Criminal IP and Securonix ThreatQ Collaborate to Enhance Threat Intelligence Operations
Strengthening Cyber Defenses: Criminal IP and Securonix ThreatQ Unite for Advanced Threat Intelligence
The relentless pace of cyberattacks demands that security operations continuously evolve. Organizations face an uphill battle against sophisticated threats, often struggling with fragmented intelligence and slow response times. Effective threat intelligence is no longer a luxury; it’s a critical component of a robust security posture. This is precisely why the recent collaboration between Criminal IP and Securonix ThreatQ marks a significant step forward in enhancing threat intelligence operations for security teams worldwide.
The Power of Integrated Threat Intelligence: Criminal IP Joins ThreatQ
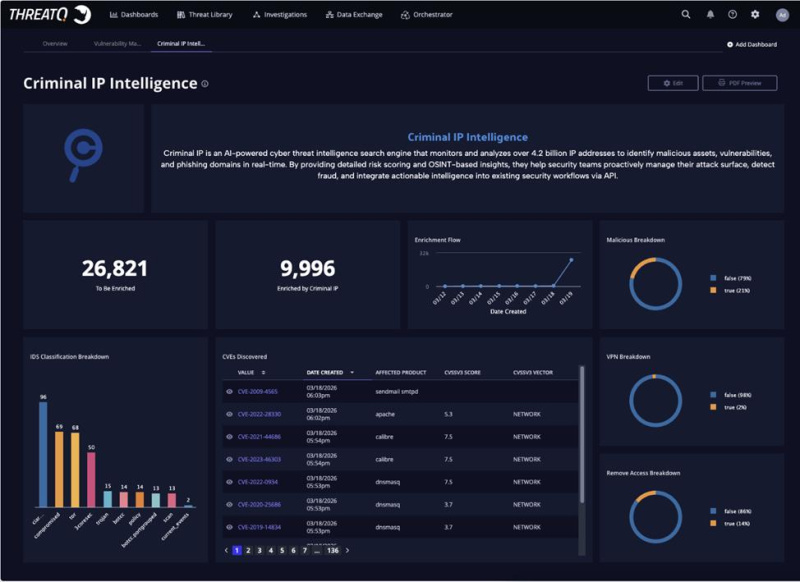
Security teams often grapple with a deluge of data, making it challenging to identify truly malicious activities from the noise. The integration of Criminal IP’s advanced threat intelligence into Securonix ThreatQ directly addresses this challenge. This partnership empowers organizations to seamlessly incorporate vital external IP intelligence into their existing security workflows. The benefit? Security analysts gain access to more actionable context, enabling them to accelerate analysis and streamline their incident response efforts.
Beyond Traditional Feeds: Criminal IP’s Unique Edge
What differentiates Criminal IP from conventional threat intelligence feeds is its depth of visibility. While many feeds offer basic indicators of compromise (IoCs), Criminal IP delves deeper, providing comprehensive insights into how assets are being exploited and leveraged by attackers. This granular understanding is crucial for a proactive defense strategy. For instance, understanding the attack infrastructure associated with a specific IP address can help identify other potential targets or related campaigns, turning reactive responses into strategic anticipations.
Why Context Matters: Accelerating Analysis and Response
In the fast-paced world of cybersecurity, every second counts. A security analyst trying to determine the criticality of an alert without sufficient context is at a severe disadvantage. The combined capabilities of Criminal IP and ThreatQ provide this essential context. By enriching internal security data with external IP intelligence, teams can quickly answer critical questions such as:
- Is this IP address associated with known malicious campaigns?
- What specific vulnerabilities (e.g., CVE-2023-XXXX or CVE-2024-XXXX) are commonly exploited by threats originating from this IP?
- What is the geographic location and historical activity of this IP?
- Has this IP been linked to phishing, malware distribution, or command-and-control (C2) infrastructure?
This comprehensive view allows for more informed decision-making, reducing dwell time and minimizing the potential impact of attacks.
Operationalizing Threat Intelligence for Enhanced Security Operations
The true value of threat intelligence lies in its operationalization. It’s not enough to simply collect data; it must be integrated into daily security operations to provide tangible benefits. The partnership between Criminal IP and Securonix facilitates this by:
- Automating Enrichment: Automatically enriching alerts and incidents with relevant Criminal IP data as they arise within ThreatQ.
- Prioritizing Threats: Enabling security teams to better prioritize threats based on the risk associated with IP addresses.
- Improving Investigation: Providing analysts with a single pane of glass for internal telemetry and external threat context, streamlining investigations.
- Proactive Defense: Identifying potential threats before they fully materialize by monitoring suspicious IP activities.
Looking Ahead: A Stronger Defensive Stance
The collaboration between Criminal IP and Securonix ThreatQ, announced on May 1st, 2026, marks a significant milestone in advancing cyber defense capabilities. By bringing together Criminal IP’s deep IP intelligence with ThreatQ’s robust threat intelligence platform, organizations are better equipped to understand, detect, and respond to the evolving threat landscape. This synergy allows security professionals to move beyond basic threat feeds, gaining invaluable insights that transform reactive incident response into a more strategic and proactive security posture.





