Multiple Exim Mail Server Vulnerabilities Leads to Crash with Malicious DNS data
Urgent Patch Alert: Multiple Exim Mail Server Vulnerabilities Demand Immediate Action
The digital infrastructure relies heavily on mail servers, acting as the backbone for countless communications. When these critical components face security vulnerabilities, the implications can be severe, ranging from service disruptions to data breaches. Recently, the Exim development team released a crucial update, version 4.99.2, addressing four newly discovered security flaws that could significantly impact unpatched systems. Given Exim’s widespread adoption as a message transfer agent (MTA) across the internet, system administrators must prioritize understanding these vulnerabilities and applying the necessary patches without delay.
Understanding the Threat: What Are These Exim Vulnerabilities?
The identified vulnerabilities in Exim’s mail server software represent a serious concern for any organization leveraging this MTA. These flaws, if exploited, could allow attackers to execute various malicious actions, including denial-of-service (DoS) attacks leading to server crashes, memory corruption, and the unauthorized leakage of sensitive information. The specific nature of these vulnerabilities highlights critical weaknesses that could be leveraged through crafted DNS responses.
Let’s delve into the specific CVEs addressed in Exim 4.99.2:
- CVE-2023-42115: DNS-based Server Crash (DoS): This vulnerability pertains to a flaw in how Exim processes DNS responses. A specially crafted DNS response, potentially from a malicious DNS server or a man-in-the-middle attack, could trigger a server crash, leading to a denial-of-service condition for the mail server.
- CVE-2023-42116: Memory Corruption via Bogus DNS Record: Similar to CVE-2023-42115, this vulnerability also involves DNS processing. An attacker could exploit this by providing a bogus DNS record that leads to memory corruption within the Exim process. Memory corruption could result in crashes, unpredictable behavior, or potentially pave the way for more sophisticated attacks like arbitrary code execution.
- CVE-2023-42117: Information Leakage with DNSSEC Records: This flaw specifically targets Exim’s handling of DNSSEC (Domain Name System Security Extensions) records. Attackers could exploit a weakness in this process to potentially leak sensitive information stored or processed by the Exim server. The exact nature of the leaked information would depend on the server’s configuration and the specifics of the exploit.
- CVE-2023-42118: DNS-based Information Disclosure: Another vulnerability tied to DNS processing, this issue could enable attackers to extract information from the Exim server. Unlike CVE-2023-42117 which focuses on DNSSEC, this vulnerability might be exploitable through more general DNS query manipulation.
The Impact: Why Prompt Remediation is Critical
The collective impact of these vulnerabilities underscores the urgent need for Exim administrators to upgrade. A mail server crash can disrupt all email communications, leading to significant operational downtime and potential financial losses. Memory corruption can introduce instability, security bypasses, or even remote code execution possibilities, allowing attackers to gain control of the server. Information leakage can expose confidential data, user credentials, or system configurations, leading to further attacks or regulatory compliance violations.
Given Exim’s prevalence, especially within smaller to medium-sized enterprises and hosting providers, the attack surface for these vulnerabilities is substantial. An unpatched Exim instance represents a significant risk to an organization’s email infrastructure and overall cybersecurity posture.
Remediation Actions: Securing Your Exim Mail Server
The primary and most effective remediation action is to upgrade your Exim mail server to version 4.99.2 or later immediately. The Exim development team has specifically released this version to address these critical flaws.
- Upgrade to Exim 4.99.2: Download the latest stable release from the official Exim website or through your operating system’s package manager if the update is available. Follow the upgrade instructions meticulously to ensure a smooth transition and proper application of the patches.
Command examples for common Linux distributions (always verify with official documentation for your specific setup):
For Debian/Ubuntu based systems:
sudo apt updatesudo apt upgrade exim4For RHEL/CentOS based systems (if Exim is installed via YUM/DNF):
sudo dnf update eximOr for direct source compilation, refer to the official Exim documentation for detailed steps.
- Monitor Exim Logs: Regularly review your Exim mail logs for any unusual activity, error messages, or patterns that might indicate attempted exploitation. Pay particular attention to DNS query failures or unusual connection attempts.
- Implement Strong DNS Security: Ensure your mail server is configured to use trusted and secure DNS resolvers. Consider implementing DNSSEC verification on your resolver to protect against DNS spoofing attacks, though this alone does not fully mitigate the Exim vulnerabilities without the patch.
- Network Segmentation and Firewall Rules: Implement strict firewall rules to limit inbound and outbound traffic to only essential ports and services. Segment your network to isolate the mail server from other critical infrastructure components, reducing the blast radius of a potential compromise.
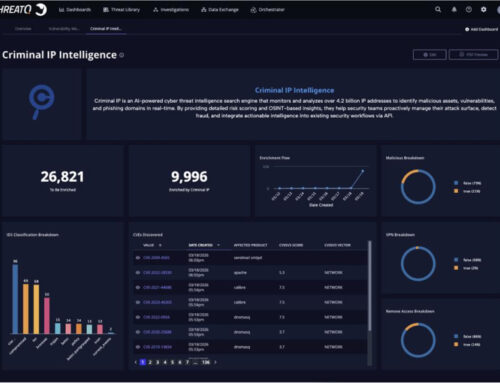
Tools for Detection and Mitigation
While upgrading is the primary defense, various tools can aid in monitoring and assessing your mail server’s security posture.
| Tool Name | Purpose | Link |
|---|---|---|
| Exim Logs | Detecting suspicious activity, errors, and potential exploit attempts. | N/A (Built-in to Exim) |
| Nessus/OpenVAS | Vulnerability scanning for known vulnerabilities, including outdated Exim versions. | Nessus / OpenVAS |
| wireshark | Network protocol analyzer for deep inspection of DNS traffic. | Wireshark |
| Security Information and Event Management (SIEM) | Centralized logging and real-time analysis of security events across your infrastructure. | Various commercial and open-source options |
Conclusion: Act Decisively to Protect Your Email Infrastructure
The discovery of multiple vulnerabilities in Exim mail server software, capable of causing crashes, memory corruption, and information leakage through malicious DNS data, presents a significant operational risk. With Exim’s critical role in internet communications, immediate action from system administrators is imperative. The release of Exim version 4.99.2 directly addresses these issues, making the upgrade the most crucial step in safeguarding your email infrastructure. Proactive patching, coupled with vigilance through log monitoring and robust network security practices, will protect against potential exploitation and ensure the continued integrity and availability of your mail services.