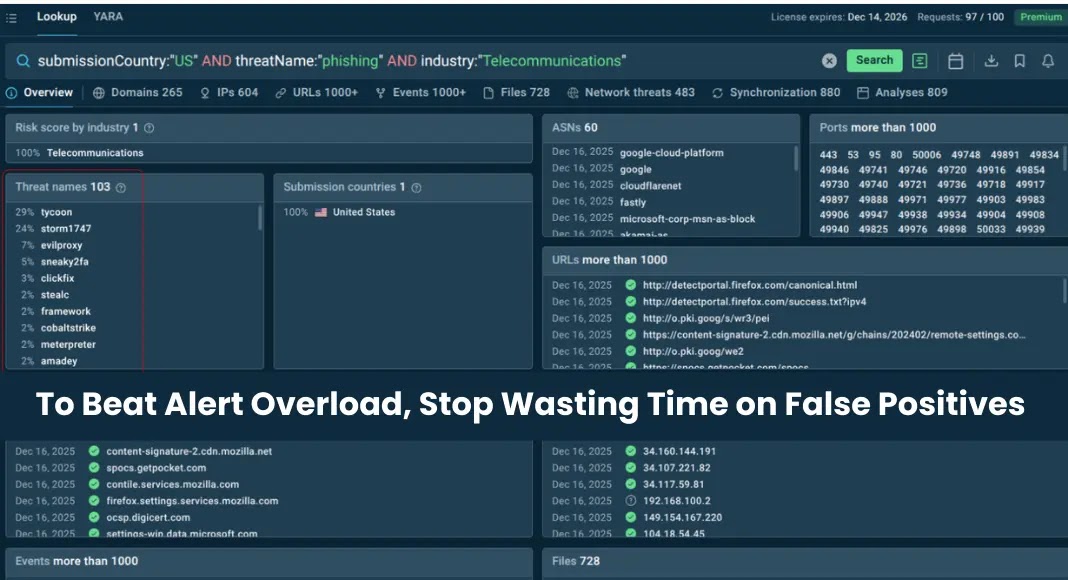
To Beat Alert Overload, Stop Wasting Time on False Positives
In the high-stakes world of cybersecurity, a constant stream of alerts can feel like a badge of honor. It suggests your detection systems are working diligently, flagging potential threats around the clock. An alert fires, a Security Operations Center (SOC) analyst investigates, only to discover it’s nothing malicious – a classic false positive. Case closed. Systems are safe, detection works, and the organization breathes a collective sigh of relief. This scenario, at face value, appears to be a healthy, “better safe than sorry” approach.
However, this seemingly benign process carries a hidden cost that few organizations fully acknowledge until it’s too late: alert overload. Every false alert, no matter how minor, consumes valuable time. Each investigation diverts critical attention from genuine, stealthier threats. And every unnecessary escalation chips away at the morale and efficiency of your security team. This isn’t just about inconvenience; it’s a fundamental drain on resources and a significant hindrance to proactive threat hunting. The key to effective cybersecurity isn’t more alerts; it’s fewer, higher-fidelity alerts that truly matter.
The Deceptive Comfort of False Positives
False positives, while initially seeming reassuring, actively undermine the very efficacy of your security posture. They create a “cry wolf” syndrome within your SOC team. When analysts are constantly sifting through noise, their ability to quickly identify and respond to real incidents diminishes. This isn’t theoretical; it’s a documented challenge impacting security teams globally. Consider the implications:
- Resource Drain: Each false positive requires human intervention. Investigation, analysis, and documentation. This ties up highly skilled analysts who could be focusing on strategic security initiatives or genuine threat intelligence.
- Reduced Efficiency: The sheer volume of alerts, many of them benign, slows down the mean time to detect (MTTD) and mean time to respond (MTTR) for actual breaches. Critical seconds or minutes are lost sifting through irrelevant data.
- Analyst Burnout: The constant grind of investigating trivial alerts leads to frustration, demoralization, and eventually, burnout among SOC personnel. This impacts retention rates and overall team effectiveness.
- Blind Spots: While chasing ghosts, real threats can slip through undetected because resources are misallocated, and critical signals are obscured by the noise.
Understanding the Root Causes of Alert Overload
Alert overload isn’t a problem without solutions; it’s a symptom of underlying issues within a security ecosystem. Identifying these causes is the first step towards remediation:
- Poorly Configured Tools: Security Information and Event Management (SIEM) systems and Intrusion Detection Systems (IDS/IPS) often come with default rulesets that generate excessive alerts. Without fine-tuning, these tools are more noisy than effective.
- Lack of Context: Alerts often fire in isolation without the necessary business or environmental context to determine their true severity. An unusual login from a known remote employee traveling abroad, for instance, might trigger an alert without integration with HR or travel data.
- Outdated Signatures and Rules: Reliance on static signatures for threat detection can lead to numerous false positives as legitimate software updates or infrastructure changes trigger old rules.
- Inadequate Baselines: Without a clear understanding of normal network traffic and user behavior, any deviation can trigger an alert, even if it’s perfectly legitimate.
- Integration Gaps: Disconnected security tools operating in silos can generate duplicate alerts or fail to correlate events, leading to a fragmented and overwhelming alert stream.
Remediation Actions: Strategies to Combat False Positives
Addressing false positives requires a multi-faceted approach, blending technical adjustments with strategic operational improvements. The goal is to elevate the signal-to-noise ratio, ensuring your security team focuses on high-fidelity alerts that genuinely represent a threat.
- Baseline Normal Behavior: Establish a clear baseline of expected network traffic, user activities, and system configurations. This allows your security tools to accurately distinguish between normal deviations and truly anomalous, potentially malicious, events. Leverage network performance monitoring tools and user behavior analytics (UBA) for this.
- Refine SIEM Rules and Policies: Continuously review and optimize your SIEM rules. Prioritize alerts based on criticality, asset value, and likelihood of being a true positive. Consider using a common vulnerability scoring system (CVSS) to prioritize alerts related to known vulnerabilities, for example, addressing critical issues like CVE-2023-46805 (a critical Ivanti Connect Secure vulnerability) or CVE-2023-22518 (a critical Atlassian Confluence vulnerability) as highest priority.
- Integrate Threat Intelligence: Incorporate up-to-date threat intelligence feeds into your detection systems. This helps differentiate between known benign activities and indicators of compromise (IoCs) associated with active threats.
- Leverage Automation and Orchestration: Implement Security Orchestration, Automation, and Response (SOAR) platforms to automate the initial triage and enrichment of alerts. This can automatically dismiss well-known false positives or gather additional context for deeper analysis, freeing up human analysts for more complex investigations.
- Contextual Enrichment: Ensure your alerts are enriched with relevant context, such as asset ownership, business criticality, user roles, and recent changes. This can be achieved through integrations with CMDBs, identity management systems, and change management platforms.
- Regularly Review and Tune IPS/IDS Signatures: Avoid a “set it and forget it” mentality. Regularly review and update IDS/IPS signatures, disabling those that frequently trigger false positives in your environment and enabling new ones relevant to emerging threats.
- Implement User and Entity Behavior Analytics (UEBA): UEBA solutions are specifically designed to detect anomalous behavior by learning patterns of “normal” behavior for users and entities. This drastically reduces false positives associated with unusual but legitimate activity.
- Conduct Purple Teaming Exercises: Simulate real-world attacks (red teaming) and work collaboratively with your detection and response team (blue team) to identify gaps in detection and areas generating excessive false positives. This iterative process refines your security controls.
Conclusion
The pursuit of comprehensive cybersecurity shouldn’t come at the cost of operational efficiency. Alert overload, fueled by an abundance of false positives, is a silent drain on resources, a breeding ground for analyst burnout, and a dangerous distraction from genuine threats. By moving beyond the deceptive comfort of “better safe than sorry” and proactively implementing strategies to reduce false positives, organizations can transform their security operations. The goal is not merely to detect more, but to detect smarter – ensuring that every alert that crosses an analyst’s dashboard is a credible signal, demanding immediate and focused attention. This shift empowers security teams to be proactive defenders, rather than reactive firefighters constantly battling phantom blazes.