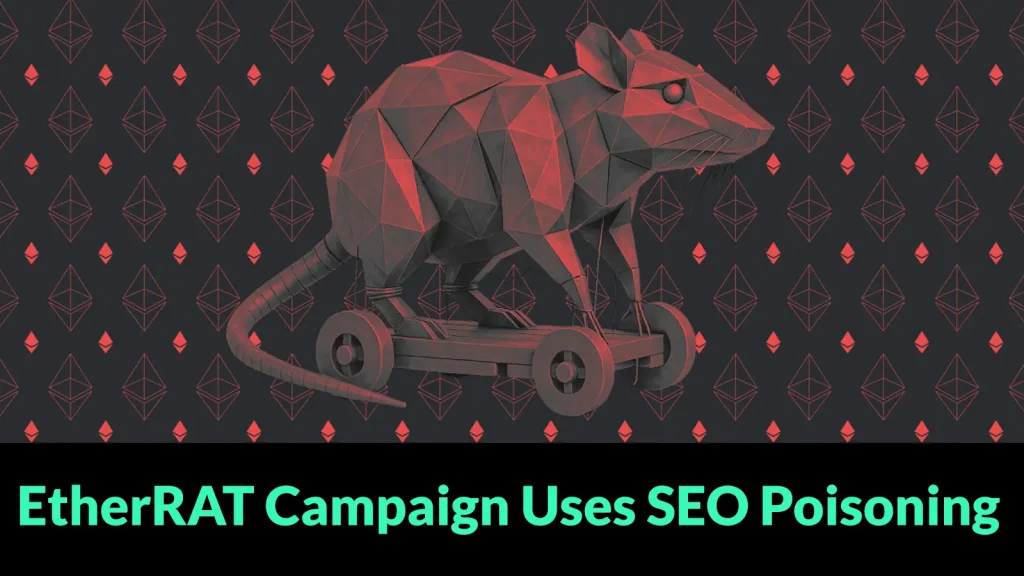
EtherRAT Campaign Uses SEO Poisoning and GitHub Facades to Target Enterprise Admins
Unmasking EtherRAT: How SEO Poisoning and GitHub Facades Target Enterprise Admins
In the intricate landscape of cybersecurity, threat actors continuously evolve their tactics to compromise high-value targets. A particularly insidious campaign dubbed “EtherRAT” has emerged, meticulously designed to ensnare enterprise administrators, DevOps engineers, and security analysts. This sophisticated operation foregoes traditional mass phishing, instead leveraging a highly targeted approach that weaponizes everyday search habits and reputable platforms like GitHub.
The EtherRAT campaign represents a calculated shift in attack vectors, focusing on precision over volume. By understanding and exploiting the digital behaviors of IT professionals, attackers are directly injecting malicious software into environments where it can inflict maximum damage. This blog post delves into the mechanics of this cunning campaign, exploring its delivery chain, identifying its targets, and providing actionable remediation strategies.
The Devious Delivery Chain: SEO Poisoning to Malicious Payloads
The ingenuity of the EtherRAT campaign lies in its multi-stage delivery chain. It begins with a technique known as SEO poisoning, where threat actors manipulate search engine results to promote malicious links. When a high-privilege IT professional searches for common tools, documentation, or solutions, they are inadvertently directed to seemingly legitimate platforms that are in fact controlled by the attackers.
- Initial Lure: Attackers create fake articles, documentation, or project pages optimized with keywords frequently searched by their targets.
- GitHub Facades: A critical component of this campaign involves the use of GitHub facades. Attackers host malicious repositories or fork legitimate projects, injecting their payloads while maintaining a veneer of authenticity. This leverages GitHub’s reputation as a trusted source for code and tools.
- Malware Dropper: Once a target interacts with these compromised GitHub assets, they are often prompted to download what appears to be a legitimate utility or update. This download, however, is a sophisticated dropper designed to install EtherRAT.
This method circumvents many traditional security measures, as the initial interaction appears benign and originates from a trusted online resource.
Who are the Targets? High-Value IT Professionals
The EtherRAT campaign is not indiscriminate; it specifically targets individuals with elevated network privileges and access to critical infrastructure. The primary victims include:
- Enterprise Administrators: Individuals responsible for managing and maintaining an organization’s IT infrastructure, granting them broad system access.
- DevOps Engineers: Professionals who bridge development and operations, often with access to source code, deployment pipelines, and production environments.
- Security Analysts: Ironically, security analysts are also targeted, likely to gain insights into an organization’s defense mechanisms or to deploy backdoors for future exploitation.
Compromising any of these roles can provide attackers with deep access into an organization, enabling data exfiltration, system disruption, or the establishment of persistent backdoors.
EtherRAT’s Capabilities: A Remote Access Trojan
The EtherRAT itself is a potent Remote Access Trojan (RAT). Once installed, it grants attackers extensive control over the compromised system. While specific capabilities can vary, common RAT functionalities include:
- Remote Command Execution: Running arbitrary commands on the victim’s machine.
- Data Exfiltration: Stealing sensitive files, credentials, and intellectual property.
- Keylogging: Recording keystrokes to capture login credentials and other confidential information.
- Screen Captures: Taking screenshots of the victim’s active desktop.
- Persistence Mechanisms: Ensuring the malware remains active even after system reboots.
- Lateral Movement: Using the compromised machine as a pivot point to access other systems within the network.
The ability to establish such deep control over high-privilege accounts poses a significant threat to an organization’s integrity and security posture.
Remediation Actions: Fortifying Defenses Against EtherRAT
Defending against sophisticated campaigns like EtherRAT requires a multi-layered approach focusing on proactive measures and incident response readiness. Here are critical remediation actions:
- Enhance Search Vigilance: Train IT staff to be extremely cautious of search results, especially those leading to unfamiliar domains or slightly altered URLs, even if they appear high in ranking. Cross-reference official documentation and project pages.
- Scrutinize GitHub Repositories: When downloading tools or code from GitHub, verify the repository’s legitimacy. Look for factors like:
- Creation date and commit history (older, active repositories are generally more trustworthy).
- Number of stars, forks, and contributors.
- Maintainer’s reputation and linked profiles.
- Absence of suspicious comments or issues.
- Implement Strong Endpoint Detection and Response (EDR): Utilize EDR solutions to monitor for anomalous process behavior, unauthorized network connections, and suspicious file executions, which can indicate RAT activity.
- Leverage Threat Intelligence: Stay updated on emerging threats and Indicators of Compromise (IoCs) related to campaigns like EtherRAT. Integrate this intelligence into your security tools.
- Principle of Least Privilege: Enforce the principle of least privilege across all user accounts, especially for administrators and engineers. Grant only the necessary permissions for their roles.
- Multi-Factor Authentication (MFA): Implement mandatory MFA for all accounts, particularly those with administrative privileges, to significantly reduce the impact of stolen credentials.
- Regular Security Awareness Training: Continuously educate employees, especially IT professionals, about social engineering tactics, SEO poisoning, and the dangers of downloading software from unverified sources.
- Network Segmentation: Isolate critical systems and administrative networks to limit lateral movement in case of a compromise.
- Application Whitelisting: Implement application whitelisting to prevent unauthorized executables from running on endpoints.
- Keep Software Updated: Regularly patch and update all operating systems, applications, and security software to address known vulnerabilities.
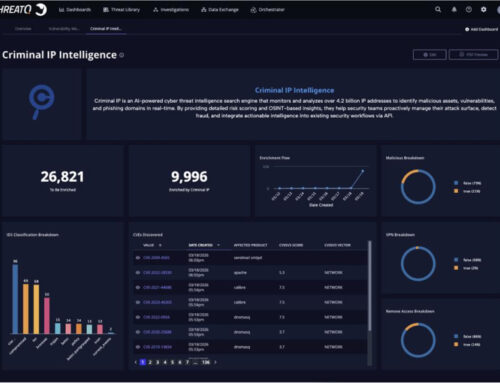
Tools for Detection and Mitigation
| Tool Name | Purpose | Link |
|---|---|---|
| Endpoint Detection and Response (EDR) Solutions | Detects and responds to suspicious activities on endpoints, including RAT deployment and command-and-control communication. | N/A (Vendor specific) |
| Network Intrusion Detection/Prevention Systems (NIDS/NIPS) | Monitors network traffic for malicious patterns, C2 communications, and data exfiltration. | N/A (Vendor specific) |
| VirusTotal | Analyzes suspicious files and URLs against a multitude of antivirus engines and malicious link scanners. | https://www.virustotal.com/ |
| YARA Rules | Creates custom rules to identify malware families by textual or binary patterns. Essential for hunting for specific EtherRAT variants. | https://virustotal.github.io/yara/ |
| OSINT Tools (e.g., Shodan, Censys) | For security teams to identify exposed infrastructure potentially related to threat actors’ C2 servers or phishing domains. | https://www.shodan.io/ https://censys.io/ |
Conclusion
The EtherRAT campaign serves as a stark reminder that cyber adversaries are constantly refining their methodologies. By leveraging SEO poisoning and masquerading behind trusted platforms like GitHub, attackers are effectively bypassing traditional security filters and targeting the very individuals tasked with safeguarding our digital infrastructure. Organizations must prioritize robust security awareness training, implement stringent endpoint and network security controls, and foster a culture of skepticism toward unsolicited or suspicious digital interactions. Vigilance and proactive defense are paramount in protecting high-privilege accounts from such sophisticated threats.