RMM Tools Essential for IT Operations but Increasingly Weaponized by Attackers
Remote Monitoring and Management (RMM) tools are the unsung heroes of modern IT operations. For countless security professionals and system administrators, these platforms are indispensable, enabling seamless system patching, proactive troubleshooting, and comprehensive network management from virtually any location. They promise speed, unparalleled control, and crucial convenience—attributes that are highly prized in today’s fast-paced IT environments. Yet, the very features that have solidified RMM tools as operational mainstays are precisely what have made them increasingly attractive targets, and potent weapons, for sophisticated attackers.
The Dual Nature of RMM Tools: Efficiency vs. Exposure
RMM platforms offer a centralized console to oversee and interact with numerous endpoints, servers, and network devices. This capability is invaluable for managing distributed workforces and complex infrastructures. Think of the critical tasks performed daily: deploying software updates, applying security patches, monitoring system health, and resolving user issues remotely. Without RMM tools, IT teams would be crippled, struggling to maintain uptime and security across their environments.
However, this high level of access and control inherently presents a significant security risk. An RMM agent, typically installed with elevated privileges on remote systems, acts as a direct conduit to the underlying infrastructure. If an attacker gains unauthorized access to an RMM platform, they effectively acquire a master key to an organization’s entire digital kingdom.
Weaponization of RMM: How Attackers Exploit Essential Tools
The weaponization of RMM tools isn’t a theoretical concern; it’s a documented and growing threat. Attackers recognize that compromising an RMM platform allows them to bypass traditional perimeter defenses and directly inject malicious code, deploy ransomware, or exfiltrate sensitive data across an entire managed network, often without triggering immediate alerts. The trust inherent in RMM operations, where agents are expected to communicate frequently with the central server, can be manipulated to facilitate covert operations.
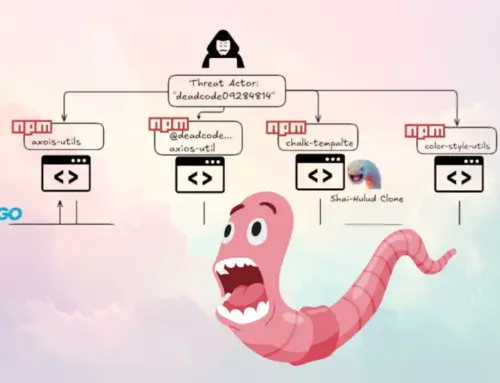
Recent incidents have demonstrated this, with threat actors leveraging legitimate RMM access to execute devastating supply chain attacks. By compromising an MSP’s RMM tool, attackers can then propagate malware to all the MSP’s clients, amplifying the impact exponentially. This transforms a targeted breach into a widespread catastrophe, affecting potentially hundreds or thousands of organizations simultaneously.
Common Attack Vectors and Vulnerabilities
- Weak Authentication: A primary weakness remains the use of weak passwords or single-factor authentication on RMM portals. Attackers routinely target these with brute-force attacks or credential stuffing.
- Exploitable Vulnerabilities in RMM Software: Like any complex software, RMM platforms can have vulnerabilities. Attackers actively seek out and exploit these to gain initial access. For instance, vulnerabilities such as CVE-2022-26166 or CVE-2022-28045 in popular RMM solutions have been identified and patched, but organizations lagging on updates remain exposed.
- Social Engineering: Phishing attacks targeting RMM administrators are highly effective, tricking IT personnel into divulging credentials.
- Insider Threats: While less common, disgruntled employees with RMM access can pose a severe risk.
Remediation Actions and Best Practices
Mitigating the risk associated with RMM tools requires a multi-layered approach, balancing operational efficiency with robust security controls. Organizations can’t simply abandon RMM; instead, they must secure its use with diligence.
- Enforce Multi-Factor Authentication (MFA): This is non-negotiable for all RMM users, especially administrative accounts. MFA significantly reduces the risk of credential compromise.
- Regular Patching and Updates: Keep RMM software, agents, and underlying operating systems fully patched. Monitor vendor security advisories diligently.
- Strong Access Controls and Least Privilege: Implement granular role-based access control (RBAC). Ensure IT staff only have the minimum necessary permissions to perform their duties. Avoid using highly privileged accounts for routine tasks.
- Network Segmentation: Isolate RMM infrastructure from the broader corporate network. Restrict RMM agent communication to only necessary ports and protocols.
- Audit and Log Monitoring: Continuously monitor RMM activity logs for unusual behavior, unauthorized access attempts, or atypical command executions. Integrate RMM logs into a SIEM solution for centralized analysis.
- Endpoint Detection and Response (EDR): Deploy EDR solutions on all endpoints managed by RMM tools. EDR can detect and alert on suspicious activities originating from RMM agents, even if the agent itself is compromised.
- Incident Response Plan: Develop and regularly test an incident response plan specifically addressing RMM compromise scenarios.
- Security Awareness Training: Educate IT staff on the latest social engineering tactics and the importance of strong security hygiene.
Tools for Detection and Mitigation
| Tool Name | Purpose | Link |
|---|---|---|
| SIEM Solutions (e.g., Splunk, Microsoft Sentinel) | Centralized log collection, correlation, and analysis for detecting anomalies in RMM activity. | Splunk |
| Endpoint Detection and Response (EDR) Solutions (e.g., CrowdStrike Falcon, SentinelOne) | Detecting and responding to malicious activities originating from RMM agents on endpoints. | CrowdStrike |
| Vulnerability Scanners (e.g., Nessus, Qualys) | Identifying unpatched RMM software vulnerabilities on servers and endpoints. | Nessus |
| MFA Solutions (e.g., Duo Security, Okta) | Implementing strong multi-factor authentication for RMM access. | Duo Security |
Conclusion
RMM tools are critical enablers of efficiency in modern IT, but their inherent power makes them prime targets for sophisticated attackers. Organizations must move beyond simply deploying these tools and instead treat them as high-value assets requiring stringent security measures. By implementing robust authentication, vigilant patching, granular access controls, and continuous monitoring, IT professionals can harness the benefits of RMM while significantly reducing the risk of weaponization. The imperative is clear: secure your RMM, or risk your entire IT estate.