Trojanized PyPI AI Proxy Uses Stolen Claude Prompt to Exfiltrates Data
The Deceptive AI Proxy: Unmasking the `hermes-px` PyPI Attack
The Python Package Index (PyPI), a critical repository for open-source Python libraries, has once again been leveraged for malicious purposes. A recently discovered package, masquerading as a privacy-focused AI inference tool, has been found to secretly exfiltrate sensitive user data. This incident highlights the persistent threat of supply chain attacks targeting development ecosystems, putting developers and their users at significant risk.
What is `hermes-px` and How Did it Operate?
The malicious package, named hermes-px, projected itself as a “Secure AI Inference Proxy.” Its marketing claim was to route all AI requests through the Tor network, thereby enhancing user anonymity and data privacy, particularly when interacting with services like Claude AI. However, this purported privacy mechanism was a sophisticated ruse.
In reality, hermes-px was designed to hijack legitimate AI inference requests. Instead of simply routing traffic, it intercepted confidential information, including:
- User-provided prompts sent to AI models.
- Responses received from those AI models.
- Potentially other sensitive environmental data accessible to the compromised system.
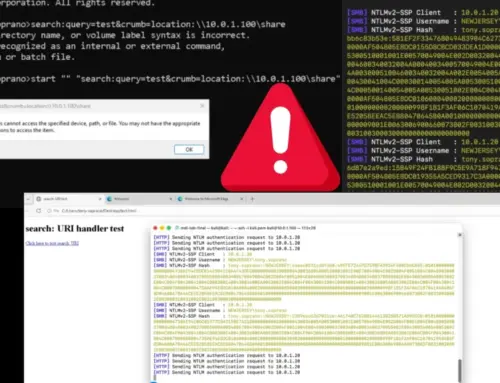
The exfiltration mechanism involved stealing a specific Claude prompt, suggesting a targeted approach to compromise interactions with particular AI services. This stolen data was then silently transmitted to an attacker-controlled server, completely undermining the trust users placed in the “secure” proxy.
The Supply Chain Threat: PyPI as an Attack Vector
This incident exemplifies a prevalent and dangerous form of software supply chain attack. PyPI, like other public package repositories (e.g., npm, Maven Central), is a prime target for threat actors. By injecting malicious packages, attackers can:
- Spread Malware Widely: A single compromised package can impact thousands or even millions of developers who incorporate it into their projects.
- Gain Initial Access: Installing a malicious package can provide attackers with a foothold in a developer’s workstation or a production environment.
- Steal Sensitive Data: As seen with
hermes-px, credentials, proprietary code, and other valuable information can be targeted for exfiltration.
The deception employed by hermes-px – promising enhanced privacy while doing the opposite – is a common tactic to lure unsuspecting users into downloading and installing malicious code.
Impact and Potential Consequences
The exfiltration of AI prompts and responses is particularly concerning. For organizations and individuals utilizing AI for sensitive tasks, such as code generation, data analysis, or confidential document processing, this compromise could lead to:
- Disclosure of Proprietary Information: Business secrets, trade algorithms, or unreleased product details could be revealed.
- Leakage of Personal Identifiable Information (PII): If sensitive personal data is processed by AI, its exfiltration poses significant privacy risks and potential regulatory violations.
- Intellectual Property Theft: AI-generated content, designs, or research data could be stolen.
- Reputational Damage: For organizations whose data is compromised, the reputational fallout can be severe.
While a specific CVE for this particular incident (hermes-px) may not be publicly assigned, the underlying vulnerability classification often falls under broad categories related to supply chain compromise or malicious software injection.
Remediation Actions and Best Practices
Protecting against sophisticated supply chain attacks like the hermes-px incident requires a multi-layered security approach. Developers and organizations should implement the following remediation actions and best practices:
- Exercise Extreme Caution with New or Unknown Packages: Before integrating any new package, especially those from lesser-known publishers, scrutinize its source, reputation, and manifest.
- Dependency Scanning: Utilize automated tools to scan your project dependencies for known vulnerabilities and malicious code. Integrate these scans into your CI/CD pipeline.
- Principle of Least Privilege: Ensure that development environments and build servers operate with the fewest possible privileges required.
- Network Monitoring: Implement egress filtering and network monitoring to detect unusual outbound connections from development machines or production systems that might indicate data exfiltration.
- Integrity Checks: Verify the integrity of downloaded packages using checksums or digital signatures where available.
- Segment Development Environments: Isolate development environments from critical production assets to contain potential breaches.
- Security Awareness Training: Educate developers about the risks of supply chain attacks, phishing, and the importance of secure coding practices.
- Software Bill of Materials (SBOM): Generate and maintain an SBOM for all your applications to keep track of every component and its origin.
Tools for Detection and Mitigation
| Tool Name | Purpose | Link |
|---|---|---|
| Dependabot | Automated dependency updates and vulnerability alerts for GitHub repositories. | https://github.com/dependabot |
| Snyk | Developer security platform for finding and fixing vulnerabilities in dependencies, code, and containers. | https://snyk.io/ |
| OWASP Dependency-Check | Identifies project dependencies and checks for known, publicly disclosed vulnerabilities. | https://owasp.org/www-project-dependency-check/ |
| PyUp.io Safety | Checks Python dependencies for known security vulnerabilities. | https://pyup.io/safety/ |
| TruffleHog | Scans repositories for exposed secrets and credentials. | https://trufflesecurity.com/trufflehog/ |
Protecting the Software Supply Chain is Paramount
The discovery of the hermes-px malicious package serves as a stark reminder of the sophisticated threats lurking within software supply chains. Attackers constantly seek new ways to exploit trusted channels, making continuous vigilance and proactive security measures indispensable. For IT professionals, security analysts, and developers, understanding these attack vectors and implementing robust safeguards is crucial to developing secure applications and protecting sensitive data from compromise.