Amazon S3 Files, Turns S3 Buckets as File System to Access Your Data
Unveiling Amazon S3 Files: Transforming Cloud Storage into a Seamless File System
Cloud storage has fundamentally reshaped how organizations manage and access their vast datasets. Amazon S3 (Simple Storage Service) has long been a cornerstone of this transformation, providing scalable and durable object storage. However, accessing this data traditionally involved application-specific integrations or complex data movement. That landscape is changing with a significant update: the introduction of Amazon S3 Files. This new capability allows S3 buckets to function as fully-fledged, accessible file systems, profoundly impacting data workflows and potentially minimizing security complexities associated with data egress.
The Evolution of S3 Data Access: From Objects to File Systems
Historically, Amazon S3 has been an object storage solution. Developers and applications interacted with S3 data as discrete objects, each with
its own metadata. While incredibly powerful for data lakes, backups, and archiving, this object-oriented approach presented challenges for workloads that inherently rely on traditional file system paradigms. Analytics platforms, high-performance computing (HPC) applications, and content management systems often expect data to reside on a hierarchical, shared file system that supports standard file operations like opening, reading, writing, and closing files, along with directory structures.
The innovation of Amazon S3 Files directly addresses this gap. By turning S3 buckets into accessible file systems, AWS eliminates the need for expensive and time-consuming data replication or complex translation layers. This update dramatically simplifies how organizations can leverage their existing Amazon S3 storage for diverse computational needs without altering their core data storage strategy.
Key Benefits and Implications for Data Management
The ability to mount S3 buckets as a file system offers several compelling advantages:
- Simplified Data Access: Applications can now interact directly with S3 data using standard file system interfaces (e.g., POSIX commands), reducing development overhead and integration complexity.
- Elimination of Data Movement: Organizations no longer need to copy or move large datasets from S3 to other file-based storage solutions to perform analytics or processing. This not only saves time but also significantly reduces egress costs and data transfer bottlenecks.
- Enhanced Workflow Efficiency: Workflows that previously required data ingestion into dedicated file systems can now operate directly on S3, streamlining processes for machine learning, big data analytics, and media processing.
- Cost Optimization: By leveraging S3’s cost-effectiveness for primary storage and direct file system access, organizations can potentially reduce their overall storage and data processing infrastructure costs.
- Scalability and Durability: Users inherit S3’s renowned scalability, durability, and availability, even when interacting with it as a file system.
Security Considerations and Best Practices for S3 File Systems
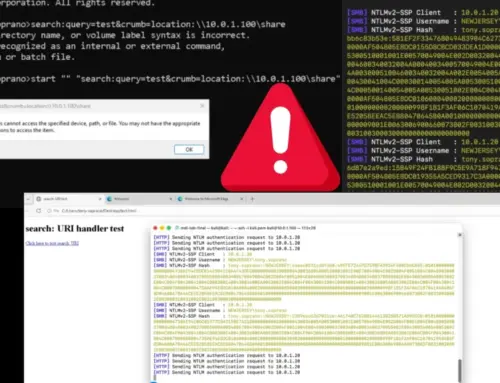
While Amazon S3 Files introduces immense convenience, it’s crucial to approach its implementation with robust security practices. The shift from object access to file system access, while beneficial, changes the interaction model and requires careful consideration of permissions and data governance.
Remediation Actions:
- Least Privilege Access: Continue to enforce the principle of least privilege. Ensure that IAM policies granting file system access to S3 buckets are as granular as possible, permitting only the necessary read, write, or execute permissions for specific users or applications. Avoid overly permissive wildcard policies.
- Bucket Policy Review: Regularly review and audit S3 bucket policies. With file system access, a misconfigured bucket policy could inadvertently expose sensitive data to unauthorized entities. Pay close attention to public access settings.
- Encryption at Rest and In Transit: Mandate encryption for all data both at rest and in transit. S3 supports server-side encryption (SSE-S3, SSE-KMS, SSE-C) and client-side encryption. Utilize TLS/SSL for all data transfers to and from the S3 file system.
- Logging and Monitoring: Enable S3 access logging and integrate with AWS CloudTrail and Amazon CloudWatch. Monitor access patterns, failed access attempts, and changes to S3 bucket configurations. Alerts should be configured for suspicious activities, such as unusual download volumes or unauthorized modifications.
- Vulnerability Management: While S3 itself is a managed service, the applications interacting with it via the file system interface might introduce vulnerabilities. Ensure that any client-side applications accessing S3 as a file system are regularly patched and subject to vulnerability scanning. There are no known direct CVEs associated with the S3 Files feature itself immediately upon its release, but the interconnected systems always represent a potential attack surface. For general S3 misconfiguration vulnerabilities, security analysts often look at configurations that lead to public exposure, for which there aren’t specific CVEs but rather general best practices to avoid.
- Network Access Controls: Implement strong network access controls, such as VPC endpoints and security groups, to limit which IP addresses or AWS resources can mount and interact with your S3 file systems.
- Data Lifecycle Management: Utilize S3 lifecycle policies to manage data retention, archiving, and deletion, ensuring that sensitive data is not retained longer than necessary.
The Future of Cloud Data Processing and Analytics
Amazon S3 Files marks a pivotal moment in cloud storage. By bridging the gap between object storage and traditional file systems, AWS empowers organizations to unlock new efficiencies, reduce operational complexities, and innovate faster. This capability is particularly impactful for industries heavily reliant on large-scale data processing, such as scientific research, media and entertainment, and financial services. As enterprises continue to migrate and generate ever-increasing volumes of data in the cloud, solutions that offer both flexibility and robust security will be paramount.