PoC Exploit Released for Windows Error Reporting ALPC Privilege Escalation
Unpacking CVE-2026-20817: A Critical Windows ALPC Privilege Escalation
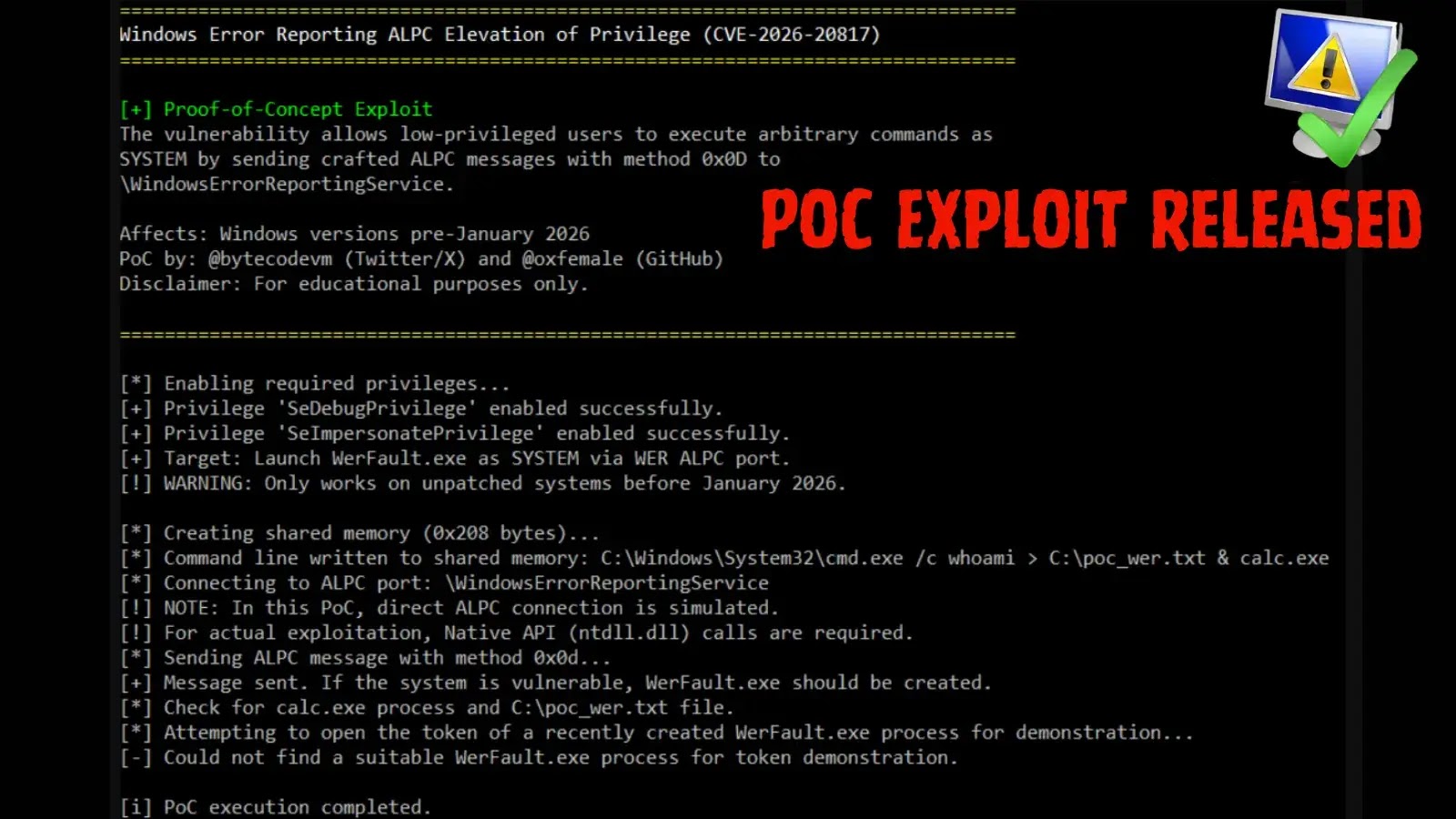
A significant local privilege escalation (LPE) vulnerability, tracked as CVE-2026-20817, has recently emerged, posing a substantial risk to Microsoft Windows environments. This critical flaw, residing within the Windows Error Reporting (WER) service, allows a low-privileged, authenticated user to execute arbitrary code with full SYSTEM privileges. The public release of a Proof-of-Concept (PoC) exploit elevates the urgency for immediate awareness and remediation. Understanding the mechanics of this vulnerability is crucial for defending against potential exploitation.
The Windows Error Reporting (WER) Service and ALPC
The Windows Error Reporting (WER) service is an integral component of the operating system, designed to collect and send crash or hang data to Microsoft. This service utilizes Advanced Local Procedure Call (ALPC), a highly efficient inter-process communication (IPC) mechanism within Windows. ALPC allows different processes, including those with varying privilege levels, to communicate securely and exchange data. While essential for system stability and diagnostics, the complexity of IPC mechanisms like ALPC can, at times, introduce overlooked security weaknesses.
In the context of CVE-2026-20817, the vulnerability specifically leverages a weakness in how the WER service handles ALPC communications. This flaw permits an attacker, already present on the system with standard user rights, to manipulate the service’s functions, ultimately leading to elevated privileges.
Understanding the Privilege Escalation Mechanism
Local privilege escalation vulnerabilities like CVE-2026-20817 are particularly dangerous because they allow an attacker to move from a limited execution environment to full administrative control. Once an attacker has gained a foothold on a system, even with low privileges, an LPE vulnerability can provide the necessary access to:
- Execute malicious payloads with SYSTEM-level permissions.
- Install rootkits or persistent backdoors.
- Disable security software.
- Access sensitive data stored on the system.
- Move laterally within a network.
The PoC exploit demonstrates how an authenticated user can interact with the WER service’s ALPC ports in an unintended way. This interaction misleads the service into performing actions or executing code under its highly privileged context, effectively granting the attacker the same SYSTEM privileges. The public availability of this PoC significantly lowers the bar for potential attackers, making timely patching imperative.
Remediation Actions and Mitigations
Addressing CVE-2026-20817 requires prompt action from system administrators and security teams. The primary remediation strategy will be applying the official security update from Microsoft as soon as it becomes available. In the interim, and as a best practice, consider the following:
- Apply Vendor Patches: Monitor Microsoft’s security advisories and promptly apply the official patch for CVE-2026-20817 when released. This is the most effective long-term solution.
- Principle of Least Privilege: Ensure all user accounts and applications operate with the absolute minimum privileges required to perform their functions. This limits the impact of an LPE if a low-privileged account is compromised.
- Endpoint Detection and Response (EDR): Utilize EDR solutions to detect anomalous process behavior, unauthorized privilege escalation attempts, and suspicious interactions with system services like WER.
- Regular Security Audits: Conduct frequent security audits and vulnerability scans to identify potential weaknesses and misconfigurations.
- Network Segmentation: Implement network segmentation to contain the potential damage from a compromised endpoint, preventing lateral movement even if SYSTEM privileges are obtained locally.
Tools for Detection and Mitigation
While awaiting a definitive patch, several security tools and practices can aid in detection and overall system hardening:
| Tool Name | Purpose | Link |
|---|---|---|
| Windows Event Viewer | Review Security, System, and Application logs for anomalous activity related to process creation, service interaction, or privilege changes. | Microsoft Docs |
| Sysmon | Provides detailed information about process creation, network connections, and changes to file creation time. Useful for detecting suspicious activity. | Microsoft Sysinternals |
| Vulnerability Scanners (e.g., Nessus, OpenVAS) | Identify unpatched systems and other configuration weaknesses. Ensure regular scans are performed. | Tenable Nessus / OpenVAS |
| Endpoint Detection & Response (EDR) Solutions | Proactive threat hunting and detection of unusual process execution, privilege escalation attempts, and command-and-control communication. | (Vendor Specific – e.g., CrowdStrike, SentinelOne) |
Conclusion
The public release of a PoC exploit for CVE-2026-20817, affecting the Windows Error Reporting service via ALPC, represents a significant immediate threat to Windows environments. This vulnerability’s ability to escalate privileges from a low-level authenticated user to full SYSTEM control underscores the need for vigilant security practices. Timely application of vendor patches, adherence to the principle of least privilege, and robust endpoint security solutions are critical to mitigating the risks posed by this and similar local privilege escalation flaws.