Hackers Leveraging Cloudflare Anti-Bot Features to Steal Microsoft 365 Credentials
The Trojan Horse in the Cloud: How Hackers Weaponize Cloudflare Anti-Bot Features
The digital landscape is a constant battleground, with defenders deploying sophisticated tools to protect user data and infrastructure. However, a disturbing trend has emerged: threat actors are now leveraging these very protective measures as a shield for their malicious activities. A recent and sophisticated campaign targets Microsoft 365 users, demonstrating how hackers are weaponizing Cloudflare’s anti-bot features to stealthily steal credentials. This evolution in tactics demands immediate attention from IT professionals and security analysts.
Cloudflare is a cornerstone of web security, renowned for its robust anti-bot, DDoS protection, and content delivery network (CDN) services. Organizations globally entrust Cloudflare to safeguard their websites from automated attacks and ensure seamless user experiences. The irony of this latest campaign lies in the attackers’ ability to co-opt Cloudflare’s legitimate security mechanisms, transforming them into a sophisticated cloaking device for credential harvesting.
The Deceptive Mechanism: Leveraging Trust for Malice
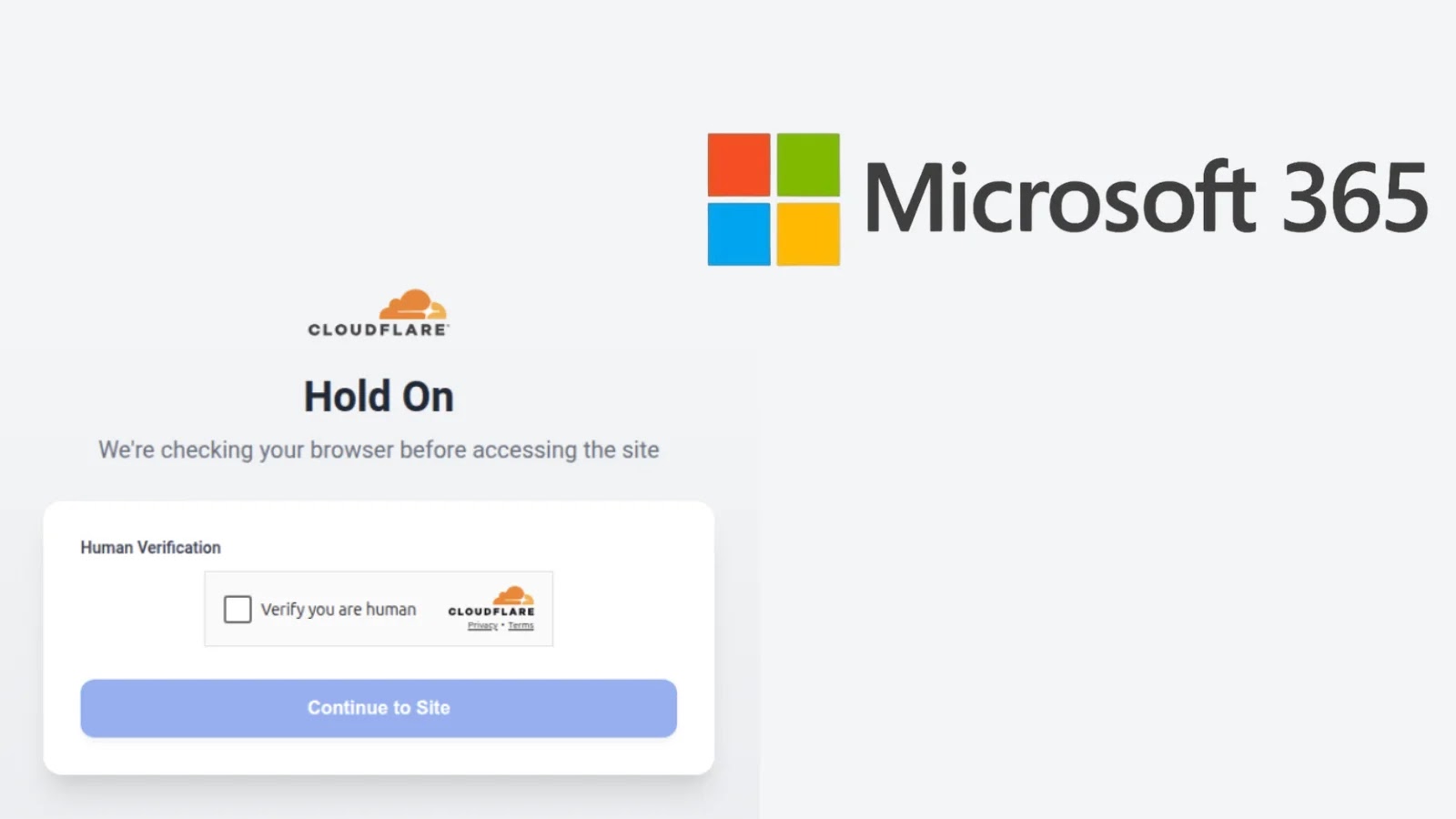
This credential harvesting campaign is particularly insidious because it subverts the trust associated with Cloudflare’s protective services. Instead of directly battling Cloudflare’s security layers, threat actors are integrating their phishing infrastructure directly behind Cloudflare. This ingenious tactic allows their malicious pages to inherit Cloudflare’s positive reputation and anti-bot challenges, making them appear legitimate to both automated security tools and unsuspecting users.
Here’s how the attack typically unfolds:
- Attackers register a domain and configure it to use Cloudflare for DNS and protection.
- They then host phishing pages designed to mimic Microsoft 365 login portals behind this Cloudflare setup.
- When a victim attempts to access the phishing site, Cloudflare’s legitimate security checks (like CAPTCHAs or JavaScript challenges) are presented. This process can inadvertently “legitimize” the malicious site in the eyes of some security scanners or even the end-user.
- Once these checks are passed, the user is presented with the spoofed Microsoft 365 login page, hosted and protected by Cloudflare.
- Unaware of the deception, the user enters their Microsoft 365 credentials, which are then harvested by the attackers.
This method significantly enhances the longevity and effectiveness of phishing campaigns. By operating behind Cloudflare, the attackers benefit from obscurity, making it harder for traditional blacklisting or IP-based blocking mechanisms to detect and neutralize their infrastructure.
Advanced Evasion Techniques
The success of this campaign hinges on several advanced evasion techniques:
- Reputation Borrowing: The malicious infrastructure “borrows” the excellent reputation of Cloudflare’s IP ranges, making the phishing sites appear less suspicious to security scanners and email filters.
- Anti-Bot Game Theory: The attackers leverage Cloudflare’s own anti-bot mechanisms. While these are designed to block malicious bots, the human interaction required to pass them inadvertently authenticates the user, paving the way for credential theft. Some advanced persistent threat (APT) groups have even been observed crafting their bot activity to mimic legitimate Cloudflare challenges, further blurring lines.
- Dynamic Infrastructure: By frequently rotating domains and leveraging Cloudflare’s extensive network, attackers can quickly shift their operations, making detection and takedown efforts a continuous challenge.
- Targeted Attacks: While the core mechanism can be broadly applied, specific campaigns are highly targeted, focusing on organizations with significant Microsoft 365 deployments, further increasing their chances of success.
Remediation Actions and Proactive Defense
Mitigating the risks posed by such sophisticated attacks requires a multi-layered approach focusing on user education, technical controls, and continuous monitoring.
- Strengthen User Education: Regular training sessions should emphasize vigilance regarding suspicious links and unconventional login prompts, even those that seem to originate from trusted services. Users must be educated to always verify URLs before entering credentials.
- Implement Multi-Factor Authentication (MFA): MFA remains one of the most effective deterrents against credential theft. Even if credentials are stolen, MFA significantly complicates unauthorized access.
- Deploy Advanced Threat Protection (ATP) Solutions: Email and endpoint security solutions with sandboxing and URL rewriting capabilities can detect and block phishing attempts even when they are hidden behind legitimate services.
- Leverage Microsoft 365 Security Features: Configure Microsoft 365’s native security features, such as Conditional Access policies, to restrict access from untrusted locations or devices, and enforce strict session controls.
- Monitor Cloudflare Logs and Analytics: For organizations using Cloudflare, closely monitor logs for unusual traffic patterns or challenges that deviate from normal user behavior.
- Adopt a Zero-Trust Security Model: Assume no user or device is inherently trustworthy, even within the corporate network. Verify every transaction and access attempt.
- Implement DMARC, DKIM, and SPF: Ensure robust email authentication protocols are in place to prevent email spoofing, a common vector for these phishing campaigns.
Recommended Tools for Detection and Mitigation
Addressing this type of threat requires a combination of robust security tools and practices.
| Tool Name | Purpose | Link |
|---|---|---|
| Microsoft Defender for Office 365 | Advanced threat protection for email and collaboration. | Official Site |
| Proofpoint / Mimecast | Email security gateways for advanced phishing and malware detection. | Proofpoint / Mimecast |
| Security Information and Event Management (SIEM) Solutions | Centralized logging and analysis (e.g., Splunk, Microsoft Sentinel). | Splunk / Microsoft Sentinel |
| Passwordless Authentication Technologies | Eliminates password-related risks (e.g., FIDO2 security keys). | FIDO Alliance |
The Evolving Threat Landscape
This Microsoft 365 credential harvesting campaign (though not assigned a specific CVE, similar tactics are often observed in broader phishing operations related to CVEs like CVE-2023-38831, which covers various phishing vulnerabilities) underscores a critical shift in the cyber adversary’s playbook. They are no longer just exploiting vulnerabilities or performing brute-force attacks. Instead, they are learning to mimic and manipulate legitimate security infrastructure to cloak their malicious intent. This presents a formidable challenge that requires continuous adaptation and a proactive defense posture from organizations.
The ability of hackers to use Cloudflare’s anti-bot features as a cover exemplifies the sophistication of modern cyber threats. Staying ahead demands not just technical solutions, but a deep understanding of evolving attack methodologies, coupled with robust security practices and ongoing vigilance. Protect your Microsoft 365 environment by prioritizing user education, fortifying authentication, and implementing advanced threat detection systems.