Malicious imToken Chrome Extension Caught Stealing Mnemonics and Private Keys
The Silent Threat: Malicious imToken Chrome Extension Steals Crypto Wallets
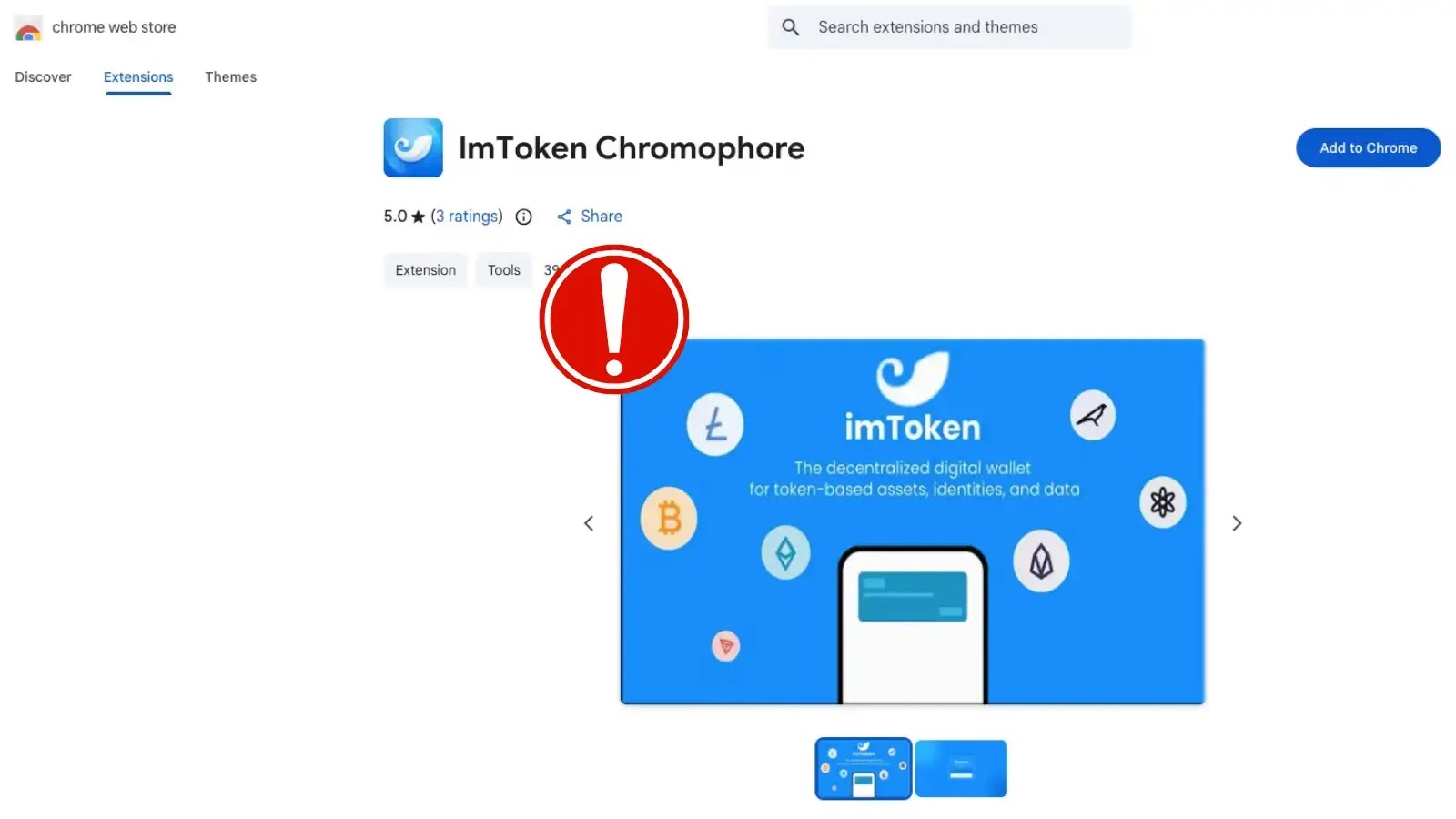
In the decentralized world of cryptocurrency, the security of your digital assets hinges on the integrity of your private keys and mnemonic phrases. Unfortunately, this critical security landscape is constantly under assault by sophisticated threats. A recent discovery by Socket’s Threat Research Team brings a stark reminder of these dangers: a malicious Google Chrome extension, deceptively named “lmΤoken Chromophore,” has been actively compromised to steal cryptocurrency wallet credentials. Masquerading as a benign hex color visualizer, this imposter targeted users of the popular non-custodial wallet brand imToken, a platform trusted by over 20 million customers since its launch in 2016.
Understanding the “lmΤoken Chromophore” Impersonation Attack
The attackers behind “lmΤoken Chromophore” employed a classic, yet highly effective, social engineering tactic combined with technical subterfuge. By creating a Chrome extension with a name visually similar to “imToken” (note the Greek letter ‘Τ’ instead of ‘T’), they aimed to capitalize on brand recognition and user trust. The extension’s purported function, a “hex color visualizer,” served as a plausible, low-suspicion cover while its true malicious purpose unfolded in the background. Users unknowingly installing this extension were granting it the necessary permissions to access sensitive browser data, including – crucially – their cryptocurrency wallet information.
How the Malicious Extension Operates
Once installed, “lmΤoken Chromophore” doesn’t immediately reveal its true nature. Its malevolent code is designed to lie in wait, monitoring user activity for specific triggers. The primary objective is to exfiltrate mnemonic phrases and private keys, which are the cryptographic foundations of a user’s cryptocurrency holdings. When a user interacts with a legitimate imToken interface or potentially other cryptocurrency-related websites, the extension intercepts this sensitive input. The extracted credentials are then covertly transmitted to attacker-controlled servers, giving the perpetrators complete control over the victim’s digital assets. This type of attack highlights the inherent risks of granting broad permissions to browser extensions without rigorous vetting.
Targeting imToken Users: A High-Value Exploit
The choice to impersonate imToken is no accident. With a vast global user base exceeding 20 million, imToken represents a significant pool of potential victims. Non-custodial wallets like imToken empower users with full control over their funds, but this also places the entire security burden on the user. When a malicious extension compromises this control, the financial repercussions can be devastating. Attackers consistently target platforms with large user penetration, amplifying their potential illicit gains.
Remediation Actions and Proactive Security Measures
Protecting yourself from sophisticated threats like “lmΤoken Chromophore” requires a multi-layered approach to cybersecurity. Here are actionable steps to safeguard your cryptocurrency holdings and digital identity:
- Immediate Removal and Wallet Transfer: If you suspect you have installed “lmΤoken Chromophore” or any suspicious crypto-related extension, immediately remove it from your browser. Furthermore, transfer all your assets from any compromised wallet to a new, secure wallet whose private keys and seed phrase were generated in an uncompromised environment.
- Exercise Extreme Caution with Browser Extensions: Only install extensions from official, verified sources (e.g., the official Chrome Web Store entry linked directly from the developer’s website). Scrutinize reviews, developer information, and the number of users. Be wary of extensions with generic descriptions or low user counts.
- Verify Extension Permissions: Before installing any extension, carefully review the permissions it requests. Does a hex color visualizer truly need access to “read and change all your data on websites”? If the requested permissions seem excessive or unrelated to the extension’s stated purpose, do not install it.
- Hardware Wallets: For significant cryptocurrency holdings, invest in a hardware wallet (e.g., Ledger, Trezor). These devices store your private keys offline, making them impervious to browser-based malware and extensions.
- Multiple Wallets and Diversification: Avoid keeping all your assets in one wallet. Use separate wallets for different purposes (e.g., spending, long-term holding). This limits potential losses if one wallet is compromised.
- Regular Security Audits: Periodically review your installed browser extensions and revoke permissions for those you no longer use or trust. Keep your browser and operating system updated to patch known vulnerabilities.
- Stay Informed: Follow reputable cybersecurity news sources and cryptocurrency security alerts. Awareness of new threats is your first line of defense.
Relevant Tools for Detection and Mitigation
While direct detection of this specific malware might require advanced techniques, several tools and practices can help improve your overall security posture and potentially identify suspicious activity:
| Tool Name | Purpose | Link |
|---|---|---|
| Browser’s Extension Manager | Review and uninstall installed extensions. | chrome://extensions/ |
| VirusTotal | Analyze suspicious files/URLs for malware. | https://www.virustotal.com/ |
| uBlock Origin / Privacy Badger | Block malicious scripts and trackers. | https://ublockorigin.com/ (uBlock Origin) |
| Hardware Wallet Providers | Offline private key storage for enhanced security. | https://www.ledger.com/ (Ledger) |
Conclusion: Vigilance is Key in the Crypto Landscape
The “lmΤoken Chromophore” incident underscores a critical reality: the threat landscape for cryptocurrency users is intricate and constantly evolving. Adversaries will continue to leverage social engineering, brand impersonation, and technical exploits to compromise digital assets. By understanding these attack vectors, adopting stringent security practices, and staying informed about emerging threats, users can significantly reduce their risk exposure. Always prioritize verifying the authenticity of software and exercising extreme caution when handling your sensitive cryptocurrency credentials. Your vigilance is the strongest shield against these digital predators.





