Magecart Hackers Uses 100+ Domains to Hijack eStores Checkouts and Steal Card Data
The Silent Threat: Magecart’s Persistent Attack on e-Commerce Checkouts
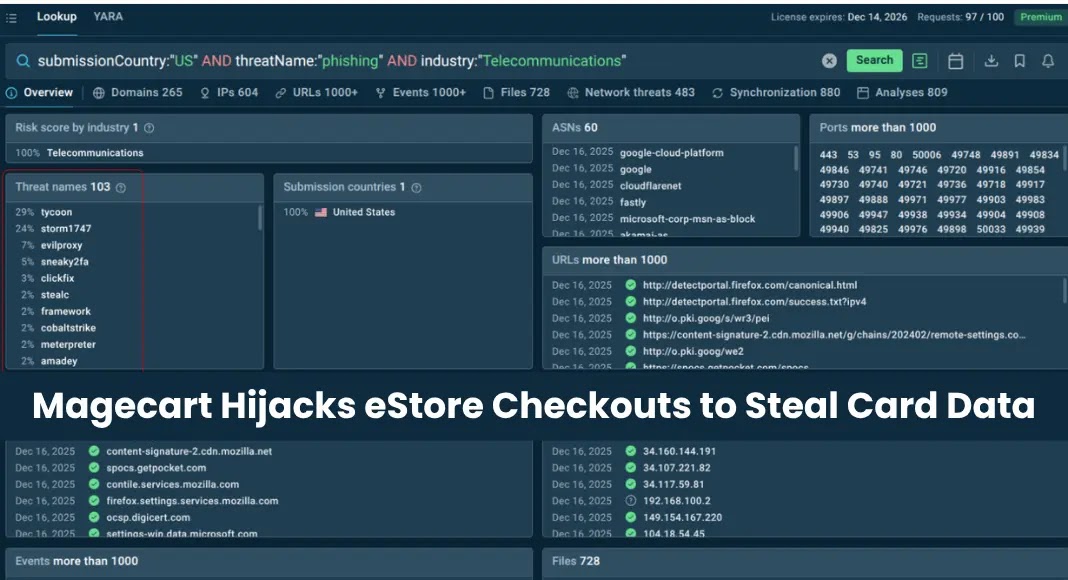
For over two years, a highly sophisticated and persistent Magecart campaign has silently compromised online retailers, siphoning off payment card data from unsuspecting customers. This long-running operation, spanning at least 12 countries and utilizing over 100 malicious domains, highlights a significant and ongoing threat to e-commerce security. While merchants grapple with the reputational damage and operational disruption, it’s financial institutions that are bearing the brunt of the financial losses from these real-time data breaches.
Understanding the Magecart Modus Operandi
Magecart is not a single entity but rather a collective term for various threat groups employing similar techniques: injecting malicious code, often JavaScript, into e-commerce websites. This code typically targets the checkout process, specifically payment forms, to skim credit card details directly as customers enter them. The stolen data, including card numbers, expiration dates, and CVVs, is then exfiltrated to attacker-controlled servers.
What makes this particular campaign so insidious is its scale and longevity. Security researchers at ANY.RUN uncovered the operation, revealing its widespread impact. The use of over 100 diverse malicious domains serves multiple purposes: it aids in evading detection by security tools and extends the attackers’ reach across a broader spectrum of targets. Each domain can host a different iteration of the skimming script or serve as a unique exfiltration point, making comprehensive blacklisting a continuous challenge. This dynamic infrastructure makes attribution and complete takedown significantly more complex for cybersecurity professionals.
Impact and Financial Fallout
The immediate impact of a Magecart attack is the theft of sensitive customer payment information. For the individual, this can lead to unauthorized transactions, identity theft, and the associated stress of fraud resolution. For merchants, beyond the immediate breach notification requirements, there’s a significant blow to customer trust and brand reputation. Recovering from such a breach involves costly forensic investigations, system remediation, and potential legal fees, not to mention the loss of future business due to customer attrition.
However, as the source highlights, the heaviest financial burden often falls on banks and other financial institutions. They are the ones who ultimately cover the costs of fraudulent transactions, issue new cards, and manage the complex process of fraud remediation for their customers. This dynamic underscores the interconnectedness of online security; a breach on one end of the transaction chain impacts multiple stakeholders throughout the financial ecosystem.
Remediation Actions and Proactive Defenses
Detecting and mitigating Magecart attacks requires a multi-layered security approach:
- Regular Security Audits: Conduct frequent, thorough security audits of your e-commerce platform, including third-party integrations and plugins. This helps identify vulnerabilities and unauthorized code modifications.
- Content Security Policy (CSP): Implement a strict Content Security Policy (CSP) to control which resources (scripts, stylesheets, images) a web page can load. This can effectively block unauthorized script injections by restricting scripts to only trusted sources.
- Subresource Integrity (SRI): For critical third-party scripts, use Subresource Integrity (SRI). This mechanism allows browsers to verify that fetched resources have not been tampered with by comparing a cryptographic hash. If the hash doesn’t match, the browser will refuse to execute the modified resource.
- Client-Side Monitoring: Employ client-side security solutions that actively monitor for malicious JavaScript activity and unauthorized changes to the DOM (Document Object Model) during checkout. These tools can detect suspicious behavior in real-time.
- Vulnerability Management: Keep all software, including your e-commerce platform, plugins, and server-side components, updated with the latest security patches. Many Magecart campaigns exploit known vulnerabilities. For instance, while not directly related to this specific campaign, vulnerabilities like CVE-2023-34036 in popular e-commerce platforms could be exploited by similar threat actors if left unaddressed.
- Strong Access Control: Implement robust access control measures for all administrative interfaces and development environments. Enforce multi-factor authentication (MFA) and regularly review user permissions.
- Endpoint Detection and Response (EDR): For internal systems connected to the e-commerce platform, deploy EDR solutions to detect and respond to suspicious activities that could indicate an initial compromise leading to Magecart injection.
- Web Application Firewalls (WAF): A WAF can help filter and monitor HTTP traffic between a web application and the Internet, potentially blocking some malicious injection attempts.
The Ongoing Battle Against Online Skimming
This long-standing Magecart campaign serves as a stark reminder that cyber threats are constantly evolving and adapting. The use of an extensive network of malicious domains demonstrates the attackers’ determination and resources. For any organization operating in the e-commerce space, proactive cybersecurity measures, continuous monitoring, and a commitment to staying informed about emerging threats are not merely best practices—they are necessities. Protecting customer data is paramount, both for maintaining trust and for safeguarding the financial stability of the broader economic system.