Signed Malware Masquerading as Teams, Zoom Apps Drops RMM Backdoors
The digital landscape is a constant battleground, and threat actors are perpetually refining their tactics. A recent and particularly insidious phishing campaign has emerged, masquerading as trusted workplace applications like Microsoft Teams, Zoom, and Adobe Acrobat Reader. What elevates this threat above typical phishing attempts is the use of legitimate-looking digital signatures on the malicious files, making detection significantly more challenging for both users and foundational security tools. This sophisticated approach allows attackers to bypass initial defenses and implant dangerous Remote Monitoring and Management (RMM) backdoors, posing a critical risk to enterprise security.
The Deceptive Lure of Signed Malware
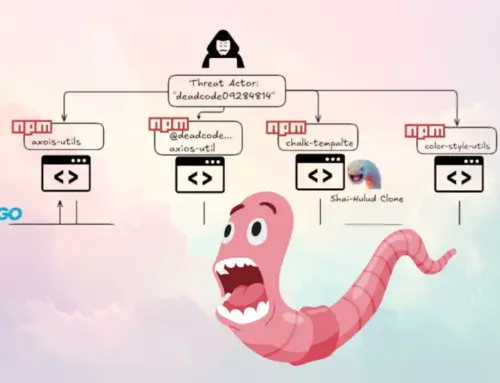
This campaign leverages the inherent trust users place in digitally signed software. Many operating systems and security solutions use digital signatures as a primary indicator of software authenticity and integrity. When a malicious file carries a signature that appears legitimate, it can easily slip past initial scrutiny. Adversaries understand this mechanism and are actively acquiring or compromising certificates to sign their malware, lending an air of legitimacy to their malicious payloads.
The current threat specifically targets enterprise users. By mimicking widely used communication and productivity tools such as Microsoft Teams, Zoom, and Adobe Acrobat Reader, attackers increase the likelihood of successful execution. Users are accustomed to downloading and installing updates or new versions of these applications, making them prime targets for social engineering. A carefully crafted email, appearing to originate from an IT department or a trusted colleague, could easily trick an unsuspecting employee into running the booby-trapped installer.
RMM Backdoors: A Gateway to Network Compromise
The ultimate goal of this signed malware is to deploy Remote Monitoring and Management (RMM) backdoors. RMM tools, legitimate in themselves, are designed for IT administrators to remotely manage and troubleshoot systems. However, in the hands of threat actors, they become powerful instruments for persistent access, data exfiltration, and further network compromise. Once an RMM backdoor is established, attackers can:
- Execute commands remotely on the infected machine.
- Install additional malware or tools.
- Exfiltrate sensitive data.
- Move laterally within the network.
- Establish persistence, even after reboots.
The deployment of RMM backdoors signifies a severe breach, as it grants attackers a stable and often stealthy foothold within the organization’s infrastructure.
The Challenge of Detection
The use of legitimate-looking digital signatures complicates detection for several reasons:
- Reduced User Suspicion: Users are less likely to question the authenticity of a file that appears digitally signed.
- AV Evasion: Traditional antivirus solutions often flag unsigned executables as suspicious. Signed malware can bypass these initial checks, requiring more advanced behavioral analysis.
- Whitelisting Issues: Some security policies might whitelist trusted signers, inadvertently allowing malicious signed software to execute.
Understanding the provenance of the certificate is crucial. While the certificate itself might be valid, it could have been stolen, fraudulently obtained, or belong to a compromised legitimate entity.
Remediation Actions and Proactive Defense
Combating this sophisticated threat requires a multi-layered approach, combining user education with robust technical controls.
For Organizations:
- Enhance Email Security: Implement advanced email filtering solutions that can detect and block phishing attempts, even those with malicious attachments claiming to be popular applications.
- Endpoint Detection and Response (EDR): Deploy EDR solutions that focus on behavioral analysis to identify suspicious activities post-execution, even if the initial file was signed.
- Application Whitelisting with Verification: Implement strict application whitelisting policies. Beyond just checking signatures, verify the integrity and origin of all applications allowed to run.
- Network Segmentation: Limit lateral movement by segmenting your network, making it harder for attackers to spread from an infected workstation.
- Principle of Least Privilege: Ensure users operate with the minimum necessary permissions to perform their job functions.
- Regular Security Awareness Training: Educate employees about the dangers of digitally signed malware, emphasizing the importance of downloading software only from official sources and verifying URLs.
For End Users:
- Verify Download Sources: Always download applications and updates directly from the official vendor websites, never from third-party links in emails or untrusted sources.
- Scrutinize Digital Signatures: While the signature might look legitimate, always check the publisher name. If anything seems off, or if you were not expecting a download, err on the side of caution.
- Report Suspicious Activity: Promptly report any suspicious emails or unexpected software downloads to your IT security team.
Relevant Tools for Detection and Mitigation:
| Tool Name | Purpose | Link |
|---|---|---|
| Endpoint Detection and Response (EDR) Platforms | Advanced threat detection, incident response, and behavioral analysis on endpoints. | Gartner EDR Overview |
| Email Gateway Security | Filtering and blocking malicious emails, protecting against phishing and malware delivery. | Cisco Email Security |
| Application Whitelisting Solutions | Restricting which applications can execute on endpoints based on predefined rules. | TechTarget App Whitelisting |
| Network Intrusion Detection/Prevention Systems (NIDS/NIPS) | Monitoring network traffic for suspicious patterns and known attack signatures. | Cloudflare IDS/IPS |
Conclusion
The emergence of signed malware masquerading as trusted applications represents a significant escalation in the ongoing cat-and-mouse game between threat actors and cybersecurity professionals. The malicious use of digital signatures exploits a fundamental trust mechanism, demanding a shift in defense strategies. Organizations must prioritize advanced detection capabilities, stringent application controls, and continuous security awareness training. By implementing robust technical safeguards and fostering a security-conscious culture, enterprises can significantly mitigate the risk posed by these sophisticated attacks and protect their critical assets from compromise by RMM backdoors.