Hackers Use Venom Stealer to Turn ClickFix Lures Into Full Data Exfiltration Pipelines
A silent but sophisticated threat has been quietly proliferating within the cybercrime underground, posing a significant challenge to conventional cybersecurity defenses. Far more advanced than typical data-stealing malware, a new platform dubbed Venom Stealer is not merely content with harvesting credentials. Instead, it engineers comprehensive, automated attack chains, transforming seemingly innocuous social engineering lures into full-blown data exfiltration pipelines. This evolution in tactics demands a deeper understanding from IT professionals and security analysts to effectively counter such advanced persistent threats.
The Rise of Venom Stealer: Beyond Basic Credential Theft
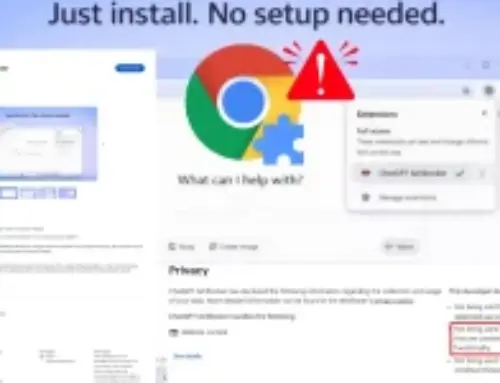
Venom Stealer distinguishes itself from its predecessors by offering a sophisticated malware-as-a-service (MaaS) platform. Unlike simpler stealers that focus narrowly on gathering login credentials or financial information, Venom Stealer orchestrates an entire lifecycle of compromise. It begins with a seemingly simple, yet effective, social engineering trick, often leveraging “ClickFix” lures, and escalates to a complete data exfiltration operation. This comprehensive approach signifies a shift in threat actor methodology, moving towards integrated, multi-stage attacks that are harder to detect and mitigate.
The “ClickFix” lure typically refers to a technique designed to trick users into downloading and executing malicious files under the guise of an essential software update, a patch for a common issue, or a utility tool. Once executed, Venom Stealer doesn’t just collect data; it establishes persistent access, explores the compromised system, and siphons off valuable information, including sensitive documents, stored passwords, browser data, and even cryptocurrency wallet details. Its modular design allows threat actors to customize payloads and exfiltration methods, making it highly adaptable.
Automated Attack Chains: From Lure to Exfiltration
The core innovation of Venom Stealer lies in its ability to automate the entire attack chain. This automation reduces the operational overhead for attackers and increases the speed and scale of their campaigns. The workflow typically involves:
- Initial Compromise: Through ClickFix lures delivered via phishing emails, malicious advertisements, or compromised websites, victims are coerced into downloading and executing the initial dropper.
- Payload Delivery: The dropper then fetches and deploys the Venom Stealer core modules, which include various functionalities for reconnaissance, data collection, and exfiltration.
- Data Harvesting: Venom Stealer systematically scans the infected system for a wide array of data types, including browser history, saved passwords, autofill data, cryptocurrency wallet files, VPN configurations, and sensitive documents.
- Command and Control (C2) Communication: Exfiltrated data is then securely transmitted to attacker-controlled C2 servers, often using encrypted channels to evade detection.
- Persistence: The malware often establishes persistence mechanisms, ensuring it survives system reboots and can continue its operation unimpeded.
This automated pipeline makes Venom Stealer particularly dangerous, as it minimizes the human interaction required from the attacker’s side once the initial lure is successful, thereby expanding the potential victim pool and increasing the efficiency of data theft operations.
Understanding the Impact: Beyond Financial Loss
While direct financial loss through compromised banking credentials or cryptocurrency wallets is a primary concern, the impact of Venom Stealer extends far beyond. The exfiltration of sensitive documents, intellectual property, and even personal identifiable information (PII) can lead to:
- Reputational Damage: For businesses, data breaches resulting from stealer infections can severely tarnish their reputation and erode customer trust.
- Regulatory Fines: Compliance failures stemming from PII exfiltration can result in hefty fines under regulations like GDPR or CCPA.
- Espionage and Competitive Disadvantage: Stolen intellectual property or strategic business data can be used by competitors or nation-state actors for economic espionage, leading to significant competitive disadvantage.
- Further Attacks: Compromised credentials can serve as a jumping-off point for lateral movement within a network, leading to even more severe breaches.
Remediation Actions
Addressing the threat posed by Venom Stealer requires a multi-layered and proactive security strategy. The following actions are crucial for both preventing infection and effectively responding to a compromise:
- Employee Training and Awareness: Educate users about the dangers of phishing, social engineering lures (especially those disguised as “ClickFix” solutions), and the importance of verifying software downloads from official sources only. Employees are often the first line of defense.
- Robust Email and Web Filtering: Implement advanced email gateways and web filters to detect and block malicious attachments, links to compromised websites, and phishing attempts before they reach end-users.
- Endpoint Detection and Response (EDR) Solutions: Deploy EDR solutions capable of behavioral analysis to detect suspicious activities, such as unauthorized process execution, unusual network connections, and attempts to access sensitive files, which might indicate a stealer infection.
- Principle of Least Privilege: Enforce the principle of least privilege, ensuring users and applications only have the minimum necessary access rights to perform their functions. This limits potential damage if a system is compromised.
- Multi-Factor Authentication (MFA): Implement MFA across all critical systems and services. Even if credentials are stolen, MFA acts as a vital secondary defense layer, significantly reducing the likelihood of account takeover.
- Regular Software Updates and Patching: Keep operating systems, applications, and security software up to date with the latest patches to remediate known vulnerabilities that attackers might exploit.
- Disable Macro Execution by Default: Configure Microsoft Office and other productivity suites to disable macro execution by default, or to prompt users for approval, as malicious macros are a common vector for initial compromise.
- Network Segmentation: Segment networks to restrict lateral movement of malware in case of a breach, limiting its ability to spread and exfiltrate data from critical systems.
- Incident Response Plan: Develop and regularly test a comprehensive incident response plan specifically for data breaches and malware infections, ensuring a swift and effective response to minimize damage.
Conclusion
Venom Stealer represents a significant evolution in the threat landscape, demonstrating how threat actors are refining their tools and techniques to create highly automated and effective attack pipelines. The shift from simple credential harvesting to full-scale data exfiltration orchestrated by a MaaS platform underscores the need for organizations to move beyond traditional perimeter defenses. A holistic approach combining advanced security technologies, rigorous employee training, and robust incident response capabilities is paramount. Staying informed about emerging threats like Venom Stealer and proactively implementing layered security measures are critical steps in protecting valuable assets from these sophisticated digital predators.