Flowise AI Agent Builder Injection Vulnerability Exploited in Attacks, 15,000+ Instances Exposed
The landscape of artificial intelligence is rapidly evolving, with platforms like Flowise empowering developers to build sophisticated AI agents and custom large language model (LLM) workflows. However, this innovation comes with inherent security challenges. Urgent reports indicate that a critical vulnerability in Flowise, an open-source AI agent builder, is being actively exploited in the wild, exposing over 15,000 instances to potential compromise.
The Critical Flowise RCE Vulnerability Explained
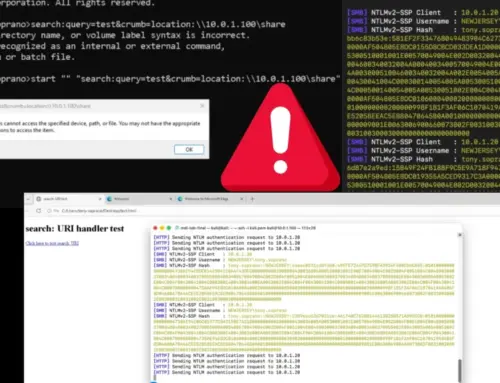
Threat actors are leveraging a maximum-severity remote code execution (RCE) vulnerability within Flowise. This critical flaw, officially tracked as CVE-2025-59528, boasts a CVSS score of 10.0 – the highest possible rating, signifying extreme danger. The vulnerability allows attackers to inject and execute arbitrary JavaScript code on vulnerable Flowise installations.
Successful exploitation grants attackers extensive control. This includes, but is not limited to, the ability to:
- Execute arbitrary commands on the underlying server.
- Access sensitive data stored on the system.
- Establish persistent backdoors.
- Manipulate AI workflows and models.
The broad impact of this RCE vulnerability means that any organization or individual running unpatched Flowise instances is at severe risk of a full system compromise. The ease of exploitation combined with the widespread deployment of Flowise makes this a high-priority threat.
Understanding the Attack Vector and Impact
The core of the vulnerability lies in an injection flaw that bypasses security controls, allowing malicious code to be executed within the Flowise environment. This type of vulnerability typically arises from insufficient input validation and sanitization, where user-supplied data is not properly vetted before being processed or executed by the system.
With more than 15,000 Flowise instances exposed, the potential for widespread damage is significant. Organizations leveraging Flowise for critical business operations, data processing, or client-facing applications face the risk of not only data breaches but also operational disruption and reputational harm. The compromise of an AI agent builder can also lead to the manipulation of the AI models themselves, potentially introducing biases, backdoors, or malicious functionalities into deployed AI systems.
Remediation Actions for Flowise Users
Immediate action is imperative for all users and administrators of Flowise instances. Given the active exploitation, delaying remediation could lead to severe consequences:
- Patch Immediately: The most critical step is to apply available security patches from the official Flowise project. Monitor their GitHub repository and official communication channels for updates addressing CVE-2025-59528. Update to the latest stable version as soon as a fix is released.
- Isolate Flowise Instances: If immediate patching is not possible, isolate your Flowise deployments from external networks as much as possible. Restrict network access only to necessary internal systems and trusted IP addresses.
- Implement Least Privilege: Ensure that the Flowise application and its underlying processes run with the absolute minimum necessary permissions. This can help limit the extent of compromise even if an RCE is exploited.
- Regular Backups: Maintain regular, secure backups of your Flowise data and configurations. In the event of a compromise, this can aid in recovery and minimize data loss.
- Monitor Logs: Enhance logging and actively monitor Flowise system logs for any anomalous activity, such as unusual process execution, unexpected network connections, or unauthorized file modifications.
- Security Audits: Conduct regular security audits and penetration testing on your Flowise deployments to identify and address potential vulnerabilities proactively.
Tools for Detection and Mitigation
Employing specific tools can aid in the detection and mitigation of this and similar vulnerabilities. While Flowise-specific exploits might require targeted patches, general security tools are crucial for overall posture.
| Tool Name | Purpose | Link |
|---|---|---|
| OWASP ZAP | Web application security scanner to identify injection flaws and other vulnerabilities. | https://www.zaproxy.org/ |
| Nessus | Vulnerability scanner that can detect unpatched software and configuration weaknesses. | https://www.tenable.com/products/nessus |
| ClamAV | Open-source antivirus engine for detecting malicious files and payloads. | https://www.clamav.net/ |
| Snort/Suricata | Network intrusion detection/prevention systems (NIDS/NIPS) for monitoring suspicious network traffic. | https://www.snort.org/ https://suricata-ids.org/ |
Conclusion
The active exploitation of CVE-2025-59528 in Flowise AI agent builder instances underscores the critical importance of robust security practices in the rapidly evolving AI landscape. Organizations and developers leveraging Flowise must prioritize immediate patching and implement comprehensive security measures to protect their systems. The high CVSS score and observed in-the-wild attacks confirm that this is not a threat to be underestimated. Vigilance, rapid response, and proactive security hygiene are essential to safeguard AI infrastructure from sophisticated cyber threats.