Attackers Deploy AiTM Phishing Pages to Access SharePoint, HubSpot, and Google Workspace
The landscape of cyber threats is undergoing a significant transformation. Attackers are increasingly leveraging sophisticated techniques to bypass traditional security measures, with a particular focus on exploiting trusted Software-as-a-Service (SaaS) environments. Recent intelligence highlights a concerning trend: the deployment of Adversary-in-the-Middle (AiTM) phishing pages to gain unauthorized access to critical platforms like SharePoint, HubSpot, and Google Workspace.
The Evolution of SaaS-Centric Attacks
For too long, enterprise security models have heavily relied on perimeter defenses and endpoint security. While still vital, these traditional approaches are proving insufficient against a new breed of highly agile and evasive threats. Threat actors are rapidly shifting their intrusion tradecraft, targeting the very platforms businesses depend on daily. This move toward high-speed, SaaS-centric attacks allows them to operate almost exclusively within trusted environments, effectively sidestepping many established security controls.
CORDIAL SPIDER and SNARKY SPIDER: Agendas and Targets
Since October 2023, cybersecurity researchers have been tracking two distinct, aggressive adversaries identified as CORDIAL SPIDER and SNARKY SPIDER. These groups are at the forefront of this shift, conducting intense data theft campaigns. Their modus operandi clearly demonstrates a strategic pivot away from directly compromising infrastructure and toward exploiting the perceived trustworthiness of SaaS applications. Their targets include, but are not limited to,:
- SharePoint: A cornerstone for document management and collaboration within many organizations. Unauthorized access here can lead to sensitive document exfiltration and intellectual property theft.
- HubSpot: A critical platform for sales, marketing, and customer service. Compromise can expose customer data, marketing strategies, and lead to direct financial impact.
- Google Workspace (formerly G Suite): Encompassing Gmail, Drive, Docs, and more, this suite holds a wealth of organizational communications, files, and personal identifiable information (PII).
The common thread among these targets is their central role in business operations and their inherent trust within organizations. By compromising these platforms, attackers gain a beachhead within an organization’s digital ecosystem, often with significantly elevated privileges and access to valuable data.
Understanding AiTM Phishing
AiTM phishing is a particularly insidious form of attack. Unlike traditional phishing that merely attempts to steal credentials, AiTM techniques sit between a user and a legitimate service. The attacker acts as a proxy, intercepting and relaying traffic in real-time. This allows them to:
- Harvest Session Cookies: Even if a user employs multi-factor authentication (MFA), an AiTM attack can intercept the session cookie after successful authentication, allowing the attacker to bypass MFA entirely.
- Bypass MFA: This is a critical distinction. Many organizations rely on MFA as their primary defense against credential theft. AiTM phishing renders many common MFA implementations ineffective by stealing the authenticated session.
- Maintain Persistent Access: Once a session cookie is stolen, attackers can often maintain access for extended periods, even after the legitimate user logs out or changes their password, until the session expires or is explicitly revoked.
The deployment of AiTM phishing pages designed to mimic SharePoint, HubSpot, and Google Workspace login portals represents a highly effective and targeted approach to gaining unauthorized access and exfiltrating data.
Remediation Actions and Mitigations
Combating these advanced threats requires a multi-layered security strategy that goes beyond traditional endpoint and perimeter defenses. Organizations must prioritize the security of their SaaS environments. Here are crucial remediation actions:
- Implement FIDO2/WebAuthn for MFA: While SMS, TOTP, and push notification MFA can be vulnerable to AiTM, hardware-backed keys utilizing FIDO2/WebAuthn protocols offer strong resistance as they are cryptographically bound to specific origins and cannot be phished in the same way. Consider solutions like YubiKeys or integrated hardware security modules. There isn’t a specific CVE for AiTM phishing itself, but rather it’s an attack technique that exploits user behavior and session management.
- Enhance User Education: Conduct regular, rigorous training on the dangers of phishing, especially AiTM variants. Teach users to scrutinize URLs carefully, look for certificate anomalies, and report suspicious activity immediately.
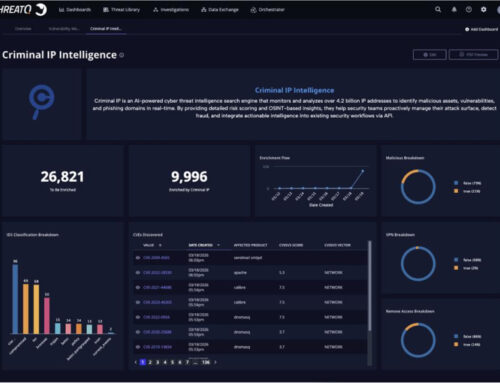
- Monitor SaaS Application Logs: Implement robust logging and monitoring within SharePoint, HubSpot, and Google Workspace. Look for unusual login patterns, access from anomalous IP addresses, large data downloads, or changes to security settings.
- Conditional Access Policies: Leverage conditional access rules within your identity provider (e.g., Azure AD Conditional Access, Google Context-Aware Access) to restrict access based on device health, location, IP range, and application sensitivity.
- Session Lifecycle Management: Enforce shorter session timeouts for sensitive applications, and implement mechanisms for automatically revoking sessions if suspicious activity is detected.
- Endpoint Detection and Response (EDR) / Extended Detection and Response (XDR): While AiTM bypasses some endpoint defenses, advanced EDR/XDR solutions can still detect post-compromise activities on the endpoint or in the cloud environment that result from the stolen access.
- Implement a Secure Web Gateway (SWG) and Cloud Access Security Broker (CASB): These tools can help detect and block access to known malicious phishing sites, enforce data loss prevention (DLP) policies, and monitor user activity within SaaS applications.
The Path Forward
The emergence of adversaries like CORDIAL SPIDER and SNARKY SPIDER underscores a critical shift in the cyber threat landscape. Traditional security paradigms are inadequate against sophisticated, SaaS-centric attacks that leverage AiTM phishing to bypass common MFA mechanisms. Organizations must proactively adapt their security strategies, focusing on robust identity and access management, enhanced monitoring of cloud environments, and advanced forms of multi-factor authentication to protect their valuable data within SharePoint, HubSpot, Google Workspace, and other critical SaaS platforms.