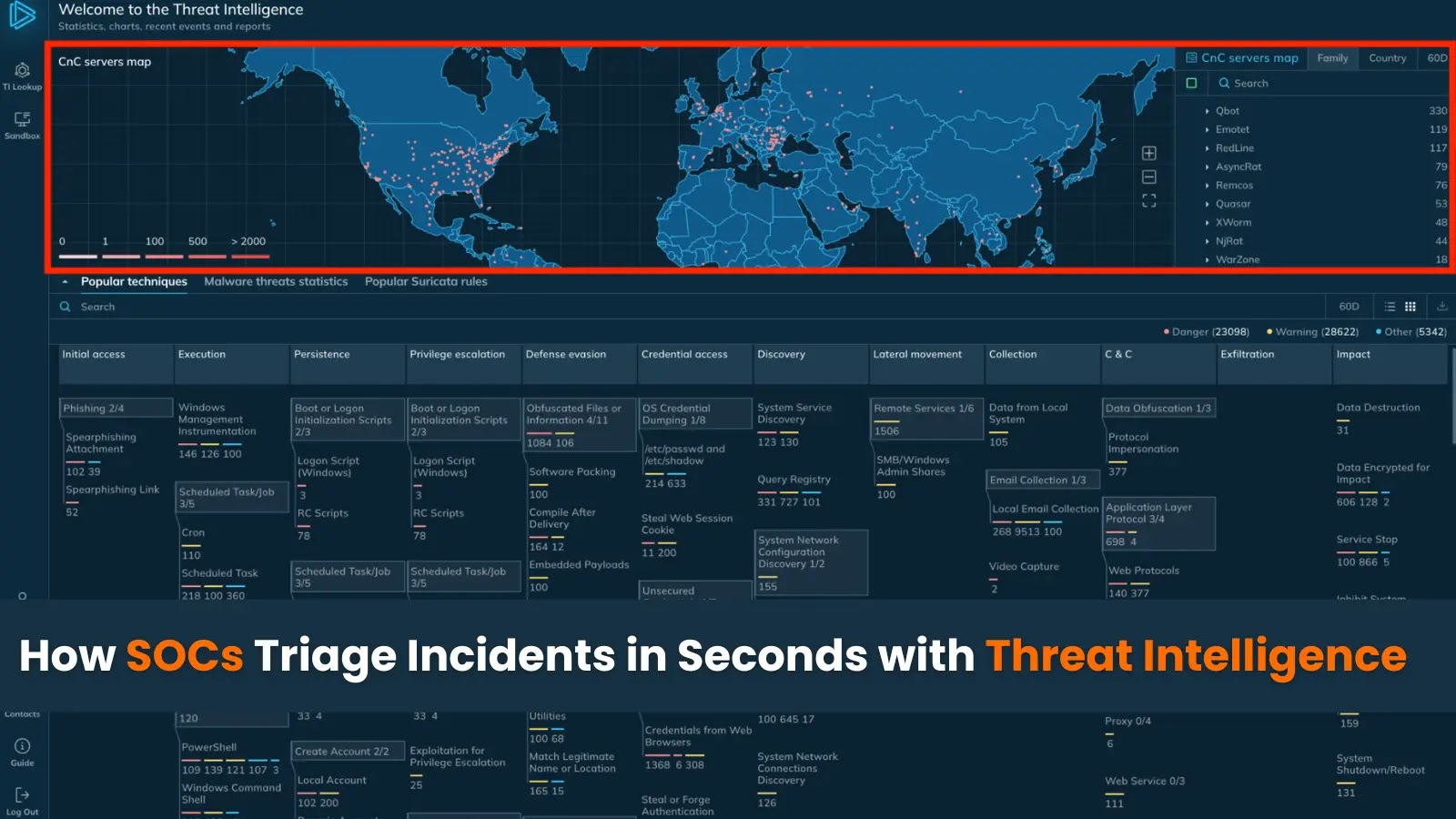
How SOCs Triage Incidents in Seconds with Threat Intelligence
How SOCs Triage Incidents in Seconds with Threat Intelligence
In the high-stakes world of cybersecurity, every second counts when responding to potential threats. Security Operations Centers (SOCs) are on the front lines, battling sophisticated adversaries who relentlessly probe defenses. The ability to triage incidents with lightning speed isn’t just an advantage; it’s a critical necessity for minimizing damage and maintaining operational integrity. This rapid response capability is largely powered by one key element: fresh, actionable threat intelligence.
This post delves into how high-performing SOC teams leverage threat intelligence to accelerate incident triage, identify relevant threat data, and understand where to acquire this crucial information—often for free.
The Imperative of Real-Time Threat Intelligence
The landscape of cyber threats is dynamic, with new attack methodologies and indicators of compromise (IOCs) emerging constantly. Outdated information renders even the most sophisticated security tools ineffective. High-performing SOCs understand this and prioritize immediate access to up-to-the-minute threat intelligence. This intelligence acts as a digital early warning system, allowing analysts to quickly identify malicious activity that would otherwise bypass traditional defenses.
Consider the recent vulnerabilities like CVE-2023-38831, a critical path traversal vulnerability in WinRAR (for more details, visit CVE-2023-38831). Without timely intelligence on such exploits, a SOC might miss early indicators of compromise related to its exploitation, leading to delayed detection and severe consequences.
Acquiring Free and Relevant Threat Data
While commercial threat intelligence feeds offer extensive data, numerous high-quality, free sources can significantly enrich a SOC’s intelligence capabilities. These open-source intelligence (OSINT) channels provide a wealth of information that, when properly processed, can be invaluable for incident triage:
- Open-Source Threat Intelligence Platforms: Projects like MISP (Malware Information Sharing Platform) allow for collaborative sharing of threat indicators.
- Government and Industry Sharing Groups: Organizations like the CISA (Cybersecurity and Infrastructure Security Agency) regularly publish advisories and IOCs related to emerging threats.
- Security Research Blogs and Forums: Many security researchers and companies share their findings on new malware, attack techniques, and vulnerabilities.
- Public Sandboxes: Services like VirusTotal compile and share analysis results for suspicious files and URLs, offering a vast repository of threat data.
- Vendor-Specific Threat Disclosures: Software and hardware vendors often release vulnerability advisories and patches, detailing new threats affecting their products.
For instance, monitoring advisories regarding a vulnerability like CVE-2023-34362, which affects the MOVEit Transfer application (information available at CVE-2023-34362), from CISA or affected vendors would provide immediate IOCs to aid detection.
Enriching Indicators and Accelerating Triage
The real power of threat intelligence lies not just in its acquisition, but in its application. When an alert fires in the SOC, analysts need to quickly determine its legitimacy and severity. This is where enriching indicators with threat intelligence becomes critical.
Here’s how SOCs leverage threat intelligence for rapid incident triage:
- Contextualization: An IP address might appear as an anomaly. Referencing it against threat intelligence feeds can immediately reveal if it’s associated with known botnets, command-and-control servers, or malicious campaigns.
- Prioritization: If an alert involves an IOC linked to a highly active ransomware group or a nation-state actor, threat intelligence elevates its priority instantly, prompting immediate investigation.
- False Positive Reduction: By cross-referencing suspicious activity with threat intelligence, SOCs can quickly distinguish between benign events and legitimate threats, reducing alert fatigue. For example, knowing that a specific domain is a legitimate content delivery network (CDN) instead of a suspected phishing site helps in rapid dismissal of false positives.
- Automated Lookups: Integrating threat intelligence platforms with SOAR (Security Orchestration, Automation, and Response) solutions allows for automated lookups of IOCs, vastly speeding up the initial triage phase.
Consider an alert flagging unusual outbound connections to an IP address. If a threat intelligence feed immediately identifies that IP as a known BlackCat ransomware C2 server, the incident’s severity escalates from “investigate” to “contain and eradicate” in moments.
Remediation Actions Driven by Intelligence
Beyond initial triage, threat intelligence directly informs effective remediation. Once a credible threat is identified, intelligence provides insights into the attacker’s tactics, techniques, and procedures (TTPs), enabling targeted containment and eradication efforts.
- Blocking Known Malicious IPs/Domains: Firewall rules and DNS blacklists can be immediately updated with IOCs from intelligence feeds.
- Patching Critical Vulnerabilities: Intelligence on actively exploited CVEs (like CVE-2023-23397, an elevation of privilege vulnerability in Microsoft Outlook, detailed at CVE-2023-23397) allows for targeted patching efforts before widespread exploitation.
- Isolating Compromised Systems: Understanding the typical lateral movement patterns gleaned from intelligence helps in isolating affected systems and preventing further spread.
- Updating Detection Rules: New intelligence data can be used to refine SIEM (Security Information and Event Management) rules and EDR (Endpoint Detection and Response) policies to detect similar future attacks more effectively.
Conclusion
The ability of a SOC to triage incidents in seconds is not a matter of luck; it’s a testament to their proactive integration and masterful application of threat intelligence. By leveraging a combination of free and commercial intelligence sources, high-performing SOC teams gain the crucial context needed to rapidly validate threats, prioritize responses, and enact decisive remediation actions. In an era where breach detection time can dictate the scale of damage, fresh and actionable threat intelligence is not just a tool—it’s the backbone of resilient cybersecurity operations.





