Ransomware Victims Jump to 7,831 as AI Crime Tools Scale Global Attacks
Ransomware’s Escalation: AI-Driven Attacks Fuel a 389% Surge in Victims
The digital landscape is under siege. Recent findings from Fortinet’s 2026 Global Threat Landscape Report reveal a stark reality: ransomware attacks have not merely increased, they have exploded. The number of confirmed ransomware victims worldwide surged to a staggering 7,831 in 2025, a dramatic leap from approximately 1,600 victims recorded just the year prior. This represents a chilling 389% year-over-year increase, underscoring the profound impact of evolving cyber threats, particularly the insidious role of AI-powered crime tools.
The Alarming Rise: A Deep Dive into the Numbers
This unprecedented jump in ransomware victim counts is a critical indicator of the expanding threat surface. The 389% increase is not merely a statistic; it signifies thousands of businesses, organizations, and individuals grappling with data encryption, operational disruption, and the agonizing decision of whether to pay a ransom. This escalation points to a confluence of factors, including more sophisticated attack methodologies, a wider array of targets, and perhaps most crucially, the leveraging of advanced technologies by threat actors.
AI Crime Tools: The Force Multiplier Behind Global Attacks
The report highlights
the critical role of artificial intelligence in scaling these global attacks. AI’s capabilities, once largely aspirational for cybercriminals, are now being weaponized to amplify the effectiveness and reach of ransomware campaigns. This includes:
- Automated Attack Vector Identification: AI algorithms can rapidly scan vast networks for vulnerabilities, accelerating the initial compromise phase.
- Enhanced Social Engineering: AI-powered tools can generate highly convincing phishing emails and spear-phishing attempts, tailored to individual targets based on publicly available information, making them significantly harder to detect.
- Adaptive Malware: Next-generation ransomware variants are utilizing AI to learn and adapt to defensive measures, making containment and eradication more challenging.
- Infrastructure Automation: The deployment and management of complex attack infrastructures, including command-and-control servers, can be automated by AI, allowing threat actors to manage simultaneous campaigns with greater efficiency.
Common Attack Vectors and Vulnerabilities Exploited
Ransomware groups leverage a variety of well-known and emerging attack vectors to gain initial access and propagate their malicious payloads. While specific CVEs vary by campaign, common themes include:
- Exploitation of Public-Facing Applications: Vulnerabilities in web servers, VPNs, and other internet-facing services are prime targets. For instance, exploits against unpatched Citrix NetScaler Application Delivery Controller (ADC) and NetScaler Gateway vulnerabilities like CVE-2023-4966 (CitrixBleed) have been widely used for initial access.
- Software Vulnerabilities: Flaws in popular software, operating systems, and third-party components remain a consistent entry point. Examples include critical vulnerabilities in Microsoft Exchange like CVE-2021-26855 (ProxyLogon).
- Phishing and Social Engineering: Despite technical advancements, human error remains a significant vulnerability, often exploited through sophisticated phishing campaigns or malware delivered via malicious attachments or links.
- Remote Desktop Protocol (RDP) Exploitation: Weak or unprotected RDP credentials continue to be a favored method for initial compromise and lateral movement within networks.
Remediation Actions and Proactive Defense Strategies
Organizations must adopt a multi-layered and proactive cybersecurity posture to
mitigate the escalating ransomware threat. The following actions are critical:
- Patch Management: Implement a robust and timely patch management program for all operating systems, applications, and network devices. Prioritize critical vulnerabilities, especially those with known exploits.
- Strong Authentication: Enforce multi-factor authentication (MFA) for all services, particularly for remote access, privileged accounts, and cloud services.
- Regular Backups & Recovery Plans: Maintain offsite, immutable backups of all critical data. Regularly test backup restoration processes to ensure data recoverability in the event of an attack.
- Network Segmentation: Segment networks to limit lateral movement of attackers. Isolate critical systems and sensitive data from less secure areas.
- Endpoint Detection and Response (EDR): Deploy EDR solutions to provide advanced threat detection, behavior analysis, and automated response capabilities on endpoints.
- Employee Training: Conduct regular cybersecurity awareness training for all employees, focusing on recognizing phishing attempts, social engineering tactics, and the importance of strong password hygiene.
- Incident Response Plan: Develop and regularly test a comprehensive incident response plan specifically for ransomware attacks, including communication protocols, containment strategies, and recovery procedures.
- Threat Intelligence Integration: Utilize threat intelligence feeds to stay informed about emerging ransomware variants, attack techniques, and indicators of compromise (IoCs).
- Application Whitelisting: Implement application whitelisting to prevent unauthorized software from executing on critical systems.
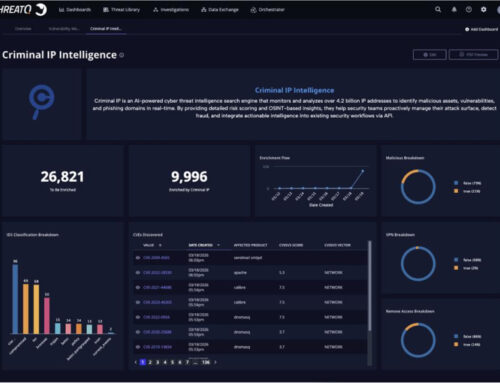
Tools for Detection and Mitigation
| Tool Name | Purpose | Link |
|---|---|---|
| FortiEDR | Endpoint Detection & Response, behavioral analysis against ransomware | https://www.fortinet.com/products/endpoint-security/fortiedr |
| Varonis Data Security Platform | Data visibility, threat detection, and data protection for on-prem & cloud | https://www.varonis.com/products/data-security-platform |
| Cofense PhishMe | Phishing simulation and security awareness training | https://cofense.com/product-services/phishme/ |
| Nessus Professional | Vulnerability scanning and assessment | https://www.tenable.com/products/nessus/nessus-professional |
| CrowdStrike Falcon Insight | Cloud-native EDR and Extended Detection and Response (XDR) | https://www.crowdstrike.com/products/endpoint-security/falcon-insight-xdr/ |
The Path Forward: Adapting to the AI-Enhanced Threat
The dramatic increase in ransomware victims, driven largely by AI-powered crime tools, signals a fundamental shift in the cybersecurity landscape. Organizations must recognize that traditional defense mechanisms are no longer sufficient. A proactive, adaptive, and intelligence-driven security strategy is paramount. Embracing advanced security technologies, fostering a strong security culture, and maintaining robust incident response capabilities are not just best practices, but essential components for resilience against the evolving and increasingly intelligent adversary.