New Fake CAPTCHA Campaign Uses SMS Pumping Fraud to Run Up Victims’ Phone Bills
Imagine navigating the web, minding your own business, when suddenly a routine CAPTCHA request pops up. You complete it, prove you’re not a robot, and move on. What you don’t realize is that behind that seemingly harmless interaction, a malicious campaign is silently draining your mobile phone balance. This isn’t a hypothetical scenario; a new and insidious scam is actively leveraging fake CAPTCHA pages to trigger international SMS message ‘pumping,’ leaving victims with unexpected, costly phone bills.
The Lurking Threat of SMS Pumping Fraud
SMS pumping fraud, also known as SMS toll fraud or artificially inflated traffic (AIT), is a sophisticated scheme where threat actors exploit vulnerabilities in telecommunications systems. Traditionally, this involves generating large volumes of SMS traffic to premium-rate numbers controlled by the fraudsters, who then receive a share of the revenue from the network provider. This new CAPTCHA campaign adds an alarming layer of deception, tricking unsuspecting users into initiating the fraudulent activity themselves.
The core mechanism is chillingly simple yet effective: what appears to be a standard “prove you’re human” challenge is, in reality, a meticulously crafted phishing page. When a user interacts with this fake CAPTCHA, it doesn’t verify their humanity; instead, it surreptitiously triggers dozens of premium international SMS messages from their device. These messages are directed to specific numbers controlled by the attackers, designed to rack up charges on the victim’s phone bill.
Anatomy of the Fake CAPTCHA Attack
The campaign operates under a veil of normalcy, making it incredibly difficult for users to identify the fraud in progress. The fake CAPTCHA pages are often embedded within legitimate-looking websites or appear as redirects, enhancing their credibility. Users are prompted to perform tasks commonly associated with CAPTCHAs, such as selecting images or typing distorted text. However, the backend execution is where the malicious intent lies.
- Deceptive Presentation: The fake CAPTCHAs mimic popular and widely recognized CAPTCHA services, increasing the likelihood of user compliance.
- Silent Execution: The SMS messages are triggered without any visible indication on the victim’s phone, no outgoing message alerts, and no prompts for confirmation.
- Financial Impact: The charges from these unsolicited international SMS messages can accumulate rapidly, leading to significantly inflated phone bills that catch victims completely off guard.
This tactic is a clear evolution of SMS pumping, leveraging social engineering at the user interaction point to bypass more direct methods of generating traffic. The victim unwittingly becomes an accomplice, albeit an unknowing one, in their own financial detriment.
What is SMS Pumping and Why is it Dangerous?
SMS pumping is a form of telecom fraud where criminals inflate the volume of SMS messages sent to specific phone numbers, often premium-rate numbers, to generate illicit revenue. Carriers pay out termination fees for delivering these messages, which are then shared with the “owner” of the premium number. In the context of this fake CAPTCHA campaign, the danger lies in the silent nature of the attack and the global reach of potential victims. The charges are often difficult to dispute, as the messages technically originated from the victim’s device.
The danger extends beyond monetary loss. Such campaigns can also be used as a smokescreen for other malicious activities, or to harvest phone numbers for future phishing or spam campaigns. The trust in essential web security mechanisms like CAPTCHAs is undermined, making users more wary of legitimate challenges.
Remediation Actions and Prevention
Protecting yourself and your organization from this evolving threat requires a multi-layered approach, combining user awareness with technical safeguards.
- Educate Users: Train employees and raise public awareness about the existence of such fake CAPTCHA scams. Emphasize vigilance when encountering unexpected CAPTCHA requests, especially on unfamiliar sites.
- Monitor Phone Bills: Regularly review mobile phone bills for unusual international SMS charges or spikes in messaging activity. Many carriers offer detailed usage reports.
- Carrier Restrictions: Contact your mobile carrier to inquire about options to block international SMS messages or restrict premium-rate SMS services. Some carriers allow setting spending limits for certain types of services.
- Browser Extensions: Consider using reputable browser extensions that help identify potentially malicious websites or warn about suspicious redirects.
- Network Monitoring: For organizations, implement network monitoring solutions that can detect unusual outbound traffic patterns, although directly identifying SMS pumping from network traffic can be challenging due to its nature.
- Security Software: Ensure all devices are protected with up-to-date antivirus and anti-malware software that can detect phishing attempts and malicious scripts.
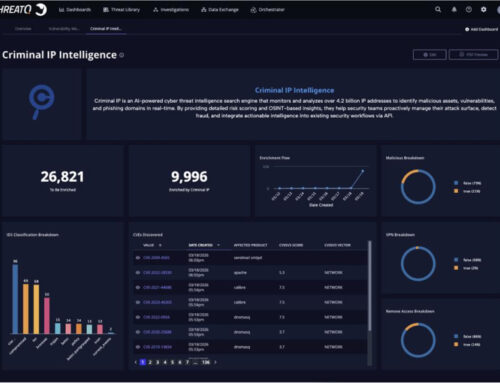
Tools for Detection and Mitigation
While direct tools for detecting in-progress SMS pumping initiated by a fake CAPTCHA on a user’s device are limited, several broader cybersecurity tools can help in prevention and post-incident analysis.
| Tool Name | Purpose | Link |
|---|---|---|
| PhishTank | Community-based phishing URL verification and sharing. | https://www.phishtank.com/ |
| URLVoid | Website reputation checker, identifies blacklists and suspicious activities. | https://www.urlvoid.com/ |
| Google Safe Browsing | API for checking URLs against Google’s list of unsafe web resources. | https://developers.google.com/safe-browsing |
| Mobile Security Suites | Antivirus and anti-malware for mobile devices, protecting against malicious apps. | (Varies by vendor, e.g., Bitdefender, Norton, Lookout) |
| Carrier Billing Management Tools | Provided by mobile operators for managing international calls/SMS and premium services. | (Varies by carrier) |
Unfortunately, there isn’t a specific CVE assigned to general SMS pumping fraud or fake CAPTCHA campaigns, as these are types of social engineering and fraud rather than software vulnerabilities with a patchable source. However, related vulnerabilities in authentication mechanisms or web platforms could contribute indirectly. For instance, any vulnerabilities enabling easier website defacement or iframe injection could facilitate the deployment of these fake CAPTCHAs.
Conclusion
The emergence of fake CAPTCHA pages for SMS pumping fraud represents a cunning evolution in cybercrime. It manipulates a common web security measure into a tool for financial exploitation. As this campaign highlights, vigilance and a proactive approach to digital hygiene are paramount. By understanding the mechanics of these attacks, staying informed, and employing appropriate security measures, individuals and organizations can significantly reduce their exposure to such surreptitious financial threats.