser Security Extensions: Deploy and manage enterprise-grade browser security extensions that can detect and block phishing attempts and malicious downloads in real-time.
- Leverage Threat Intelligence: Integrate threat intelligence feeds that track new malicious repositories, phishing campaigns, and indicators of compromise (IOCs) related to the abuse of developer platforms.
The abuse of GitHub and GitLab underscores a critical shift in the threat landscape. Attackers are no longer just targeting obscure corners of the internet; they are weaponizing the very infrastructure that underpins modern software development. By understanding these tactics and implementing robust, layered security controls, organizations can mitigate the risks and protect their assets from these increasingly sophisticated threats. The key lies in moving beyond implicit trust and adopting a posture of continuous verification and vigilance, even for seemingly benign traffic.