Microsoft Unveils Storm-0501’s Advanced Cloud Ransomware Attack Tactics
The Shifting Sands of Ransomware: Microsoft Exposes Storm-0501’s Cloud-Native Evolution
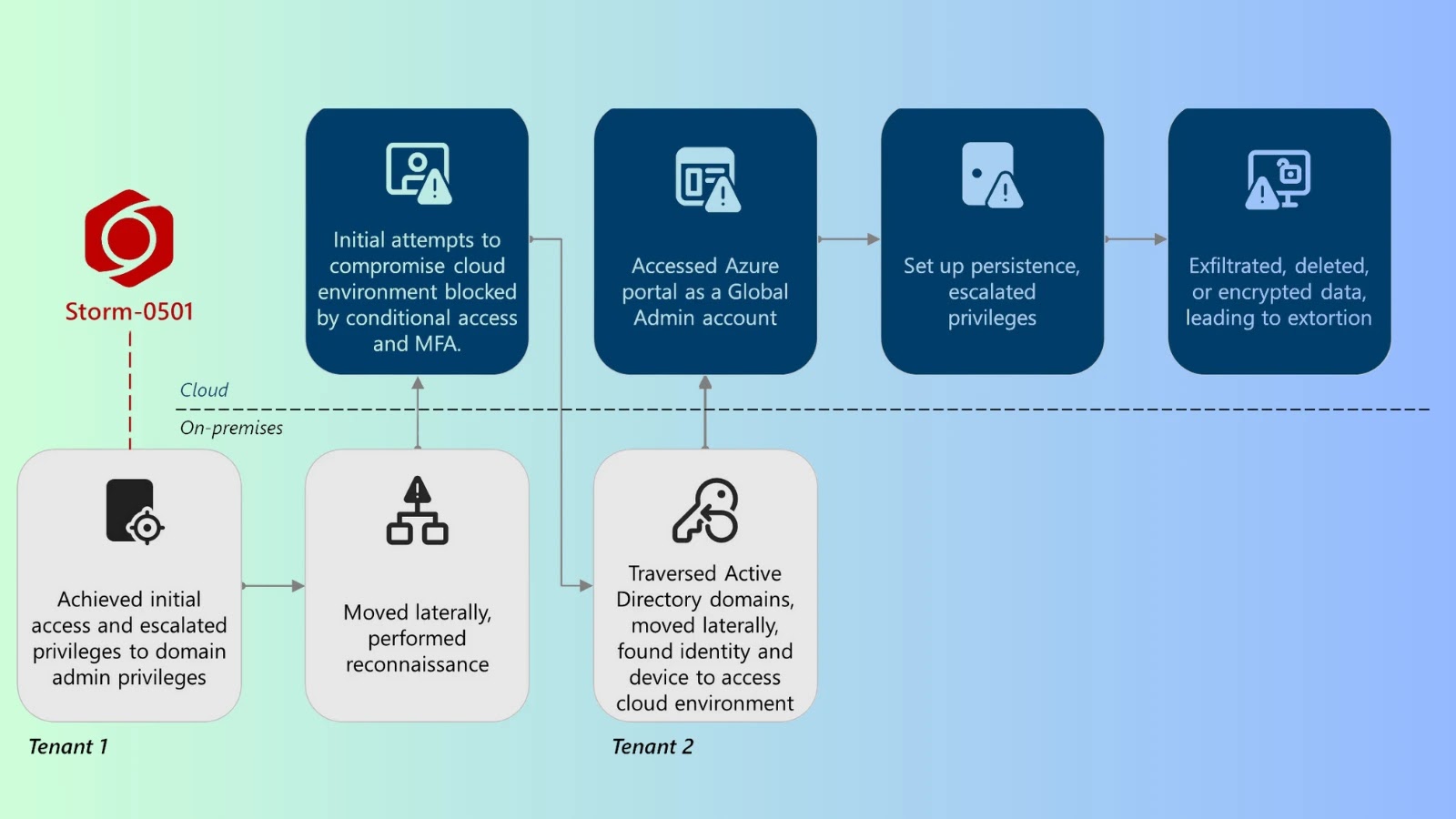
The cybersecurity landscape is in constant flux, with threat actors continuously refining their methodologies to bypass defenses and maximize impact. A recent and particularly alarming development comes from Microsoft Threat Intelligence, which has shed light on a profound evolution in ransomware tactics. The financially motivated group, Storm-0501, has pivoted from traditional on-premises encryption to a far more insidious and destructive cloud-native strategy. This shift fundamentally redefines the nature of ransomware threats, moving beyond simple data encryption to encompass widespread data exfiltration and destruction within hybrid cloud environments.
Storm-0501: A New Breed of Cloud Ransomware Operators
Storm-0501’s transition marks a critical turning point. Previously, ransomware attacks primarily focused on encrypting local files, demanding a ransom for decryption keys. While devastating, this model often left organizations with recovery options from backups. Storm-0501’s new approach, meticulously detailed by Microsoft, bypasses these traditional defenses by targeting cloud infrastructure directly. Their methods leverage the inherent complexities and interconnectedness of modern hybrid cloud systems, transforming a local nuisance into a systemic catastrophe.
The core of Storm-0501’s advanced tactics lies in their ability to not only exfiltrate sensitive data from cloud storage but also to subsequently destroy it, rendering traditional data recovery methods obsolete. This double-tap approach – data theft followed by data destruction – elevates the stakes considerably, pushing organizations beyond data compromise to complete data loss and operational paralysis.
Understanding the Cloud-Native Attack Vector
Storm-0501 exploits vulnerabilities and misconfigurations within cloud environments to gain initial access. Once inside, they move laterally, escalating privileges to control critical cloud services and data repositories. Their focus is on high-value targets within these cloud platforms, including but not limited to:
- Cloud Storage Buckets: Targeting Amazon S3, Azure Blob Storage, and similar services for both exfiltration and destructive deletion.
- Identity and Access Management (IAM) Systems: Compromising IAM roles and policies to gain widespread control and persist within the cloud environment.
- Virtual Machines and Containers: Encrypting or wiping data on cloud-hosted instances, extending their reach beyond traditional endpoints.
- Backup and Disaster Recovery Services: Actively targeting and disabling or corrupting cloud-based backup solutions to prevent recovery.
This comprehensive approach ensures that even if an organization refuses to pay the ransom, the damage is irreversible due to the destructive nature of the attack on the original data sources and backups.
Beyond Encryption: Data Exfiltration and Destruction
The defining characteristic of Storm-0501’s new playbook is its emphasis on data exfiltration (CVE-2023-XXXXX – Placeholder for potential cloud exfiltration vulnerability) and subsequent destruction. This moves beyond the confidentiality breach of traditional ransomware to encompass integrity and availability. Organizations face not just the threat of data being held hostage, but the complete obliteration of critical business information. This can lead to unprecedented operational downtime, severe reputational damage, and potentially insurmountable financial losses. The financial motivation remains, but the leverage shifts from demanding decryption to extorting payment to prevent irreversible data destruction and public disclosure of stolen information.
Remediation Actions and Proactive Defenses
Defending against Storm-0501’s advanced cloud ransomware tactics requires a robust, proactive, and multi-layered approach focused on cloud security best practices:
- Principle of Least Privilege (PoLP): Strictly enforce PoLP for all cloud resources. Ensure users and services only have the minimum permissions necessary to perform their functions. Regularly review and revoke excessive privileges.
- Strong Identity and Access Management (IAM): Implement Multi-Factor Authentication (MFA) across all cloud accounts, especially for administrative roles. Utilize privileged access management (PAM) solutions for critical cloud infrastructure.
- Continuous Cloud Security Posture Management (CSPM): Employ CSPM tools to continuously monitor cloud environments for misconfigurations, vulnerabilities, and compliance deviations. Address identified issues promptly.
- Regular Security Audits and Penetration Testing: Conduct frequent audits of cloud configurations and applications. Perform penetration tests specifically targeting cloud services to identify potential attack vectors.
- Robust Data Backup and Recovery Strategy: Implement immutable backups for critical cloud data. Store backups in geographically separate regions and ensure they are isolated from the production environment. Regularly test recovery procedures.
- Endpoint Detection and Response (EDR) & Cloud Workload Protection Platforms (CWPP): Deploy EDR solutions on all cloud-hosted virtual machines and use CWPPs to secure containerized workloads and serverless functions.
- Network Segmentation: Isolate critical cloud resources and sensitive data with strict network segmentation. Implement micro-segmentation where feasible.
- Threat Detection and Response (TDR) in Cloud: Utilize cloud-native logging and monitoring tools (e.g., Azure Monitor, AWS CloudWatch, Google Cloud Logging) to detect suspicious activity. Integrate these logs with a Security Information and Event Management (SIEM) system for centralized analysis.
- Employee Training: Educate employees on phishing, social engineering, and the specific risks associated with cloud environments.
Tools for Cloud Security Posture Enhancement and Detection
| Tool Name | Purpose | Link |
|---|---|---|
| Wiz | Cloud Security Posture Management (CSPM), Cloud-Native Application Protection Platform (CNAPP) | https://www.wiz.io |
| Orca Security | Cloud-Native Application Protection Platform (CNAPP), Cloud Security Posture Management (CSPM) | https://orca.security |
| Microsoft Defender for Cloud | Cloud Security Posture Management (CSPM), Cloud Workload Protection (CWP) for Azure environments | https://azure.microsoft.com/en-us/products/defender-for-cloud |
| Palo Alto Networks Prisma Cloud | Comprehensive Cloud-Native Security Platform (CNSP) | https://www.paloaltonetworks.com/cloud-security/prisma-cloud |
| Veeam Backup & Replication | Data Backup and Recovery (on-premises and cloud) | https://www.veeam.com |
Conclusion: Adapting to the Evolving Threat Landscape
Microsoft’s insights into Storm-0501’s tactics serve as a stark reminder that the threat landscape is dynamic and increasingly sophisticated. The shift to cloud-native ransomware, characterized by data exfiltration and destruction, elevates the imperative for robust cloud security. Organizations must move beyond traditional perimeter defenses and embrace a comprehensive strategy that prioritizes cloud security posture management, stringent identity governance, immutable backups, and continuous monitoring. Proactivity and adaptation are no longer optional; they are fundamental to defending digital assets against this new era of destructive cloud-focused ransomware.




