North Korean IT Worker Unmasked After Refusing to Insult Kim Jong Un in Job Interview
In the high-stakes world of cybersecurity, the game of cat and mouse between nation-state actors and defense teams is constantly evolving. Attack vectors shift, tactics morph, and the methods for identifying adversaries become increasingly sophisticated. However, a recent viral video has unveiled a surprisingly simple, yet profoundly effective, technique for unmasking North Korean state-sponsored IT workers attempting to infiltrate Western organizations. This incident highlights not only the ingenuity required in counter-intelligence but also the unique cultural and political vulnerabilities that can be leveraged.
The footage, widely circulated within cybersecurity and crypto communities, depicts a job interview scenario where a seemingly ordinary question proved to be an insurmountable obstacle for a would-be infiltrator. This discovery serves as a critical reminder of the multi-faceted approach necessary to safeguard digital infrastructure against persistent threats.
The Unmasking Incident: A Bold New Strategy
The core of this compelling story revolves around a job candidate, identified as Taro Aikuchi, who presented himself as a Japanese national. During the interview, Aikuchi was asked to perform an unusual task: to insult North Korea’s Supreme Leader, Kim Jong Un. His refusal to comply with this seemingly innocuous request immediately raised red flags, leading to his unmasking as a North Korean state-sponsored IT worker. This technique exploits the inherent ideological and political indoctrination prevalent in North Korea, where any form of disrespect towards the Supreme Leader is not only unthinkable but potentially punishable by severe consequences for the individual and their family.
This incident, detailed in Cyber Security News, demonstrates a novel approach to vetting individuals from high-risk geopolitical zones. While traditional background checks, technical skill assessments, and behavioral analyses remain crucial, this tactic introduces a psychological and cultural litmus test that few state-sponsored actors would be able to bypass without betraying their true allegiance.
North Korea’s IT Workforce: A Strategic Asset
North Korea’s state-sponsored cyber operations are well-documented, with groups like Lazarus Group (also known as APT38, Guardians of Peace, or Hidden Cobra) implicated in numerous high-profile attacks. These operations often serve a dual purpose: intelligence gathering and illicit fundraising to circumvent international sanctions. To achieve these objectives, North Korea deploys a significant number of highly skilled IT workers abroad, often disguised as freelancers or contractors in countries across Asia, Europe, and North America.
- Economic Sanctions Circumvention: These IT workers are instrumental in generating foreign currency through legitimate-looking IT services, facilitating cryptocurrency theft (e.g., as seen in incidents like the Axie Infinity hack, though a specific CVE is not tied to the worker’s unmasking, these large-scale thefts are indicative of their capabilities), and laundering funds for the regime.
- Espionage and Intelligence Gathering: By embedding themselves within foreign companies, these operatives gain access to sensitive intellectual property, technological advancements, and strategic information.
- Cyber Attack Capabilities: Beyond fundraising, these individuals contribute to the development and deployment of sophisticated malware and attack infrastructures used in state-sponsored cyberattacks.
The pressure on these workers is immense. Failure to adhere to the regime’s strict ideological principles, even in a seemingly private context like a job interview, could have devastating repercussions for them and their families back home.
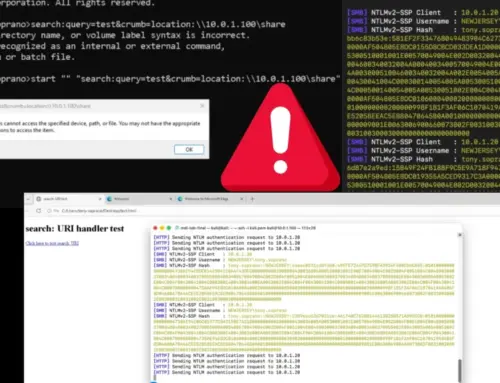
Operational Security (OpSec) Implications for Organizations
This incident underscores the critical need for organizations, particularly those in sensitive sectors (e.g., finance, technology, defense, and cryptocurrency), to enhance their operational security (OpSec) measures. The seemingly low-tech nature of this unmasking technique points to a broader truth: human factors remain a significant vulnerability.
Remediation Actions for Enhanced Insider Threat Detection
To guard against such sophisticated infiltration attempts, organizations should consider a multi-layered approach:
- Enhanced Vetting Processes: Move beyond standard background checks. Implement comprehensive vetting that includes cultural, behavioral, and psychological assessments, especially for roles involving access to sensitive data or systems.
- Behavioral Analysis and Monitoring: Utilize tools and practices to monitor employee behavior for anomalies that might indicate insider threats. This includes unusual network activity, attempts to access unauthorized files, or changes in work patterns.
- Geopolitical Risk Assessment: For remote or outsourced IT talent, understand the geopolitical landscape and potential risks associated with various regions. Evaluate sourcing strategies to mitigate exposure to state-sponsored infiltration attempts.
- Cultural Awareness Training: Equip HR and hiring managers with knowledge about common red flags and cultural nuances that might indicate a hidden agenda, particularly when interviewing candidates from high-risk regions.
- Zero Trust Architecture: Implement a Zero Trust model where no user or device is implicitly trusted, regardless of their location or prior authorization. This minimizes the blast radius of any successful infiltration.
- Regular Security Awareness Training: Educate all employees, not just IT staff, about the evolving nature of cyber threats, including insider threats and social engineering tactics.
The Evolution of Counter-Intelligence in Cybersecurity
The unmasking of Taro Aikuchi marks a significant moment in the ongoing battle against state-sponsored cyber espionage. It demonstrates that sometimes, the most effective defense mechanisms are not necessarily the most technologically advanced. Instead, they leverage a deep understanding of human psychology, geopolitical realities, and cultural frameworks.
As nation-states continue to weaponize their IT talent, organizations must innovate their defense strategies. This means fostering a culture of vigilance, adopting robust security protocols, and developing a nuanced understanding of the adversaries they face. The “Kim Jong Un test” might seem unconventional, but its success highlights the invaluable role of creative thinking in modern cybersecurity operations.
The incident reminds us that effective cybersecurity is a blend of technical prowess, strategic intelligence, and a keen awareness of the human element. Staying ahead requires continuous adaptation, learning from novel incidents, and integrating diverse perspectives into our defense strategies.