Hackers Impersonate Secure Messaging Apps to Deploy ProSpy in Middle East Espionage Attacks
In a pervasive and highly concerning development, a sophisticated mobile espionage campaign has been unmasked, revealing a deep-seated threat targeting individuals across the Middle East since at least 2022. This persistent operation leverages a cunning tactic: presenting malicious Android spyware, dubbed ProSpy, by impersonating widely trusted secure messaging applications. This report delves into the mechanics of this attack, its implications, and crucial mitigation strategies for users and organizations alike.
The Deceptive Lure: Impersonating Secure Messaging Apps
The attackers behind this operation demonstrate a keen understanding of user trust and digital habits. They craft highly convincing, fake versions of popular secure messaging platforms such as Signal and ToTok. These counterfeit applications are meticulously designed to mimic the legitimate apps visually, making them incredibly difficult for an unsuspecting user to differentiate. The primary goal is to trick victims into downloading and installing these seemingly benign applications, which, in reality, are Trojan horses for the potent ProSpy spyware.
The choice of secure messaging apps for impersonation is particularly insidious. Users download these applications precisely because they offer enhanced privacy and security, creating a false sense of safety that the attackers exploit. Once installed, the fake app functions as a wrapper, subtly deploying ProSpy onto the victim’s device while potentially offering some superficial, albeit non-functional, aspects of the legitimate messaging service.
ProSpy: A Potent Android Spyware
ProSpy is not a trivial piece of malware; it’s a powerful Android spyware engineered for comprehensive surveillance. While the specific functionalities can evolve, typical capabilities of such sophisticated spyware include:
- Call Recording: Intercepting and recording both incoming and outgoing voice calls.
- SMS/MMS Interception: Reading and exfiltrating text messages, including one-time passwords (OTPs) and sensitive communications.
- Location Tracking: Monitoring the device’s GPS location in real-time, providing a detailed movement history of the victim.
- Microphone Eavesdropping: Activating the device’s microphone to record ambient conversations.
- Camera Access: Covertly taking photos and videos using the device’s cameras.
- Contact List Exfiltration: Stealing contact information, potentially leading to further social engineering attacks.
- File Access: Gaining access to files stored on the device, including documents, photos, and videos.
- App Data Collection: Accessing data from other applications installed on the device, including financial or personal information.
The covert nature of ProSpy means it operates in the background without the user’s knowledge, making detection challenging without specific security measures.
Distribution Mechanisms and Target Profile
While the exact distribution methods are not fully detailed in the source, such targeted espionage campaigns typically employ a combination of:
- Spear Phishing: Highly customized emails or messages designed to trick specific individuals into downloading the malicious app.
- Watering Hole Attacks: Compromising legitimate websites frequented by the target demographic and injecting malicious links or downloads.
- Social Engineering: Directly manipulating victims through social media, dating apps, or other personal interactions to persuade them to install the fake app.
- Side-Loading: Encouraging users to download apps from unofficial app stores or directly via links, bypassing the security checks of official marketplaces like Google Play.
The focus on the Middle East and the sophistication of the attack suggest state-sponsored actors or highly organized criminal groups are likely behind this campaign, with targets potentially including activists, journalists, government officials, or individuals of strategic interest.
Remediation Actions and Proactive Defense
Protecting against sophisticated mobile espionage campaigns like those involving ProSpy requires a multi-layered approach. Users and organizations must prioritize cybersecurity hygiene and proactive defense strategies.
- Verify App Sources: Always download apps exclusively from official and trusted app stores, such as Google Play for Android devices. Even then, exercise caution and verify developer information.
- Scrutinize App Permissions: Before installing any app, carefully review the permissions it requests. Be suspicious if a messaging app demands access to your microphone, camera, or location when not actively using those features within the app.
- Employ Mobile Endpoint Detection and Response (MEDR): For organizations, implementing MEDR solutions provides advanced threat detection, incident response capabilities, and continuous monitoring of mobile devices.
- Maintain OS Updates: Keep your mobile operating system and all installed applications updated. Updates often include critical security patches for known vulnerabilities. For instance, addressing an Android vulnerability like CVE-2023-21102 could prevent an exploit chain.
- Educate Users: Implement robust security awareness training programs to educate users about phishing, social engineering tactics, and the dangers of side-loading applications.
- Back Up Data Regularly: In the event of a compromise, having recent backups can minimize data loss and facilitate recovery.
- Utilize Reputable Antivirus/Anti-malware: While not foolproof against advanced persistent threats, a strong mobile security suite can add an extra layer of defense against known malware signatures.
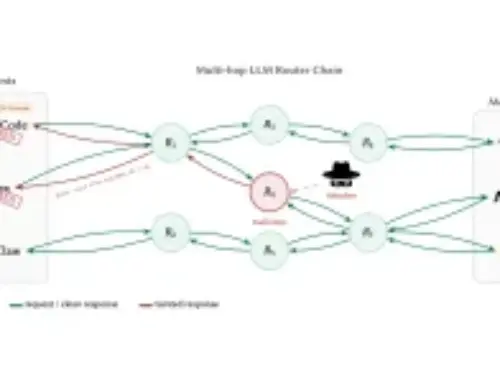
Threat Intelligence and Collaborative Defense
The discovery of campaigns like the ProSpy operation underscores the critical role of threat intelligence sharing. Cybersecurity researchers and organizations collaborating to identify, analyze, and disseminate information about new threats is vital. Staying informed of the latest attack vectors, malware capabilities, and adversary tactics empowers better defensive postures. Enterprises should regularly consult reputable threat intelligence feeds and security advisories to keep their defenses current against evolving threats.
Conclusion
The use of fake secure messaging applications to deploy ProSpy in Middle East espionage operations highlights an alarming trend of attackers leveraging trust and digital habits for malicious ends. This campaign serves as a stark reminder that even the most security-conscious applications can be co-opted for nefarious purposes through social engineering and deception. Vigilance, coupled with robust technical security measures and continuous user education, remains paramount in defending against such sophisticated and persistent threats.