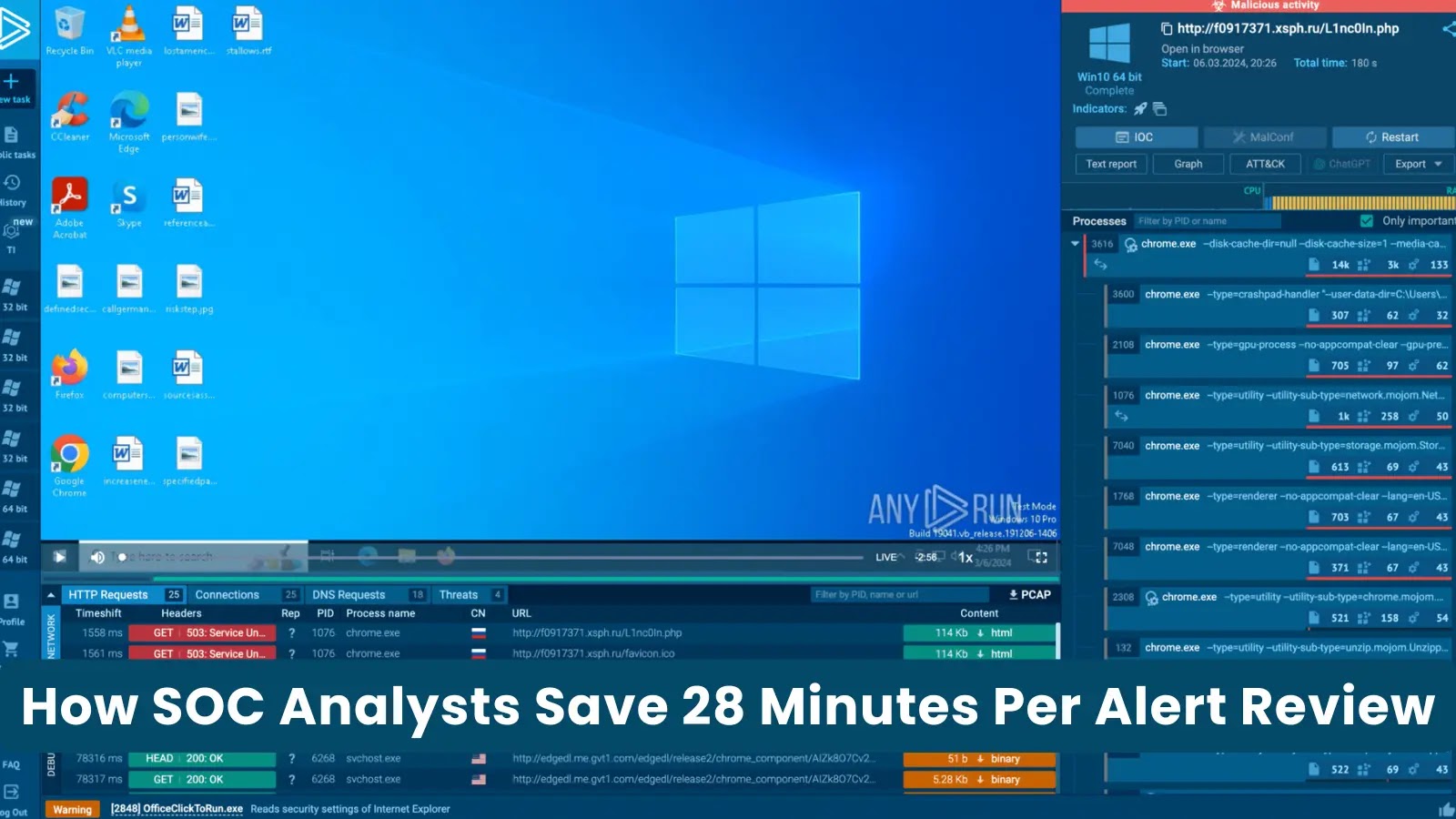
How SOC Analysts Can Save 28 Minutes Per Alert Review
In the high-stakes world of cybersecurity, time is a critical differentiator between proactive defense and reactive damage control. For Security Operations Center (SOC) analysts, the sheer volume of alerts can be overwhelming, with many hours spent investigating incidents that ultimately prove benign. What if there was a way to significantly cut down on the time spent per alert, freeing up valuable resources for genuine threats? Recent insights suggest that SOC analysts can save up to 28 minutes per alert review, a substantial gain in efficiency and impact.
The Time-Consuming Reality of Alert Investigation
Many cybersecurity teams grapple with a fundamental challenge: the average alert investigation, even for seemingly simple cases, consumes approximately 30 minutes. This isn’t necessarily due to inherent complexity, but rather the fragmented nature of data and tools. Before an analyst can confidently declare an alert harmless or, conversely, a genuine threat, they must perform a series of often manual, time-intensive steps:
- Reputation Checks: Verifying the legitimacy of IP addresses, URLs, and file hashes.
- Enrichment: Gathering additional context from various threat intelligence platforms.
- Detonation Requests: Submitting suspicious files or links to sandboxes for behavioral analysis.
- Log Pivots: Sifting through extensive logs from firewalls, SIEMs, endpoints, and other security tools to trace activity.
Each of these steps requires logging into different systems, copying and pasting data, and synthesizing information manually. At scale, this repetitive process quickly erodes analyst productivity and introduces fatigue, increasing the risk of missing critical indicators.
Understanding the 28-Minute Saving Potential
The potential to save 28 minutes per alert review, effectively reducing a 30-minute investigation to a mere 2 minutes, stems from streamlining and automating these labor-intensive steps. The core principle lies in reducing the manual context-gathering effort. By automating the aggregation and correlation of data from disparate sources, analysts receive a pre-digested, comprehensive overview that allows for rapid decision-making.
Strategies for Enhanced SOC Efficiency
Achieving this level of efficiency requires a strategic approach focused on integration, automation, and intelligent context delivery. Here’s how SOCs can reclaim those valuable minutes:
- Unified Security Platforms: Implementing a Security Orchestration, Automation, and Response (SOAR) platform, or a unified XDR (Extended Detection and Response) solution, can centralize data and automate workflows. These platforms can automatically pull reputation scores, enrich data with threat intelligence, and even initiate sandbox detonations, presenting all findings in a single pane of glass.
- Automated Enrichment: Instead of manual lookups, automated scripts or platform integrations can instantly retrieve information about suspicious indicators. This includes geolocation data, known associations with malware, domain registration details, and historical data, providing immediate context for the alert.
- Pre-filtered and Prioritized Alerts: Leveraging machine learning and artificial intelligence can help filter out known false positives and prioritize genuine threats. This reduces the overall alert volume that analysts need to review, focusing their attention on high-fidelity incidents.
- One-Click Actions: For common incidents, providing analysts with one-click response actions (e.g., block IP, isolate endpoint, reset password) can dramatically speed up the response phase, moving beyond just investigation.
- Contextual Playbooks: Implementing dynamic playbooks that automatically guide analysts through investigation steps, pre-populating relevant information, and suggesting next actions based on the alert type, ensures consistency and speeds up resolution.
The Impact of Time Savings on Cybersecurity Posture
Saving 28 minutes per alert is not merely a number; it translates into tangible benefits for an organization’s cybersecurity posture:
- Faster Mean Time to Respond (MTTR): Quicker investigations lead to faster containment and eradication of genuine threats, minimizing potential damage.
- Reduced Analyst Burnout: Less time spent on repetitive, manual tasks alleviates stress and improves job satisfaction, helping retain skilled cybersecurity professionals.
- Improved Threat Hunting Capabilities: With fewer alerts to individually triage, analysts gain more time for proactive threat hunting, discovering hidden threats before they escalate.
- Enhanced Accuracy: Automated processes reduce human error in data correlation and analysis, leading to more accurate verdicts on alerts.
- Better Resource Utilization: Security talent can be reallocated to more complex architectural improvements, strategic planning, and advanced threat analysis.
Remediation Actions for SOC Teams
To realize the potential for significant time savings, SOC teams should consider the following actions:
- Assess Current Workflows: Document the current process for alert investigation, identifying bottlenecks and manual steps.
- Investigate SOAR/XDR Solutions: Research and evaluate solutions that offer robust integration with existing security tools and provide automation capabilities.
- Develop Automation Roadmaps: Start with automating the most time-consuming and repetitive tasks first, focusing on high-volume, low-complexity alerts.
- Train Analysts on New Tools: Ensure adequate training for the security team on new platforms and automated workflows to maximize their effectiveness.
- Regularly Review and Optimize: Continuously monitor the efficiency of automated processes and adjust playbooks or integrations as threat landscapes evolve.
The concept applies broadly to different types of security alerts. For instance, an alert related to a suspicious executable (e.g., if it were linked to a known vulnerability pattern, though not explicitly an individual CVE in this general context) would benefit from automated reputation checks, sandbox detonation, and log correlation regarding its origin and behavior on endpoints. Such automation significantly streamlines the investigation, much like how CVEs like CVE-2023-45866 (a recent Android zero-day) or CVE-2024-21415 (a critical Microsoft Outlook vulnerability) would require rapid, context-rich analysis from incident responders.
Conclusion
The aspiration to save 28 minutes per alert review is not a distant dream but an achievable reality for modern SOCs. By strategically embracing automation, consolidating tools, and delivering actionable context directly to analysts, organizations can transform their security operations. This shift not only enhances the speed and efficacy of threat detection and response but also fosters a more sustainable and productive environment for the invaluable cybersecurity professionals on the front lines.





