New CanisterWorm Steals npm Tokens and Spreads Through Compromised Publisher Accounts
The digital supply chain is a prime target for threat actors, and a critical component like the npm ecosystem is no exception. A new, insidious self-propagating malware campaign dubbed CanisterWorm is actively stealing npm tokens and spreading rapidly through compromised publisher accounts. This sophisticated threat highlights the escalating risks in open-source software supply chains and demands immediate attention from developers and security professionals.
What is CanisterWorm?
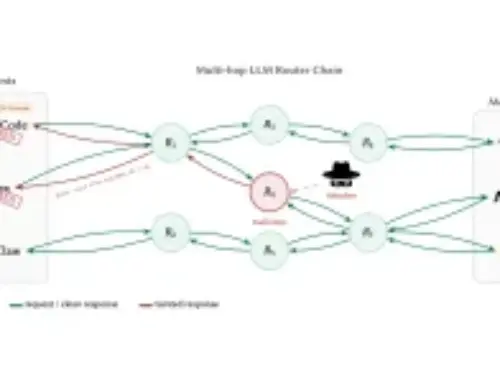
CanisterWorm is a newly discovered npm supply chain attack that leverages compromised publisher namespaces to inject malicious code into trusted packages. Operated by a group identified as “TeamPCP,” this malware campaign turns legitimate developer tools into stealthy mechanisms for credential theft. The core purpose of CanisterWorm is to quietly exfiltrate sensitive npm tokens, granting attackers unauthorized access to developer accounts and potentially enabling further compromise of critical infrastructure.
The attack vector is particularly concerning because it exploits the trust inherent in the open-source ecosystem. By compromising legitimate publisher accounts, TeamPCP can push poisoned versions of existing packages or introduce new malicious ones, which then spread when developers integrate these seemingly benign updates into their projects.
How CanisterWorm Spreads and Operates
The self-propagating nature of CanisterWorm is a key characteristic. Once a publisher account is compromised, the malware can take several actions:
- Publish Malicious Package Versions: TeamPCP can push new versions of existing, popular packages that include the CanisterWorm payload. Developers then unknowingly download and execute this malicious code when updating their dependencies.
- Create New Malicious Packages: The attackers might also publish entirely new npm packages designed to lure developers, which, upon installation, execute the token-stealing code.
- Automated Propagation: The malware is engineered to search for and compromise additional npm accounts using stolen tokens, creating a cascading effect that broadens its reach across the npm ecosystem. This automation significantly accelerates its spread and impact.
The primary payload focuses on stealing npm tokens. These tokens are crucial for authentication and authorization within the npm registry, allowing users to publish, unpublish, and manage packages. With stolen tokens, attackers gain significant control, potentially leading to further supply chain compromises, intellectual property theft, or even the injection of backdoors into widely used applications.
Target Audience and Potential Impact
Anyone using npm packages in their development workflow is a potential target. This includes:
- Software Developers: Directly affected by the compromise of packages they rely on for their projects.
- Open-Source Project Maintainers: Their accounts are prime targets for compromise, leading to their trusted packages being weaponized.
- Organizations Using npm: Companies that build applications with npm dependencies face the risk of integrating malicious code into their software, potentially leading to data breaches or system compromise.
The impact can range from unauthorized access to developer accounts and intellectual property theft to the widespread deployment of backdoors in applications used by millions. Such an attack severely erodes trust in the open-source community and has significant financial and reputational consequences for affected organizations.
Remediation Actions and Best Practices
Mitigating the threat of CanisterWorm and similar supply chain attacks requires a multi-layered approach. Developers and organizations must adopt robust security practices:
- Enable Multi-Factor Authentication (MFA): Mandate MFA for all npm accounts, especially for publisher accounts. This significantly reduces the risk of account compromise even if passwords are stolen.
- Regularly Revoke and Regenerate npm Tokens: npm tokens should be considered sensitive credentials. Regularly rotate them, and revoke any tokens that are no longer in use or could have been exposed.
- Implement Supply Chain Security Tools: Utilize tools that scan for known vulnerabilities and suspicious activity in your npm dependencies.
- Pin Dependency Versions: Avoid using broad version ranges (e.g.,
^1.0.0or*) for critical dependencies. Instead, pin to specific versions (e.g.,1.0.3) to prevent automatic updates to potentially malicious versions. - Audit Package Integrity: Before deploying, verify the integrity of downloaded packages, perhaps by checking their hashes against known good versions.
- Implement Least Privilege: Grant npm tokens only the necessary permissions. If a token only needs to publish, ensure it doesn’t have read access to sensitive data.
- Stay Informed: Keep abreast of the latest threats and vulnerabilities in the npm ecosystem. Follow security advisories from npm and credible cybersecurity news outlets like Cyber Security News.
- Segment Development Environments: Isolate development environments to limit the blast radius if one environment is compromised.
Detection and Prevention Tools
Several tools can assist in detecting malicious packages and strengthening npm supply chain security:
| Tool Name | Purpose | Link |
|---|---|---|
| npm audit | Scans project dependencies for known vulnerabilities and provides recommendations. | https://docs.npmjs.com/cli/v9/commands/npm-audit |
| Snyk | Identifies vulnerabilities in open-source dependencies and containers. | https://snyk.io/ |
| Dependabot (GitHub) | Automated dependency updates and vulnerability scanning for GitHub repositories. | https://docs.github.com/en/code-security/dependabot/dependabot-security-updates/about-dependabot-security-updates |
| OWASP Dependency-Check | Identifies project dependencies and checks for known vulnerabilities. | https://owasp.org/www-project-dependency-check/ |
| Renovate | Automated dependency update bot with security features. | https://www.mend.io/free-developer-tools/renovate/ |
Conclusion
The emergence of CanisterWorm serves as a stark reminder of the persistent and evolving threat landscape within the software supply chain. Attacks targeting open-source ecosystems like npm pose significant risks due to their broad reach and the inherent trust placed in widely used packages. Proactive measures, including strong authentication, diligent dependency management, and continuous security scanning, are no longer optional but essential for safeguarding development workflows and the integrity of software products. Developers and organizations must remain vigilant, implement robust security practices, and stay informed about the latest threats to protect against sophisticated adversaries like TeamPCP.