BoryptGrab Stealer Spreads via Fake GitHub Repositories, Stealing Browser and Crypto Wallet Data
Unmasking BoryptGrab: The Stealer Lurking in Fake GitHub Repositories
The digital landscape is a constant battleground, and a new threat, BoryptGrab, has emerged from the shadows, silently compromising Windows systems. This sophisticated data stealer has been actively spreading since at least April 2025, cleverly leveraging a network of fake GitHub repositories to ensnare unsuspecting users. Its primary targets? Your sensitive browser data and highly valuable cryptocurrency wallet information. This blog post delves into the mechanics of BoryptGrab, its deceptive distribution tactics, and crucial measures to protect your digital assets.
The Deceptive Lure: How BoryptGrab Operates
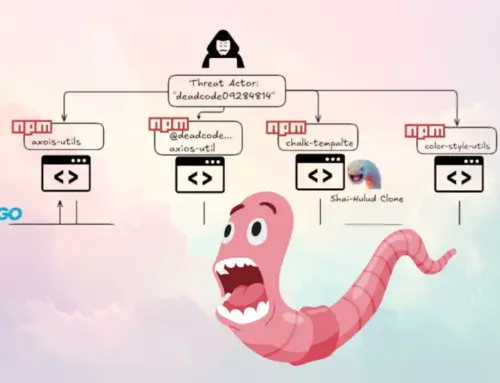
BoryptGrab isn’t your run-of-the-mill malware. Its distribution strategy is particularly insidious, focusing on social engineering and search engine manipulation. Threat actors create a plethora of fake GitHub repositories, meticulously crafted to mimic legitimate, popular free software tools. These repositories are then boosted in search engine rankings, often appearing as top results for common software queries. Users, believing they are downloading a trusted application, fall prey to the deception, inadvertently installing BoryptGrab onto their Windows machines.
Once unleashed, BoryptGrab’s objective is clear: to exfiltrate as much sensitive data as possible. This includes, but is not limited to:
- Browser Data: Stored passwords, cookies, browsing history, and autofill information from popular web browsers.
- Cryptocurrency Wallet Data: Private keys, seed phrases, and other critical credentials from various crypto wallet applications, both desktop and browser-based.
- System Information: Details about the compromised Windows system, potentially aiding further exploitation.
The Anatomy of Deception: Fake GitHub Repositories
The success of the BoryptGrab campaign hinges on its elaborate network of fake GitHub repositories. These repositories are not simply empty shells; they are designed with convincing details to appear authentic. This often includes:
- Fictitious Commit Histories: Fabricated commit logs to simulate active development and a stable codebase.
- Stargazer and Fork Counts: Artificially inflated numbers to project popularity and trustworthiness.
- Descriptive README Files: Well-written documentation mimicking legitimate open-source projects, often containing instructions for installation and usage.
- Misleading Project Names: Using names very similar to well-known software tools to confuse users.
This level of detail makes it incredibly difficult for an average user to discern a fake repository from a genuine one, especially when coupled with effective search engine optimization (SEO) by the attackers.
Beyond the Download: BoryptGrab’s Stealth and Evasion
BoryptGrab is designed to operate discreetly once installed. It employs various techniques to evade detection by antivirus software and forensic analysis. While specific evasion tactics are still under investigation, common methods for stealer malware include:
- Process injection.
- Obfuscated code.
- Dynamic analysis evasion.
- Communication with command and control (C2) servers over encrypted channels.
The malware’s ability to remain undetected for an extended period allows it to continuously harvest data, escalating the potential damage to victims.
Remediation Actions: Protecting Against BoryptGrab
Given the stealthy nature and severe implications of BoryptGrab, proactive and reactive measures are crucial for protection.
- Verify GitHub Repositories: Before downloading any software from GitHub, meticulously verify the repository’s legitimacy. Check for official links from the software vendor’s website, scrutinize commit history for inconsistencies, and be wary of newly created accounts with high activity.
- Source Software from Official Channels: Always download software directly from the official developer’s website or trusted application stores. Avoid third-party download sites or unfamiliar GitHub repositories.
- Employ Robust Endpoint Security: Utilize next-generation antivirus (NGAV) or endpoint detection and response (EDR) solutions that can detect and prevent malware execution, even for unknown threats. Keep these solutions updated.
- Practice Strong Password Hygiene: Implement unique, complex passwords for all online accounts. Consider using a reputable password manager. Enable multi-factor authentication (MFA) everywhere possible, especially for email, financial accounts, and cryptocurrency exchanges.
- Regularly Back Up Data: Maintain regular backups of critical files, including cryptocurrency wallet files, on offline or secure cloud storage.
- Monitor Cryptocurrency Wallets: Regularly monitor your cryptocurrency wallet activity for any unauthorized transactions. Set up transaction alerts where available.
- Educate Users: Conduct cybersecurity awareness training for employees and users, emphasizing the dangers of phishing, social engineering, and the importance of verifying software sources.
Tools for Detection and Mitigation
| Tool Name | Purpose | Link |
|---|---|---|
| Virustotal | Online service for analyzing suspicious files and URLs. | https://www.virustotal.com/ |
| Hybrid Analysis | Free online malware analysis service for in-depth reports. | https://www.hybrid-analysis.com/ |
| YARA Rules | Pattern matching tool for identifying malware families. | https://virustotal.github.io/yara/ |
| OWASP ZAP | Web application security scanner to identify vulnerabilities. | https://www.zaproxy.org/ |
Key Takeaways: Staying Ahead of the Threat
BoryptGrab serves as a stark reminder of the evolving tactics employed by cybercriminals. Its reliance on fake GitHub repositories and search engine manipulation highlights the need for vigilance and critical thinking when sourcing software online. By adhering to best practices in cybersecurity, verifying download sources, and employing robust security tools, individuals and organizations can significantly reduce their risk of falling victim to sophisticated data stealers like BoryptGrab. Staying informed about emerging threats remains paramount in maintaining a secure digital environment.