New Spyware Platform Lets Buyers Rebrand and Resell Android Surveillance Malware
The Resale Epidemic: When Android Spyware Becomes a Brandable Commodity
The digital defense perimeter constantly faces new and evolving threats. While individual malware strains are a persistent concern, a far more insidious development has emerged: the commercialization and rebranding of sophisticated surveillance tools. A new Android spyware platform is enabling threat actors, or even less scrupulous individuals, to purchase, rebrand, and resell powerful monitoring software with alarming ease. This trend accelerates the democratization of digital surveillance, making advanced spyware accessible to a wider, and potentially less scrupulous, audience.
The Business Model of Digital Espionage
Unlike traditional, one-off malware campaigns, this new platform offers a complete white-label solution. For a fee, purchasers gain access to the core Android spyware capabilities and, crucially, the ability to customize its appearance. This customization includes rebranding with their own names and logos, effectively allowing them to market and distribute the surveillance tool as their “own product.” This business model lowers the barrier to entry for aspiring cybercriminals or private investigators seeking illicit methods, transforming complex technical operations into a simple retail transaction.
Beyond Basic Surveillance: The Rebranding Threat
The danger here extends beyond the inherent surveillance capabilities of the spyware itself. While the act of monitoring an Android device is a significant breach of privacy, the rebranding feature adds several critical layers of concern:
- Increased Obfuscation: Rebranded spyware is harder to attribute to its original developers, making investigations into its source more challenging.
- Wider Distribution: The ease of rebranding encourages a greater number of individuals and groups to enter the spyware market, leading to a proliferation of these tools.
- Legitimacy Facade: A custom brand and logo can lend an air of legitimacy to an illicit tool, potentially deceiving unsuspecting users into installing or trusting it.
- Reduced Technical Skill Barrier: Buyers no longer need advanced coding or malware development skills; they simply need to be able to market a product.
Technical Insights into the Android Spyware Platform
While specific technical details of this new platform are still emerging, similar Android spyware often leverages common attack vectors and functionalities:
- Social Engineering: Distribution frequently relies on convincing users to install the application willingly, often disguised as legitimate apps, social media updates, or system utilities.
- Permission Abuse: Once installed, the spyware typically requests extensive permissions, including access to contacts, call logs, SMS messages, GPS location, microphone, and camera.
- Persistence Mechanisms: Spyware often employs techniques to ensure it remains active on the device, even after reboots, by embedding itself deeply within the operating system or leveraging legitimate background processes.
- Data Exfiltration: Collected data isusually exfiltrated to a command-and-control (C2) server, often encrypted, to avoid detection.
While no specific CVE has been assigned to this particular platform, the underlying vulnerabilities that enable such broad permission abuse and persistence are often linked to weak application sandboxing or user permission models. For instance, vulnerabilities like those found in Android’s permission handling (e.g., related to CVE-2023-28537, though not directly applicable to this specific spyware, illustrates general permission bypasses) or shortcomings in app store vetting processes contribute to the environment where such spyware thrives. For more information on CVE-2023-28537, refer to the official CVE database.
Remediation Actions for Android Users and Organizations
Protecting against rebranded Android spyware requires a layered approach, encompassing user education, vigilant security practices, and robust organizational policies.
- For Individual Users:
- Be Wary of Unsolicited Downloads: Never install applications from untrusted sources or links received via SMS, email, or unverified social media posts.
- Scrutinize App Permissions: Before installing any app, carefully review the permissions it requests. If an app’s permissions seem excessive for its stated functionality (e.g., a flashlight app requesting access to your microphone and contacts), do not install it.
- Keep Your OS Updated: Regularly update your Android operating system to patch known vulnerabilities that spyware might exploit.
- Use Reputable Antivirus/Anti-Malware: Install a reputable mobile security solution on your device and keep it updated.
- Regularly Review Installed Apps: Periodically check your device’s installed applications and remove any that you don’t recognize or no longer use.
- Enable Google Play Protect: Ensure Google Play Protect is enabled on your device, as it scans apps for malicious behavior.
- For Organizations:
- Implement Mobile Device Management (MDM): Utilize MDM solutions to enforce security policies, manage app installations, and monitor device health across corporate-issued and BYOD devices.
- Provide Security Awareness Training: Educate employees on phishing, social engineering tactics, and the dangers of installing unauthorized applications.
- Prohibit Sideloading: Enforce policies that prohibit employees from sideloading applications from third-party app stores or unknown sources.
- Regular Security Audits: Conduct regular security audits of mobile devices used for business purposes.
- Network-Level Filtering: Implement network-level filtering to block known command-and-control server IPs associated with spyware.
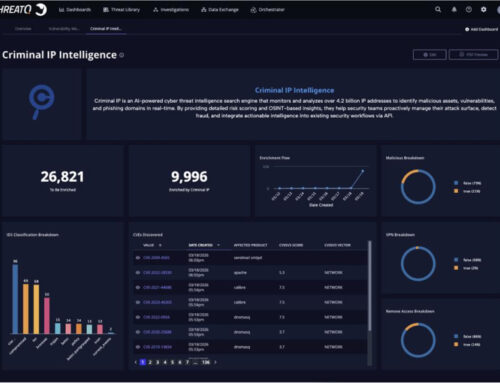
Essential Tools for Detection and Mitigation
Leveraging the right tools is crucial for identifying and neutralizing Android spyware. While no tool is foolproof, a combination of these can significantly enhance your defensive posture.
| Tool Name | Purpose | Link |
|---|---|---|
| Google Play Protect | Built-in Android security scanner for malicious apps. | N/A (Integrated with Google Play Services) |
| Malwarebytes Security | Comprehensive mobile antivirus and anti-malware scanning. | https://www.malwarebytes.com/mobile |
| Bitdefender Mobile Security | Advanced mobile security with anti-theft, privacy, and VPN features. | https://www.bitdefender.com/solutions/mobile-security-android.html |
| Any.Run | Interactive online malware analysis sandbox (for analyzing suspicious app APKs). | https://any.run/ |
| App Census (for developers/analysts) | Tool for analyzing app permissions and tracking behaviors. | https://appcensus.mobi/ |
The Pervasive Threat of Rebrandable Spyware
The advent of a rebrandable Android spyware platform signals a new phase in the arms race between cyber defenders and malicious actors. This development lowers the technical and financial hurdles for deploying sophisticated surveillance tools, making them accessible to a broader array of individuals and groups outside traditional state-sponsored entities. The implications are significant for individual privacy and organizational security. Vigilance, education, and proactive security measures are paramount to countering this pervasive and evolving threat.